第十一章 三头同盟时代的战争
布伦迪西翁的和约已经达成,安东尼也迎娶了奥克塔维娅。现在,三头同盟可以继续为士兵们分配土地,并且运用手中的权力来提升名望、壮大势力了。东方正在召唤着安东尼。他带着新婚妻子奥克塔维娅去了雅典,然后开始准备大举东征帕提亚人。安东尼给自己定下的目标是为公元前53年战败被杀的克拉苏报仇,同时完成尤里乌斯·恺撒生前的东征计划。而此时的屋大维也有紧迫的事情要处理。首先,他需要完成分配土地的承诺。其次,伟大的庞培之子塞克斯图斯·庞培仍然是一个问题。虽然三头同盟已经和塞克斯图斯·庞培达成了和解,但他仍然拥兵自重,在西西里岛割据一方,这种和平脆弱无比。
剿灭海盗之王
差不多是在他的父亲被恺撒击败以后,塞克斯图斯·庞培开始了他的军事生涯。此时,他盘踞在西西里岛,并且由此建立了海上霸权,控制着西地中海的重要航道。以前,庞培为安东尼提供了海军支援,还协助安东尼的家人完成了撤离,让安东尼欠下了人情债。于是,安东尼帮助庞培与三头同盟签订了和约,但李必达因此吃了一些亏。[280]这份和约还准许了那些被流放的贵族返回罗马。尽管和解还未达成,但至少这些已然失败的贵族得以摆脱流放生活。
屋大维和庞培之间的和平打从一开始就不可能持续多久。他们的关系本就很紧张,同时,没有什么因素能够促使他们化敌为友。屋大维控制了意大利的丰富资源,这就意味着从长远来看,他们的竞争必定会以屋大维的胜利告终。庞培及其追随者应该也能看清这一点。此外,屋大维肯定一方面知道夺取西西里的田地能够带来多么巨大的好处,另一方面也深知庞培的舰队不容小觑。维持一段时间的和平既可以让屋大维有机会来发展自己的海军,也可以削弱庞培的势力,因为舰队的建造和维持都需要耗费大量的人力、物力。随着时间的流逝,庞培的资源会越来越紧张,其追随者也会相应地减少。
屋大维提出的宣战理由是庞培的海盗行径。不过,最终战争的到来还是因为庞培麾下的一名比较重要的舰队统帅米诺多洛斯(Menodoros)投靠了屋大维。现在,屋大维有了一支足以与庞培一战的舰队。公元前38年,战争爆发了。第一场大规模战斗发生于意大利南部库马伊(Cumae)附近的海域,屋大维的舰队告负。海战本身其实并没有造成特别大的损伤,但是屋大维这边的舰队统帅经验相对较少,遇上了风暴,许多船只都是在这个时候被毁的。屋大维就这样失去了在海上与庞培对抗的能力,而庞培的制海权令其可以自由地劫掠意大利的沿海地区,这让接下来一年时间里的屋大维深感无奈。[281]
到了公元前36年,屋大维再次有了可堪一用的舰队。安东尼造访了意大利,给屋大维带来了一百二十艘船只。而屋大维需要相应地给他提供两万名士兵,支援他对抗东方的帕提亚人。李必达则得到了指示,让他自7月1日开始从北非发起协同攻击。这一次,屋大维的部队又遇上了糟糕的天气,李必达的攻势也不顺利。[282]但是,庞培的处境还是不可避免地恶化了。李必达的十二个军团最终成功地登陆了西西里,并且围住了位于岛上西端的城市利吕拜翁[Lilybaeum,今天的马尔萨拉(Marsala)]。现在,庞培必须在西西里岛上直面一支实力强劲的军队。而且,屋大维的部队也即将到来。
阿格里帕是屋大维的密友。从屋大维踏入政坛开始,他就一直站在屋大维这边。在佩鲁西亚战争期间,阿格里帕也有出众的表现。此时,他已经在意大利本土西面的埃奥利群岛(Aeolian Islands)上建立了前沿基地。接着,他率军大致朝着正南方航行,在西西里岛东北部的缪莱(Mylae)附近和庞培的舰队相遇。此次交手是屋大维的部队第一次在海战中占上风。虽然这场战斗本身并没有产生重大的战果,但阿格里帕的胜利让他得以登陆西西里,把第二支三头同盟的军队带到了岛上。而且,就在庞培专注于北部的战斗之时,屋大维乘机开始从东部的陶洛米尼翁[Tauromenium,今天的陶尔米纳(Taormina)]登陆西西里。
然而,屋大维所部的登陆行动受到了阻碍。庞培的海陆军队撤离缪莱以后沿着海岸经过梅萨纳(Messana)[今天的墨西拿(Messina)],往南遇上了正在登陆的屋大维。他们早已料到屋大维会尝试登陆。既然已经无法阻止阿格里帕的行动,那么他们就果断地放弃,转而试图出其不意地进攻屋大维。于是,屋大维麾下人数较少的这支部队被打乱了,陷入了非常危险的境地。不过,他最后还是稳住了阵脚。其原因大概有两个:首先,夜幕已经降临;其次,庞培的部队消耗了过多的体力。当天夜里,屋大维抓紧时间巩固了营地的防御工事。第二天,双方开始对峙。[283]
不过,屋大维的这个营地毕竟独木难支。所以,他召集海军登上了小型船只,试图突破庞培的阻拦,转移到别处去。虽然庞培击败了屋大维的舰队,但屋大维本人成功地逃到了意大利的海岸上。如果庞培能够在这场战斗里抓住屋大维,那么战争的走向也许会发生剧变。不过,最终找到屋大维的是一些一直在山丘上围观战斗的当地居民。他们帮助了屋大维,令其得以顺利地与部下会合,并且开始组织后援部队。
与此同时,屋大维留在陶洛米尼翁的军团受到了不小的压力。营地的位置不是很理想。而且,驻扎的部队有一万九千人,但他们的补给却不多,尤其缺少饮用水。负责指挥的将领是科尔尼非奇乌斯。他试图与对方展开战斗,但庞培等人深知己方的优势,拒绝出战。因此,科尔尼非奇乌斯只好率领全军出去寻找饮用水和援军。[284]他顶着敌方的骚扰,向西西里岛的内部挺进。他们途中需要经过埃特纳火山(Etna)附近的熔岩平原,这是一块崎岖、干燥的荒芜之地,当地居民通常只会在夜里来此。对于军队而言,在这种地方行进是非常困难的。而且,庞培的人还在不停地干扰科尔尼非奇乌斯的行动。他们一面阻挡在某些路线上,一面派出部队来进行骚扰。庞培的骑兵熟练地保持着距离投射火力,致使许多人负伤,进而拖慢行军的速度。路上的每一个庞培派据点都阻碍着科尔尼非奇乌斯的行军,让士兵们越发渴望水源,同时还增加了伤员的数量。就这样,在这仲夏之时,科尔尼非奇乌斯等人既没有据点也没有充足的饮用水,只能步履维艰地在西西里岛的熔岩平原上缓慢前行。这支部队可以说是朝不保夕。
终于,他们发现了一处泉水,但是旁边还有不少的庞培派军队。如果他们无法快速地突破敌方的防线获得水源,那么这支部队就很可能会因疲劳和干渴而崩溃。就在他们前进的时候,又有一支相向而来的军队出现在他们的视野里。但是,由于双方距离过远,他们无法分清敌我。如果这是庞培方的援军,那么科尔尼非奇乌斯等人就彻底失去了得救的希望。不过,位于泉水处的庞培方部队距离这支军队较近,他们应该已经通过斥候探得了情报。这支靠近的部队属于阿格里帕,他正在寻找科尔尼非奇乌斯的下落。于是,庞培的部队离开了,科尔尼非奇乌斯等人得救了。[285]
屋大维带来的军团和阿格里帕会师以后,庞培的处境就很艰难了。三头同盟的强大陆军业已在西西里岛上展开了行动。庞培的最大优势原本是他的舰队,但现在,他已经无法完全掌控海洋。当然了,他还可以守住一些城镇,但已然无力阻止敌方自由行动。李必达正在逐步地控制西西里岛的西部地区,阿格里帕和屋大维的部队则正在东部虎视眈眈。庞培现在的最佳策略就是寻求海上决战。如果他能摧毁敌方的海军,那么就可以进一步切断敌方和意大利的联系,给敌方的补给造成巨大的压力。公元前36年9月3日,庞培的舰队出航了。对此,屋大维和阿格里帕卓有自信地接受了挑战,双方舰队会战于缪莱以西的瑙洛库斯[Naulochus,大概在今天的斯帕达福拉(Spadafora)]。
罗马人的海战有一套标准的模式。在古老的三层划桨战船时代,海战的目标是用己方的船只迅猛地撞击对手,以期击毁敌方船只。相比之下,罗马人的海战更为稳健,也更加缓慢。他们更看重近距离的缠斗和接舷战。[286]因此,罗马人倾向于建造特别高大的船只。船上还会有高高的塔楼以供士兵们在塔楼上向对手投射火力。同时,他们还会准备厚重的防护板,用以阻挡敌方的火力。在这种设计思路下建造起来的船只都是笨重的庞然大物,载着大量的士兵和装备。这些宏伟的海上堡垒还会整齐地排列为一条线,以免让对手抓住侧翼的破绽甚至找到落单的船只。在这个阶段,船员的目标就是让友方船只尽可能紧密地靠在一起,不给对手插队的机会,但同时又必须保持足够的距离,以免不同船只的桨碰撞在一起。战斗打响以后,双方的船只就会开始缠斗,互相投射火力。撞击船会反复地进出,以期逃离敌方的攻击或者发起下一轮冲锋,从而保持己方的阵形或者摧毁敌方的阵形。船上的士兵必须在瞄准对手的同时闪躲敌方的火力。他们还会注意抓钩,避免让自己的船被旁边下沉的船只拖下水。他们也会挑选看起来比较弱的对手,避开强敌。等到合适的时机来临,他们就会纵身扑向对手,开启接舷战。总而言之,海战是漫长的消耗战。
在瑙洛库斯海战当中,阿格里帕运用了一种新设计的抓手。随着双方船只的靠近,他们把这种抓手伸到了庞培的舰队的甲板上,用来拨走敌方士兵或者毁坏甲板上的防御工事或者火力投射装置的引擎。也许,这种武器的主要效果其实只是引发敌人的骚乱。因为这是一种前所未见的新武器,庞培的士兵们都没有准备长杆子来进行反制。三头同盟的舰队大概由此而获得了些许的优势,并且将优势逐步扩大为胜利。
此时,庞培和他的陆军正在营地里观看战局。渐渐地,他们的舰队难以支撑下去了。在这一天的战事结束的时候,三头同盟的海军唱起了胜利的颂歌,屋大维的军团也在岸上附和。庞培派陷入了绝望。庞培本人当即离开,回到了梅萨纳的基地。据说,他在基地里一言不发,没有下达任何命令。他的军团看不到未来,选择了投降。[287]
庞培本人还有一些挣扎的余地,但他已经无力回天了。他一边召集部队,一边逃往东方,然后请求安东尼看在他之前曾经为其效劳的分儿上出手相助。与此同时,庞培还派出使者前往帕提亚,想要再寻一条后路。安东尼接见了庞培的信使,承诺只要他怀着善意前来就会认真地考虑他的请求。然而,此时的庞培毕竟已经丧失了谈判的资本,安东尼没有理由与他交涉。所以,当庞培落脚于小亚细亚以后,安东尼就开始调遣海陆部队过来包围庞培。而庞培派往帕提亚的使者也被拦截了下来,他只好尝试着作战。他取得了一些战果,但他已经深陷重围。最终,他烧毁了剩下的舰船,准备沿陆路逃往帕提亚。他的势力彻底失败了。他的部下们也都明白了这一点,纷纷离他而去。最后,庞培被俘,并且在不久以后遭到了处决。[288]
西西里局势的走向有些奇怪。庞培的残部并没有投靠屋大维,反而投奔了李必达,令其顺势宣布自己才是西西里的主人,由此提出了提高自身在三头同盟当中的地位的要求。于是,他们二人的部队与其展开了对峙。然而,此时的广大士兵仍然像公元前40年那样不愿自相残杀。至于庞培的军团,他们都是败军,早已没了士气,当然也不会愿意为了李必达而战死沙场。屋大维带人来到李必达的营地旁边,宣布对方士兵主动来降可以免罪。然后,双方爆发了小规模的打斗。屋大维的一位朋友在打斗中受了伤,于是,他匆忙下令撤退。不过,李必达的一部分士兵已经听到了屋大维的话,他们的战意越来越少。接着,李必达的部下开始三三两两地跑到屋大维那边去。此情此景,李必达非常熟悉,当初面对安东尼的时候他就经历过这一幕。于是,他换下了戎装,亲自去会见屋大维。他鞠躬以示谦卑,请求屋大维饶过自己的性命。屋大维则转身离去,让部下去欢迎李必达加入己方的阵营。就和当年一样,他的对手展示了自己的仁慈,留下了他的性命。屋大维或许想要以此向所有的恺撒派人士表明,无论发生了什么事,往日的交情始终是存在的。同时,屋大维的举动还可以说明他根本不认为李必达会威胁到自己。之后,李必达被剥夺了军权,只保住了最高祭司这个最重要的神职。归根结底,李必达的那点政治影响力实在是不值得让人动手杀他。[289]
不过,战争还没有完全结束,屋大维就遇到了兵变。士兵们要求得到腓立比之战以后那种规格的奖赏,屋大维不太情愿,并且试着坚持己见。这种态度激怒了与会的士兵,他们开始反叛。一个名叫奥非里乌斯Ofellius的军官成了他们的领导者,屋大维被迫撤回了自己的军帐。第二天,他较有信心地回到了士兵们的面前,表示愿意做出一些让步,并且承诺要带领大家前去讨伐伊利里亚人(Illyrians)。然而,奥非里乌斯失踪了。据说,屋大维的人在夜里悄悄地杀死了他。不管怎样,士兵们意识到自己的代表不见了。于是,屋大维在做出让步的同时加以威胁,他宣布不服从者再也没有参军的资格。屋大维这是在强调自己的权威,逼迫士兵们做出选择—要么永远地离开三头同盟的关系网络,再也没有分得奖赏的机会;要么服从这张关系网络的规矩。最终,屋大维恢复了自己的权威。或许,他确实依赖于这些军人,但这些军人无疑也依赖于屋大维。[290]
这是屋大维的光辉时刻。他成功地取得了对西西里和阿非利加的控制权,保证了罗马城能够拥有稳定的粮食供应。他不仅为三头同盟击败了割据一方的庞培,还能凭着在粮食供应方面立下的功绩赢得广大平民的感激。贵族的观点或许有所不同。一些人应该是刚刚从庞培那里返回,还有一些也许仍然忠诚于布鲁图斯和卡西乌斯的理念。但是,屋大维这次取得的胜利再一次说明了这些人根本无关紧要。
屋大维毫不客气地利用了这份战功。平民会议表决让屋大维有权坐在保民官的座位上(很可能是永久性的),同时也给了他等同于保民官的神圣不可侵犯sacrosanctitas的权利。从此,伤害屋大维就是在犯罪。当然,这个权利只是一份荣誉。真正的刺客肯定不会在意。不过,值得注意的是,这两项长期有效的特权都把屋大维和保民官联系在了一起。[291]由此,屋大维将自己塑造为罗马人民的保护者,宣布自己对人民负有义务,同时强调了人民也依赖于他。
屋大维还在罗马城的正中心建造了一座独特的纪念柱,用以长期纪念这次的胜利,并且警告那些妄图与自己作对之人。按照罗马的古老传统,海战胜利的纪念物就是敌舰的船首和撞击锤。屋大维命人截下了敌船的撞击锤,然后将其添加到罗马城广场中心新建的纪念柱上。这座建筑物(未能保存至今)占据了罗马城内最为重要的政治场所,吸引着无数人的目光。纪念柱的顶端还有屋大维的金色雕像。
一般来说,只有神灵才会享有贵金属制成的雕像,屋大维这是在尝试为自己塑造合适的公共形象。他是手握重权的人民守护者,位居罗马新秩序的中心,享受着军人的拥戴和平民的感激。现在,他足以比肩神明。
唯一有可能挑战其地位之人远在海外—位于亚历山大的安东尼和克莱奥帕特拉。不过,在屋大维庆祝胜利之时,三头同盟的制度看起来前所未有地强大而稳固。毕竟,真正终结了庞培的是安东尼,他之前还曾给屋大维提供作战所需的舰船。而且,无论他和克莱奥帕特拉之间到底有着怎样的关系,安东尼仍然是奥克塔维娅的丈夫、屋大维的姐夫。当然,安东尼和屋大维应该都不怎么想念李必达与他们分享权力的日子。战后,屋大维归还了安东尼借给他的舰队。其中的一部分船只已经毁于战火,屋大维对此做了相应的补偿。[292]此外,安东尼在这场战争中做出的贡献也得到了认可:罗马城中举办了庆祝安东尼杀死庞培的赛事;罗马城广场的演讲台附近立起了安东尼乘坐战车的雕像;和谐女神庙(Temple of Concord)里也有了安东尼的雕塑;新铸的货币上同时描绘着屋大维和安东尼两人的头像(如图3);安东尼本人和他的妻子(奥克塔维娅)、儿女都获得了在神庙里举办宴会的权利。[293]总之,屋大维认可了安东尼的重要地位,他们二人团结一致。心存怀疑的元老都不妨去看一看广场上的安东尼像,深刻地感受一下屋大维和安东尼之间互相依赖、合则两利的关系。此时此刻,他们二人想要做的不是自相残杀,而是自古以来罗马人最为擅长的一件事情:开疆拓土。
安东尼的东方霸业
自公元前53年罗马人在卡莱遭遇大败[指卡莱战役。在这次战争中,罗马执政官马尔库斯·克拉苏被杀,七个罗马军团全军覆没,罗马军队的军旗被夺。这是罗马与帕提亚帝国之间的一场重要战役,也是罗马的一次重大失败]以来,帕提亚人就成了罗马人的心腹大患。当时被击败的罗马远征军由七个军团和相应的辅助部队组成,其统帅是马尔库斯·克拉苏。他们被帕提亚人找到了行踪,然后在对方的骑兵手下吃了大亏。罗马的重步兵难以应对帕提亚的重甲骑兵和轻装弓骑兵。一般说来,罗马人在遇到这种失败的时候只会迎难而上,继续投入兵力。然而,当时西部的政治局面动荡不断,令罗马人暂时无法把资源调集至东方。后来,公元前44年,恺撒在大致平定西部乱局以后就开始准备复仇之战。不过,他在奔赴东方之前就遇刺身亡了。时至今日,罗马的国内秩序终于再度恢复,帕提亚当然就成了安东尼用以建功立业的对象。
在腓立比之战结束以后,安东尼就致力于平定东部的领土。除了埃及以外,东部的地方势力都曾经与布鲁图斯和卡西乌斯为伍。在这个过程当中,安东尼和克莱奥帕特拉的政治联盟以及他们二人之间的私人关系发挥了不小的作用。克莱奥帕特拉的对手遭到了清洗。安东尼先从希腊各地收取了资金,然后到埃及的亚历山大建立了自己的政治基地。[294]
就在这个时候,帕提亚人出兵了。也许,他们意识到了罗马人在政局稳定以后就会发动入侵。帕提亚军队的统帅是王子帕科鲁斯(Pacorus)和流亡至帕提亚的罗马人拉比恩努斯,他当初是恺撒在高卢的得力助手,但在内战期间投靠了庞培。后来他成为布鲁图斯和卡西乌斯派往帕提亚的使者。当腓立比之战的结果传到帕提亚之时,他选择了留在帕提亚。在民族主义兴起之前,这种改换门庭的行径虽然并不多见,但还不是什么难以设想的事情。
在拉比恩努斯的劝说下,帕提亚人决定主动出击。东部的罗马驻军大部分还是布鲁图斯和卡西乌斯留下的,他们不会坚定地效忠于安东尼,这让帕提亚军队有了可乘之机。他们在叙利亚地区长驱直入,阿帕梅亚(Apamea)和安条克(Antioch)相继沦陷。然后,拉比恩努斯西进至奇里乞亚,帕科鲁斯则南下犹地亚,控制了耶路撒冷。就这样,帕提亚人迅速地占领了黎凡特地区(Levant)的大块罗马领土。[295]然而,安东尼还没来得及发起反击就被迫带兵返回了意大利。
公元前39年,安东尼得以抽身回来处理帕提亚人的问题。他派出了共同经历过穆提纳战役的老朋友文提迪乌斯,命他率领一支大军先行。安东尼自己则途经希腊,落后一些。对此,我们的各位史家秉持一贯的态度,将其归因于安东尼的性格缺陷—懈怠。然而,安东尼的作战计划还是一如既往地取得了成功。
拉比恩努斯在和文提迪乌斯交上手之前都没有得知对方靠近的消息。随他进入小亚细亚的只有他自己的罗马士兵,而这些部队是无法抵挡文提迪乌斯的。安东尼或许就是知道了这个情报才做出了这样的安排,拉比恩努斯只好向叙利亚撤退。但是文提迪乌斯留下了重装部队,只带着骑兵和轻装部队快速行军,拦下了拉比恩努斯。接着,双方都开始等待援军抵达。
帕提亚的骑兵和罗马的步兵同时到达了。文提迪乌斯的军营在地势较高处。拉比恩努斯和帕提亚人前来叫阵,但文提迪乌斯并不想让己方部队暴露在帕提亚骑兵面前。[296]为了吸引对方出战,帕提亚人越来越靠近罗马军队的营地。最终,他们朝着文提迪乌斯设置在上坡的工事发起了冲锋。于是,文提迪乌斯下令出击。遭受突袭的帕提亚骑兵连忙转身逃跑,以求尽快远离罗马步兵。在一般情况下,这其实是正确的做法。但这一回,帕提亚骑兵直接撞上了文提迪乌斯安排好的骑兵。接着,罗马步兵也赶到了,帕提亚人被打得溃不成军。拉比恩努斯带着残部向西边转移,但无济于事。为了逃跑,他把部队化整为零,试图由此避开文提迪乌斯的部队。然而,还是有许多人未能逃出生天。拉比恩努斯本人一度乔装成平民,藏匿于奇里乞亚。但这种花招并不能拯救他,最后,拉比恩努斯被找了出来,遭到处决。[297]
帕提亚人没有做好防御的准备,他们动员起来的部队已经被击溃,还有大量的骑兵战死沙场。现在,他们既不能与罗马人展开野战,也没有足够的驻军来打守城战。黎凡特地区的诸位国王既然可以接受帕提亚人占领他们的土地,那么就同样可以接受罗马人的再次进驻。一旦罗马军队进入了叙利亚,帕科鲁斯就几乎只能选择撤退了。[298]
在安东尼收复失地的过程中遇害的最著名的人物是统治着犹地亚的国王安提柯(Antigonus)。他曾经与帕提亚人为伍,后来又试图抵御罗马人的入侵。在罗马人围攻拿下耶路撒冷以后,安提柯被绑在了十字架上遭受鞭打。他或是立刻或是没过多久就被处死了。在他以后统治犹地亚的是出身于其他家族的希律,也被称为大希律王(Herod theGreat)。犹地亚社会的传统精英阶层是神职人员,在这些人眼里,希律算是一个异类。但是,对罗马人来说,希律几乎是一个完美的附庸国王。他有从军的履历,不惜动用严酷的手段来维持公共秩序,但他的地位归根结底来自罗马人的扶植。[299]
公元前38年,帕提亚人主动进攻了。文提迪乌斯如法炮制,再次引得帕提亚重装骑兵靠近了他的据点,然后先用火力扰乱敌方的军阵,接着出动部队进攻。这一次,帕科鲁斯被杀死了。帕提亚骑兵奋勇作战,夺回了他的尸体,但他们的败局已定。罗马军队成功地将其击退,文提迪乌斯又取得了一场大胜。[300]
战事暂停了,安东尼需要巩固罗马人对叙利亚的统治。同时,他还在分心关注屋大维和塞克斯图斯·庞培的战争。至于帕提亚人,他们现在不仅无力再次发动攻势,还又一次深陷于同室操戈的泥沼。大概在公元前37年,老国王奥罗迪斯(Orodes)去世了。在帕科鲁斯也已亡故的情况下,王位传到了另一位王子普拉提斯(Phraates)的手中,而这位王子还有不少的竞争对手需要解决。他杀死了科马基尼(Commagene)国王安条克[即科马基尼王国国王安条克一世(Antiochus Ⅰ)]的女儿和奥罗迪斯所生的儿子。安条克对此表示抗议。于是,他把安条克国王也给杀了。接着,至少有一部分帕提亚贵族举起了反旗,比如莫奈西斯(Monaeses)。[301]
现在,安东尼成了主动进攻的一方。他让奥皮乌斯·斯塔提阿努斯(Oppius Statianus)指挥大多数的士兵和辎重车队,自己则带着一股规模较小的部队朝着普拉斯帕(Praaspa)进发。这座城市位于今天伊朗的西北部,在当时是米底王国的一座重要城市。安东尼的计划其实是不差的,因为帕提亚人正在自相残杀,他想要趁此良机推动帕提亚帝国解体。但是,就在罗马人学习如何对抗帕提亚人及其盟友的同时,东方的诸位国王也逐渐掌握了与罗马人战斗的技巧。米底国王阿尔塔瓦斯迪斯(Artavasdes)深知一旦被罗马人围困在城里就必败无疑。所以,他在普拉斯帕留下了一些驻军,然后就主动出击。他避开了安东尼,找到了正在行军的斯塔提阿努斯,趁其不备,将其一举击溃。
安东尼的后援部队和辎重车队都被歼灭了,但他仍然拒绝撤退。接着,阿尔塔瓦斯迪斯开始骚扰安东尼的补给线。于是,安东尼尝试着在普拉斯帕附近就地收集补给,但他派出去的人手遭到了米底人的抵抗。渐渐地,安东尼的补给越来越少,他只好无奈地选择战略转移。途中,米底人趁机对其发起了攻击。安东尼带着一部分军队来到了亚美尼亚,但另有一部分人先是偏离了寻常的道路,然后就失去了方向。有一次,面对米底弓箭手的攻击,罗马步兵摆出了龟甲阵(testudo),把盾牌紧密地靠在一起,抵挡住来自所有方向的火力。米底人从未见过这种战术,他们以为自己的箭雨已经奏效,便贸然发起了冲锋,被重整阵形的罗马人打得大败。接着,罗马军队得以继续撤退。[302]
安东尼回到了埃及过冬,并且向屋大维和克莱奥帕特拉求援。屋大维做了一个不同寻常的决策—派奥克塔维娅和援军一起去安东尼处。但安东尼并不打算让两位妻子一起陪伴自己,他让奥克塔维娅回到了罗马。尽管各位史家依然有些偏颇地强调了安东尼在公元前36年的行动是比较大的失败,但身为当事人的米底国王阿尔塔瓦斯迪斯并不觉得自己有望赢得这场战争。大约在公元前35年底之前,米底人加入了罗马人的阵营。[303]第二年上半年,安东尼入侵了亚美尼亚,俘虏了亚美尼亚国王,并且击退了发起反攻的帕提亚人。[304]至此,安东尼已经赢得了战争:他驱逐了侵占叙利亚的帕提亚人,杀死了帕提亚的王位继承人帕科鲁斯,迫使米底王国依附于罗马,占领了亚美尼亚。后世的传统观点对安东尼怀有偏见,认为这场战争失败了,还以此来证明安东尼是一位沉溺于温柔乡的不称职的将军。然而,安东尼毫无疑问地取得了一连串的政治、军事胜利,将一大片广阔的土地纳入了罗马的势力范围,同时还削弱了这一地区其他政权的实力。安东尼或许的确没能实现他原先设立的远大目标,但他仍然完全有资格宣布自己已经取得了胜利。之后,他返回了亚历山大去庆祝自己建立的功业。
胜利返回亚历山大标志着安东尼在东方的霸业登上了巅峰。就在安东尼征服东方之时,屋大维也在忙着东征西讨。在塞克斯图斯·庞培死后,屋大维最先想到的是去安抚原本属于李必达的阿非利加行省。他抵达了西西里,但接着就改变了主意。达尔马提亚出现了一些问题,给了屋大维扩张领土的机会。于是,他召集了部队,准备作战。或许就是因为他自己也需要用兵,屋大维派往东方的援军数量没有完全符合安东尼的要求。[305]
公元前35年,达尔马提亚的战事开始了。罗马人早就在这个地区拥有了很强的影响力,亚得里亚海北部的制海权也掌握在他们手中。但是,越往内陆推进,他们遇到的阻力就越大。屋大维本人也在一次围城战中受了伤。不过,到了那一年的战事大体结束之时,屋大维似乎觉得战争已经结束了。[306]他离开了达尔马提亚,转而赶往高卢。据说,他想要入侵不列颠。[307]但是达尔马提亚人还没有认输,战火再次引燃。于是,屋大维就回到了达尔马提亚,再次负了伤,又带领罗马军队取得了胜利。在接下来的几十年里,这个地区仍然在不屈不挠地反抗着罗马人的统治。不管怎样,屋大维也算是取得了胜利。基本已经被驯服的元老院为他举办了凯旋仪式,表达了感谢之情。[308]
时至公元前33年,屋大维和安东尼面前都已经没有亟待解决的军事问题了。当然了,只要有心,他们肯定还能找到可以扩张势力范围的地方和相应的出军理由。然而,屋大维和安东尼的关系正在不停地恶化,其原因尚不明确。在勉强维持了十年的合作关系以后,他们自己以及他们身边的人都开始相互攻讦。这种现象的根源不是很明显。也许,他们其实未必走向决裂。此时的罗马毕竟已经大大不同,没有人像卢比孔河畔的恺撒那样骑虎难下。不过,我们也不能把问题简化成安东尼和克莱奥帕特拉的私人关系。罗马的确又一次不可避免地坠入了内战的深渊。等到尘埃落定,安东尼和屋大维的双头统治就将蜕变为奥古斯都一人执掌大权的君主制。
[280] Appian, Civil Wars , 5.71-75.
[281] Appian, Civil Wars , 5.78-92; Dio, 48.46-47.
[282] Appian, Civil Wars , 5.96-100; Dio, 49.1.
[283] Appian, Civil Wars , 5.98-110; Dio, 49.3-5.
[284] Appian, Civil Wars , 5.111-112.
[285] Appian, Civil Wars , 5.113-114; Dio, 49.6-7.
[286] 关于罗马人的战船,读者可以参考Michael Pitassi, Roman Warships(Woodbridge: Boydell and Brewer, 2011)。
[287] Appian, Civil Wars , 5.117-121; Dio, 49.9-10.
[288] Appian, Civil Wars , 5.133-144; Dio, 49.11; 49.18.
[289] Appian, Civil Wars , 5.123-126; Dio, 49.12.
[290] Appian, Civil Wars , 5.128; Dio, 49.13-14.
[291] 后来,奥古斯都以非保民官之身取得了保民官的权力,对罗马宪法做出了创新,发展出元首制。此时的这两项特权或许可以被视作元首制的先声。
[292] Dio, 49.14-15.
[293] Dio, 49.18.6-7.
[294] Dio, 48.24.
[295] Dio, 48.25-26.
[296] Dio, 48.39-40.
[297] Dio, 48.40.
[298] Dio, 48.41.
[299] Dio, 39.22.
[300] Dio, 49.19-21.
[301] Dio, 49.23.
[302] Dio, 49.27-30.
[303] Dio, 49.33.
[304] Dio, 49.39-40.
[305] Dio, 49.34.
[306] Dio, 49.35.
[307] Dio, 49.37.
[308] Dio, 49.38.
第十二章 安东尼和克莱奥帕特拉:爱情
和与爱为敌之人
罗马革命已经改变了罗马政治的本质。在公元前40年9月的布伦迪西翁,屋大维和安东尼避免了交战,让三头同盟得以稳固地统治着罗马。无论还有多少共和国的制度、机关、传统保存了下来,罗马人都已经置身于完全不同的时代,国家的最高权力现在由三头同盟来掌握。而且,安东尼和屋大维都不太可能会主动放弃这种权力。我们或许可以把布伦迪西翁和约的签订视作罗马共和国的谢幕。不过,一般说来,我们会立刻把目光转移到历史舞台上的下一个剧目—安东尼和克莱奥帕特拉之间引人入胜的故事。
后人或许会凭着后见之明认为阿克提翁海战是安东尼和屋大维之间势必发生的总清算。他们本来就不是什么亲密的好朋友,还曾经在战场上兵戎相见。阿克提翁海战就是公元前44年至公元前40年以来的种种恩怨爆发的结果,同时也是向君主制演变的一个必要环节。但是,在公元前40年,几乎没有人能够断言三头同盟必将消亡。他们恐怕也难以想到罗马的社会、经济问题最终会被奥古斯都时代的那种君主制给画上一个句号。从公元前43年至公元前32年,三头同盟的政权一共经历了佩鲁西亚战争、屋大维和塞克斯图斯·庞培之间的战争、安东尼在东方遇到的波折、屋大维后来发动的战争以及李必达的失势。这个时间跨度甚至已经超过了很多现代的政权。在此期间,屋大维和安东尼还有他们身边的其他参政者之间难免会不断地产生各种各样的摩擦。但这并没有伤及大局,没有哪一方看起来早就准备着与另一方开战。当然,双方之间肯定充满了防备之意,两位领导者有可能只是在互相虚与委蛇。但是屋大维的确为安东尼在帕提亚的战事而派出了一些援军,安东尼也给屋大维提供了对抗庞培所需的舰队。我们固然不能说三头同盟毫无问题,但是这个政权的稳定性确实也没有那么弱。所以,我们有必要探寻屋大维和安东尼最后究竟是怎样走向决裂的。
安东尼和克莱奥帕特拉的故事有着非常丰富的内容,却未免有些可疑。这大体上要归因于后人。在当代的我们和这对古代的爱侣之间隔着两千多年来积累下来的形形色色的电影、戏剧、画作、小说等等。而且,即使我们排除了这些东西的影响,恐怕也不能触及“真相”,因为就连最早的相关文本也都有着一种虚构的色彩。看来,很可能在他们二人还统治着亚历山大的时候就已经有了许多神奇的事在人们口中流传。[309]关于安东尼和克莱奥帕特拉,我们主要参考的是普鲁塔克和狄奥的文本。但普鲁塔克生活的年代距离他们二人有一百多年的时间差。也就是说,各种谣言有了一百多年的时间来产生、演变。他的《安东尼传》是后来莎士比亚编写戏剧《安东尼与克莱奥帕特拉》的根据。至于狄奥,他著述的时间比普鲁塔克还要晚一百年。此外,我们还需要注意的是,普鲁塔克编写《安东尼传》的主要目的既不是还原历史的真相,也不是探究政治形势。他的主旨是以史为鉴,用历史上的教训来提升大家的道德水平。所以,有关安东尼和克莱奥帕特拉的各种谣言其实正好有助于达成他的编写意图,贴近于历史真相的评价反而没有那么重要。
除了普鲁塔克以外,还有很多人也把安东尼和克莱奥帕特拉的故事当作道德说教的案例。因此,有大量的相关文本都把叙述的重心放在了他们二人之间的亲密关系上。换言之,人们关注的重点不是权力斗争,而是个人的道德品质。这在一定程度上是因为每个人都需要思考如何完善自我,但只有个别人才会去考虑如何治国理政。此外,安东尼和克莱奥帕特拉是可以被树立为反面典型的,而这种反面人物更能引发大家的兴趣。身处两百五十年后的史家狄奥就把各种古代文献的内容精炼为一句话:“克莱奥帕特拉的妖术让安东尼成了欲望的奴隶。”[310]
总之,安东尼和克莱奥帕特拉被塑造为爱情故事的主角,而爱情基本上与政治无关。我们通常把这种情感划入非理性的领域,同时认为政治生活必然需要理性,而且一般由男性主宰。早在莎士比亚写出相关的戏剧之前,安东尼和克莱奥帕特拉就已经是广为人知的悲剧角色了。不过,现代人一般认为这段关系的主导者是邪恶的克莱奥帕特拉,她凭着东方女子的魅力迷住了安东尼。但是在古代,人们往往认为安东尼的道德缺陷才是引发这场悲剧的关键。随着安东尼和克奥帕特拉成为痴迷于爱情的典型人物,伟大的屋大维等人自然就成了爱情的敌人。在非黑即白的思想影响下,罗马的历史就被简化为爱情对帝国、情感对理性的道德对抗史。不过,这种通俗易懂、简洁明了的对比确实让很多后人引以为然。
但是,如果审视一下安东尼的具体行动,我们会发现他似乎不是一个合格的爱情的奴隶。从公元前40年起,在绝大部分时间里他都置身于意大利、小亚细亚、叙利亚、亚美尼亚和米底。亚历山大或许确实是安东尼的过冬之所,但总体说来,这对据说沉溺于爱情的夫妻有相当长的时间分居异地。那么,我们或许不应该把接下来的这场战争归因于克莱奥帕特拉的妖术或者安东尼的欲望。此外,我们也不太能相信屋大维等人竟然在九年以后才察觉安东尼和克莱奥帕特拉之间有着异乎寻常的亲密关系。安东尼本人似乎也认为他和克莱奥帕特拉的关系不会影响到他和奥克塔维娅的婚姻。这也难怪,毕竟他的这种状态维持了将近八年都没有引发什么值得一提的政治问题。
在现代社会里,家庭私事通常与政治无关。但是在罗马人看来,这不是泾渭分明的两类事情。婚姻是政治化的。当然,性生活和婚姻不同。性生活是私事,但婚姻是公事,或者说政治关系。不过,公元1世纪的罗马人似乎越来越反对女性干政,这大概是因为尤里乌斯-克劳狄乌斯王朝[包括提比略(Tiberius)、卡里古拉(Caligula)、克劳狄(Claudius)和尼禄(Nero)]的宫廷政治给人们留下了教训。后来,这种视婚姻为公事的观念还进一步延伸到了性生活上,很多人都关心罗马皇帝的性生活对象是谁。然而,在共和国时代,我们似乎很难说真的有人会这么在意谁和谁上了床(除了当事人和他们身边的亲朋好友)。在战争来临之前,安东尼就自己和克莱奥帕特拉的关系给屋大维写了一封信。[311]他的这些文字同样反映了前文所提的论断:
你怎么了?就因为我和女王上了床吗?她是我的妻子。我不是九年以前就和她这样了吗?你难道只和德鲁茜拉(Drusilla)一个人上床吗?提尔图拉(Tertulla)、提兰提拉(Terentilla)、鲁菲拉(Rufilla)、萨尔维娅·提提森尼娅(Salvia Titisenia)或者别的什么女人,你难道没和她们上过床?在什么地方和谁一起享受欢愉有什么关系呢?
鉴于苏埃托尼乌斯引用的部分很简短,我们得审慎地考虑一个问题:屋大维对他抱怨的到底是什么?按照安东尼的说法,屋大维抱怨的是他和多个女性保持性关系。然而,从后来的史料来看,屋大维抱怨的很可能是安东尼被克莱奥帕特拉“支配”了。毕竟,这才是他的开战理由。不管怎样,安东尼都是在佯作不知。他的意思是,利用他人的性生活来发起政治攻击是前所未有的。但这本来就是罗马人的惯用手段,虽然后面的这些才是比较常见的名目:同性恋、通奸、溺爱情人或者因私生活(尤其是和地位较低的女性)而玩忽职守。
况且,克莱奥帕特拉绝非寻常女子。安东尼自己也在信件的开头就提到了—她是女王。安东尼和克莱奥帕特拉还组建了家庭,让问题变得更加复杂。罗马人采用一夫一妻制。不过,就像其他的许多奴隶制社会一样,一夫一妻制并不意味着罗马人只能有一个性生活的对象。而且,在罗马人看来,性生活不是一种罪,而是很正常的一种活动。需要用制度来严格约束的只是传宗接代的事情—每个罗马男性只能拥有一位妻子来为他生育合法的后代。
此外,妻子也是家庭的核心人物。一方面,她的地位和人脉可以为其丈夫所用。安东尼以实际行动向所有的罗马人证明了他是有能力和一位女王组成家庭的男人。另一方面,对于安东尼这样的大人物而言,妻子还是他的政治伙伴。一般说来,人们都认为夫妻二人是会互相支持的。[312]在晚期罗马共和国,虽然男性往往是家庭的支配者,但是女性显然也能发挥不小的政治影响力,像奥克塔维娅和安东尼那样的政治联姻就是基于这样的考虑而出现的。
这种婚姻关系的缔结基础是政治考虑,而不是男女双方的感情。爱情甚至往往不在考虑范围之内。或许正是如此,至少精英阶层的罗马人还比较能够容忍婚外情。他们并不是不知爱情为何物,事实恰恰相反,他们很明白个中三昧。在罗马革命时期就诞生了某些异常热烈的情诗。但是,罗马人一般不会指望着在婚姻中找到这种浪漫的感情。
显然,奥克塔维娅和安东尼之间的联姻最终未能保住屋大维和安东尼的盟友关系。但是,这段婚姻关系的终止是他们二人之间政治关系破裂的结果,而非其原因。虽然乍一看可能有些奇怪,但是安东尼真的在很长的一段时间里同时维持住了他和克莱奥帕特拉组成的王室家庭以及他和奥克塔维娅组成的罗马家庭。
安东尼在信里列举了他觉得有可能和屋大维上过床的女性。她们都不是地位低下的女子(没有人会在意屋大维是否和那种女性发生过婚外性关系),而是屋大维身边最亲密的朋友的妻子。安东尼的意思是,就连屋大维侵害他人家庭的通奸行径都不足为奇,他自己的行为就更不应该受到指责了,因为他的两个性生活对象都是他的合法妻子。
根据罗马的法律,每个罗马男性都只能和一名罗马女子维持一段婚姻关系,组建一个家庭。不过,身为三头之一,安东尼掌握着莫大的权力。克莱奥帕特拉也是地位超然的女王,他们不太可能会拘泥于寻常的法律规定。后三头的权力让他们甚至可以不顾应有的法律流程,随意地杀死任何一位罗马公民。这样的权力肯定也能解决婚姻法的问题,让安东尼如愿以偿地和克莱奥帕特拉拥有合法的婚姻关系。因此,安东尼完全可以有底气地宣称克莱奥帕特拉就是他的合法妻子,他们的孩子也是合乎法律的,他和奥克塔维娅的关系也是如此(就算这是重婚)。
然而,让安东尼得以摆脱传统束缚的这份权力同时也改变了他的家人的政治地位。成家确实是一件从头到尾都很实际的事情。例如,在三头同盟时代的早期,富尔维娅凭着安东尼的权力而享有了罕见的强大政治影响力,因为人们通常认为掌权的男性会听取妻子的意见,并且在此基础上做出决策;妻子则会热心地支持丈夫的事业,同时对外代表着丈夫的意志。在共和国时代,家庭内部的这种决策过程不会导致什么问题,因为罗马官员的所有重要决策都还需要进一步和同僚们展开讨论。但是,在三头同盟时代,安东尼和屋大维的家人就拥有了前所未有的政治地位。
所以,安东尼和克莱奥帕特拉的关系遭到诟病不是因为人们忽然想要把男女私情夸大为严肃的政治问题,而是因为安东尼和克莱奥帕特拉组建家庭本身就是影响深远的政治行为,他们二人的政治未来由此被绑在了一起。至少从理论上来说,双方都从中受益了。对于这段亲密的私人关系,他们并不介意对外声张,他们甚至还在货币上描绘了彼此之间非常相像的形象(如图5)。通过与安东尼联姻,埃及的女王克莱奥帕特拉获得了罗马世界的权力。所以,罗马世界的政治人物势必要对安东尼的这段关系加以审视。屋大维的通奸行为确实如安东尼所说,不是什么严重的问题,因为没有人会相信这些情人能够影响屋大维的决策。但克莱奥帕特拉完全不同。她原本就有着不小的权势,罗马有可能会为她所掌控。当然,要除掉威胁着罗马人的克莱奥帕特拉就意味着要攻击安东尼。
我们在前文强调了爱情并不是这场战争的主要原因,但是从安东尼在信件里所写的愤怒、简短而明确的文字来看,我们也无法完全忽视埃及女王的异域魅力以及他们之间的亲密关系。安东尼最后还提出了这个问题:“和谁一起享受欢愉有什么关系呢?”然而,无论他有多么讨厌人们把他的风流韵事摆上台面来加以严肃的政治讨论,无论这种事情在罗马的历史上有多么罕见,对这个问题的回答都是肯定的—安东尼和谁一起享受欢愉真的是个大问题。而且,安东尼自己也一定是明白这一点的。
亚历山大的封赏仪式
公元前34年,为了庆祝他对帕提亚人取得的胜利,安东尼在亚历山大举办了游行仪式。身为战俘,亚美尼亚国王被戴上了银质的镣铐,然后跟着安东尼的游行队伍在城里走了一趟。安东尼本人则乘着战车,一边前进,一边向民众致意。埃及人民簇拥着一个银色的高台,其上有一个金色的宝座,他们的女王就坐在这里。此次庆功仪式的高潮就是把俘虏和战利品都献给克莱奥帕特拉。[313]接着,安东尼为亚历山大城内的军民举办了一场盛大的宴会,然后对大家发表了讲话,宣布克莱奥帕特拉为统治诸王的女王,克莱奥帕特拉和尤里乌斯·恺撒的儿子恺撒里昂为王中之王。这种波斯风格的头衔让他们至少在名义上成了东方的主人。安东尼和克莱奥帕特拉所生的子女也得到了封赏:托勒密得到了叙利亚;克莱奥帕特拉·塞勒涅拿到了昔兰尼加(Cyrenaica,埃及以西的土地);亚历山大则获得了亚美尼亚以及东至印度的土地。[314]
亚历山大的封赏仪式并不符合罗马的传统。当然,游行以及在市中心献出战俘还算是效仿了传统的凯旋仪式。但是,这次活动的举办地点和克莱奥帕特拉扮演的角色都是全新的设计。这场封赏仪式足以说明公元前34年的罗马政治已经与之前的时代大不相同。此外,这种公开的仪式是执政者在人民面前塑造政权形象的一种手段,并且因此具备了意识形态方面的意义:执政者可以通过这种仪式向特定的受众宣传某种世界观。显然,安东尼以及克莱奥帕特拉都不可能在民众面前把自己包装成之前统治埃及的各位将军或者法老,埃及女王和罗马三头之一组成的王室是史无前例的,无论罗马人还是埃及人都能明显地感受到这一点。因此,安东尼和克莱奥帕特拉不得不去探寻可用的政治象征,然后对其加以改造,进而发明出新的仪式。例如,他们以神话为基础,把克莱奥帕特拉塑造为伊西丝(Isis),把安东尼描绘成奥西里斯(Osiris)或狄俄尼索斯。[315]
不过,这种尝试具有一定的政治风险。象征其实是在给人们展示一种看待现实的方式,同时也会让人们有机会去展开独立的思考。如果权力的运行方式已经不能顺畅地融入既有的政治文化,那么执政者就需要对政治文化进行创新。他们可以在公开的仪式上向民众展示新的象征,获取民众的认可,从而成功地树立新的政治文化。但是,对于执政者提出的新的解释世界的方式,民众或许会表示怀疑乃至否定。
一般说来,罗马的将军取胜以后会向元老院提议在战败者的土地上建立起殖民地。然而,这一次,安东尼不仅没有采用罗马人的传统做法,还公然任命自己的家人去统治这些土地。这是足以让罗马人深感震惊的新颖事物(虽然熟悉希腊王族传统者大概立刻就能明白安东尼在做什么打算)。而且,这些封赏的意义也不明确,克莱奥帕特拉和她的儿女们看起来不会去实际地统治这些地方。克莱奥帕特拉本人的角色显然是很被动的。在封赏仪式上发表讲话的是安东尼,预先做出这些安排的也是安东尼,这次封赏事件体现的完全是安东尼的权力。亚历山大的封赏仪式是一场政治秀。安东尼等人采用了罗马的凯旋仪式里的一部分内容,但也吸收了埃及和近东王权的一部分传统,因为这种形式更能引起当地居民的文化共鸣。包括安东尼和最为著名的亚历山大大帝在内,东方的征服者们往往会以当地居民认可的传统方式来宣传自己的王权。安东尼这次的宣传受众既有罗马人也有东方诸国的人民。这些群体有着截然不同的文化背景,但是他们之间的交流已经有了比较长的历史。所以,无论哪一方都不会对安东尼的封赏仪式感到陌生,他们都能够明白其寓意。
安东尼当然不是法老,也没有把自己宣传为法老。他也不同于托
勒密王朝的希腊国王,克莱奥帕特拉没有尝试着把安东尼塑造为埃及
的君主,他的形象没有和克莱奥帕特拉一起出现在埃及的神庙上。克
莱奥帕特拉更倾向于宣传自己和恺撒里昂一同出现的样子,安东尼则
仍然是外来的罗马人。不过,这次的封赏仪式毕竟体现了安东尼享有
永久的统治权,克莱奥帕特拉及其子女在仪式上获得的头衔都彰显着
安东尼的权威。封赏仪式还宣布安东尼和克莱奥帕特拉的子女后代都
可以统治东方的土地,这种声明全然违背了共和国的旧制度。不过安
东尼却仍非国王。他既没有给自己加冕,也没有采用新的头衔。[316]
总之,安东尼改造了既有的宣传权力的方式,从而将其化为己
用。无独有偶,屋大维也做了类似的事情。如前文所述,屋大维击败
庞培以后在罗马城广场上立起了自己的金色雕像。由于恺撒已经被尊
奉为神明,屋大维还命人铸造了称其为“神子”的货币。我们很难说
他们二人此刻的所作所为有很大的区别,安东尼涉嫌效仿希腊化时代
的东方君主;屋大维则自比于神明,在罗马城内竖立起自己的金色雕
像。如果在罗马的共和制度坚如磐石的年代,他们二人的举动显然都
会遭受猛烈的抨击。安东尼和屋大维都是在以全新的方式宣传自己的
权力,试图让自己在理论上也摆脱元老和罗马传统的束缚。他们的做
法无疑都反映了公元前1世纪晚期罗马政治的新形势。不过,安东尼在
亚历山大举办的封赏仪式还反映了他和屋大维之间的关键差异。这场
仪式显然说明了安东尼和克莱奥帕特拉已经在私人和政治层面上合二
为一,他们的权力中心则位于亚历山大。身处东方的安东尼仍然可以
在一定程度上维持罗马人对他的支持,并且对这些支持者予以奖赏。
然而,在当时,埃及的亚历山大距离罗马有两三个月的路程,克莱奥
帕特拉女王和意大利政界的联系也不是很密切,这样一个以亚历山大
为中心的私人关系网络难免不能及时而广泛地照顾到位于意大利的支
持者。而如果关系网络不能满足其成员的需要,这些人或许就会择木
而栖。更何况,屋大维的关系网仍然立足于意大利。
安东尼的个人及政治命运都已经和克莱奥帕特拉维系在一起。她为安东尼生下了三个孩子,就算安东尼在宣传自己的权力之时未曾把克莱奥帕特拉当作核心人物,他也不可能简简单单地把克莱奥帕特拉给抛在一边。况且,没有任何证据能够证明安东尼觉得自己有必要做这种事情。此时,这段婚姻给他带来了一位美丽动人的女王和无与伦比的财富与地位。克莱奥帕特拉是安东尼政权里的关键角色。
三头同盟的终结
时至公元前33年,安东尼和屋大维的关系已经相当紧张了。具体的细节我们已经无法获悉,但他们显然在很多问题上都发生了争执。安东尼要求屋大维派出援军;屋大维则要求分享一半的战利品,同时还抱怨安东尼擅自举行亚历山大的封赏仪式。安东尼接着质问了屋大维取消李必达的权位,并且入主西西里和阿非利加的事情。虽然看起来就很难取信于人,但屋大维还是对安东尼声称他原本打算饶恕塞克斯图斯·庞培,进而指责安东尼杀死庞培。他也对克莱奥帕特拉和恺撒里昂表示了不满,暗指安东尼在亚美尼亚的战争有违道德。[317]他们基本上都在围绕着旧闻展开争论。
双方的交流大体上处于保密状态。当然,某些贵族也许曾经不慎泄露过机密。在此期间,信使们来来往往,为这两个人传递着令彼此都埋怨不已的消息。或许,罗马的贵族们已经在不停地讨论着安东尼和屋大维的关系。但是,双方依然没有大打出手,他们还没有遇到什么不得不立刻解决的法律问题或政治问题。虽然后三头的权力即将在公元前33年末抵达法定期限,但这两个人看起来都不会心甘情愿地回归“正常”的政治地位。
公元前32年,安东尼的密友格奈乌斯·多米提乌斯和盖乌斯·索西乌斯成了执政官。在1月1日的传统就职典礼上,多米提乌斯借机赞颂了安东尼,并且对屋大维加以批评。屋大维本人并不在现场,但他很快就做出了回应。他召集了元老院会议,然后带兵与会。两位执政官只得静静地听着屋大维驳斥他们所做的批评。接着,会议就结束了。
于是,这两位执政官连夜逃离了罗马。[318]三头同盟的正式终结和屋大维此次动用军队的行为或许的确让很多人深感不安,担心之后还会有更大规模的暴力冲突。但就算如此,战争也未必不可避免,此时还远远没有真正达到足以引发战争事端的地步。
不过,在某些人看来,站队的时机已到。一部分人离开了罗马去
投奔安东尼,另一部分人则从亚历山大来到了屋大维这边。抵达罗马
的这些人充分表达了他们对克莱奥帕特拉的不满,还暗指安东尼想要
把罗马献给克莱奥帕特拉。除此以外,或许还有很多人期待着有同时
忠于双方的人能够从中斡旋,再一次化解两边的矛盾。然而,逃至罗
马的变节者让屋大维得知了安东尼的遗嘱就被保管在维斯塔贞女
(Vestal Virgins)手中(罗马人常常把文件和财产存放在神庙里,因为
他们认为这样就可以得到神明的保护)。于是,屋大维全然不顾法律的
约束,强行取走了安东尼的遗嘱,然后对元老们宣读了其中的内容。
这份遗嘱里有一项看似无关紧要、实则非常致命的条款—安东尼希望
自己死后能够和他的女王一起被葬在亚历山大。为此,元老们断然披
上了战袍,表决同意对克莱奥帕特拉开战。[319]
屋大维提出的宣战理由是克莱奥帕特拉正在窃取罗马的最高权力。安东尼的遗嘱可以算作一种证据:安东尼已经想要抛弃罗马,彻底投入克莱奥帕特拉的怀抱。而且,他们之间的婚姻也可以视作克莱奥帕特拉对罗马东部领土主权的篡夺。由此,罗马和亚历山大之间有了裂痕。罗马城本该是国家的唯一中心,享有最高的权威。但现在,这种独一无二的地位受到了威胁。如果有安东尼相助,克莱奥帕特拉有可能让所有的罗马人都臣服于她。而亚历山大的封赏仪式已经证明了安东尼确实打算和克莱奥帕特拉建立长久的关系,甚至还要把权力传承给子女后代,开创一个新的王朝。
面对这种潜在的威胁,屋大维要求意大利的城镇社区立誓以他为领导(dux),随他一同作战。他由此宣布整个意大利都在支持他。[320]屋大维让意大利在政治和文化上取得了某种统一性,从而成为支撑起一个大帝国的根基。在古老的共和国时代,罗马城以外的地方都不重要,只有罗马城的政治生活才值得重视。然而,屋大维造就了新的权力版图。老兵们定居的城镇和殖民地、与屋大维达成一致的社区都被包括在内。意大利成了国家的中心。屋大维对意大利的重视说明了,身为三头之一,他的私人关系网,亦即他的势力范围已经远远超出了罗马城。此外,强调意大利的支持有助于表明他现在和东方的异国埃及站在对立面上。
当然了,这场战争其实是安东尼和屋大维的战争。意大利境内还有不少安东尼的支持者。我们可以想见,很多倾向于支持安东尼的人或许还留在意大利,和安东尼一起历经多场战役的老兵们可能也对他留有不错的印象,政治宣传往往有别于现实。但是安东尼毕竟不能召集起留在罗马和意大利的支持者,这些人无法给安东尼提供多少实质性的帮助。因此,屋大维成功地实现了他的政治宣传:意大利的资源会被他调集起来对抗安东尼及其埃及盟友。
阿克提翁之战
在两位执政官逃跑以后,安东尼和屋大维先做出了一些谈判的姿态,然后就在公元前32年末展开了军事行动。不过,到公元前31年春,双方才准备就绪。屋大维的海陆军队集结于意大利南部的布伦迪西翁,安东尼则率军来到了位于其势力范围最西端的希腊。安东尼让舰队停驻在阿克提翁,又往伯罗奔尼撒(Peloponnese)派出了驻军。
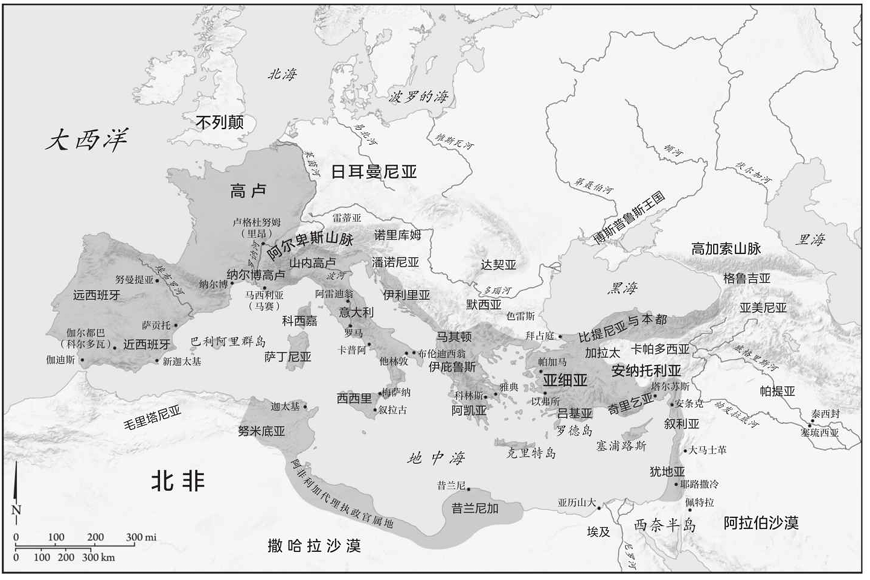
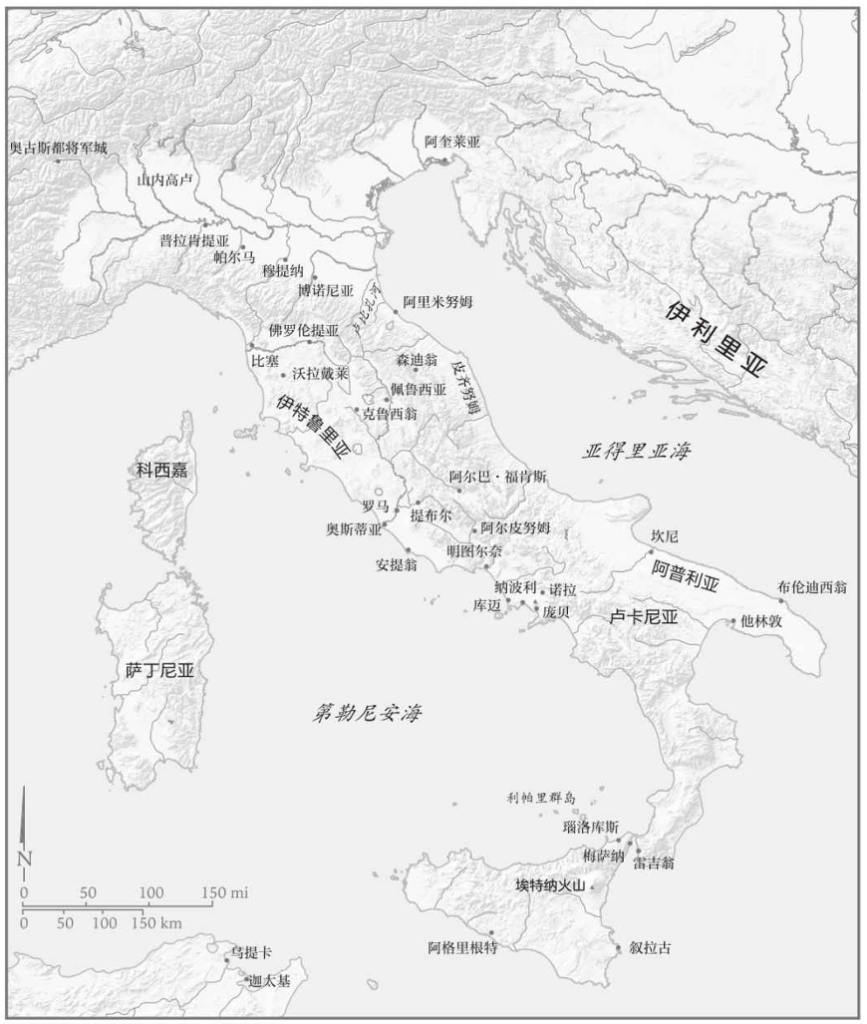
希腊西部的安布拉奇亚湾(Ambracian Gulf)深入内陆约五十公里(请参考地图5),它和伊奥尼亚海以一条窄短的水道相连。阿克提翁就坐落于这个入口的南岸,它是希腊西海岸的少数良港之一。虽然阿克提翁的陆路交通受到了崎岖的山地的阻碍,但它和意大利以及伯罗奔尼撒的海路交通是很便捷的。因此,驻扎在这里的舰队有着不小的行动空间。安东尼的意图是直接威胁亚得里亚海沿岸归属于屋大维的城镇或部队。其实,安东尼的这个策略在佩鲁西亚战争以后就曾经实施过一次。当时的他以希腊西部为基地,利用己方的海军优势主动向布伦迪西翁发起了进攻。然而,公元前31年的屋大维已经今非昔比,他的舰队现在有能力和安东尼竞争海洋的控制权。所以,这一次,阿克提翁不再是安东尼进攻意大利的跳板,他甚至会发现自己已经被困在了安布拉奇亚湾。
阿格里帕决定先发制人。他绕过了阿克提翁,直接攻下伯罗奔尼
撒半岛西南部的米托涅(Methone),进而对安东尼的领地发起了一连串
的劫掠行动,骚扰着安东尼的部队。屋大维则横渡亚得里亚海,大概
登陆于今天的阿尔巴尼亚(Albania)境内某处,准备进攻安东尼部署在
阿克提翁的舰队。[321]接着,就在安东尼赶来与其大部队会合之时,
屋大维经由帕克索斯岛(Paxos)南下至安布拉奇亚湾北岸,在阿克提翁
以北数公里处安营扎寨。屋大维试图和安东尼的海军或陆军交战,但
是安东尼在海湾入口的两岸都建好了防御工事。如果强攻,屋大维势
必会面临不小的风险。此时,安东尼还有部队大概在沿着曲折的陆路
赶赴阿克提翁,他不愿在这种时候应战。于是,双方都开始一边积攒
军力,一边等候良机。[322]
不过,阿格里帕向来热衷于主动出击。他趁此时机在伯罗奔尼撒
大肆劫掠,还在琉卡斯(Leucas)[1]建立了据点,让屋大维控制了阿克
提翁以南的交通要道。至此,屋大维已经从海上包围了安东尼。而
且,阿格里帕的舰队现在掌控着科林斯湾(Gulf of Corinth),可以直
接威胁安东尼的陆路交通,[323]安东尼的后勤因此受到了严重的影
响。在海路被截断的情况下,他的补给队只能沿着曲折又漫长的陆路
前进。
希腊的这个地区在夏天的时候有可能会变得异常酷热,当地的气
候还很潮湿。位于低地的安东尼大概尤感不适。而北边的屋大维所部
驻扎在地势较高的地方,每天下午都能享受到清爽的海风。现代的安
布拉奇亚湾南岸分布着很多沼泽。而在古典时代,这里疟疾频发。在
当地获取清洁的饮用水是一个大问题。而且,安布拉奇亚湾的水体流
速较慢,几乎不可能被用来处理营地里产生的垃圾。因为补给线受到
了骚扰,安东尼帐下还有越来越多的人饱受饥饿之苦。总而言之,安
东尼的部队在酷暑时节承受着食物、燃料、饮用水的匮乏,居住在肮
脏又潮湿的环境里。没过多久,疾病就来袭了。安东尼已经受困,他
的军队危在旦夕,他不能再坐以待毙了。
地图5:阿克提翁及其周边地区
于是,安东尼来到北岸向屋大维发起了挑战。可形势已然逆转,
屋大维现在更愿意坐等安东尼的军队不攻自破,他肯定已经知道安东
尼此刻急需做出决断。摆在安东尼面前的大概有三条路:首先,他可
以尝试着与屋大维的陆军展开决战,将其一举击溃;其次,他可以让
海军尝试突围;最后,他的选项就只剩下先烧毁己方的全部船只(同时
也是安东尼的主要军备),然后带着他饥病交加的部队,顶着敌方海陆
军队的骚扰,沿着崎岖的山路撤退。如果要展开陆军决战,安东尼就
必须来到海湾北岸靠近今天的普雷韦扎(Preveza)的那块平原上。因
此,他率军出动,在屋大维的据点前摆好了阵势。双方发生了一些小
规模的冲突,但屋大维还不想与他展开陆军决战。
这一定是屋大维和阿格里帕兼权熟计的结果,他们想要让海战来决定此次战役的胜负。屋大维拒绝出营应战的态度让安东尼也明白了这一点。此前,屋大维和阿格里帕以海战击败了塞克斯图斯·庞培,而安东尼还没有海战的经历。看起来,他们二人大概觉得己方的海军能够稳占上风。
既然屋大维无意展开陆战,安东尼便撤走了海湾北岸的部队。这
一举动充分说明了此时的主动权掌握在屋大维手中。有史料称,安东
尼此时召开了一场作战会议。这则记载又一次突出了克莱奥帕特拉的
角色,声称她才是最高决策者,而她已经被各种各样的凶兆给吓坏
了,认为他们现在应当竭尽全力地撤退。[324]这种说法不足为信。到
了这个时候,安东尼等人其实已经没有什么可以商议的了,他们的主
要军备就是这支舰队。更何况,他们的陆军和海军的关系堪称休戚与
共。[325]假如安东尼能够在海战中大败屋大维和阿格里帕,他就能确
保对希腊的掌控权,进而再次以希腊为跳板进攻意大利,乃至彻底扭
转局势,让屋大维也尝到失去补给的滋味。就算安东尼仅仅是让自己
的舰队大致完好地撤离了此地,他也可以有重整旗鼓、来日再战的机
会。比如,他可以把舰队派去竞争亚得里亚海的控制权,也可以把这
一批陆军撤走,还可以从东方的领地召来更多的后援军。总而言之,
无论是取胜还是打平,安东尼和克莱奥帕特拉都至少能够摆脱阿克提
翁的困境,改善己方主力部队的作战条件,从而继续进行这场战争。
在安东尼的部队离开了海湾北岸以后,双方都立刻开始着手准备海上
决战。
安东尼和克莱奥帕特拉花了几天的时间来等待合适的风况和海
况。公元前31年9月2日,他们率领舰队离开了阿克提翁的水道。屋大
维和阿格里帕正在等待着他们。安东尼的舰队就在海湾入口之外。他
们排好了紧密的阵形,组成了一堵木质高墙,以免敌方战舰穿插进
来。双方都在等待,没有人轻举妄动。屋大维也许期待着安东尼的舰
队会朝南方的开阔海域逃跑,以致露出侧翼并且加大船只的间距,但
安东尼没有犯下这种错误。于是,屋大维下令延长阵线,同时派出小
股部队去包抄敌舰。面对着遭到多方夹击的威胁,安东尼选择了利用
敌方调整阵形的时机发起进攻。[326]
安东尼的舰队有着更大、更重的船只,它们不仅火力更强,而且具备高度优势。屋大维的战船更小、更轻,因而更加灵活;但这种船只如果被困住了就很有可能被敌方强行攻下。在很长的一段时间里,这场海战都没有明显的优劣之分,两边都无法给对方造成严重的损伤。但是,因为比较笨重,安东尼的舰队基本不可能逃离敌方的攻击。
传说,在战况依然僵持不下的时候,克莱奥帕特拉受到了惊吓,
连忙逃跑,安东尼也随她而去。[327]也就是说,决定了战局走向的是
脆弱的克莱奥帕特拉和过于信赖、爱护克莱奥帕特拉的安东尼。但这
个传说很可能是不实的。安东尼和克莱奥帕特拉此战的目标是至少突
围离开海湾,进入开阔的外海,从而完成撤退,以求在日后另寻良
机。在中午以后、傍晚之前,风力渐渐增强了。安东尼和克莱奥帕特
拉一定在密切地关注着风况,想要借助风势,一口气摆脱敌舰。但
是,挑选扬帆的时机并不容易。就算风力和风向都合适,安东尼的船
只也还需要有充足的时间才能拉开距离,真正地逃出生天。[328]而
且,所有战舰都必须整齐划一地开始行动,因为放弃作战、进行转向
或许会导致阵形破裂或者露出侧翼。那样一来,屋大维就很有可能找
到可乘之机。而只要安东尼的大多数舰船未能逃离,屋大维就算是取
得了胜利。也许,安东尼甚至应该安排一定量的殿后部队来掩护大部
队扬帆撤退。
时机一到,克莱奥帕特拉便下令撤离。安东尼本人的行动也很顺
利。但是,他的绝大部分战舰都没能突围。不过,尽管我们可以认为
胜负已分,但是战斗还没有完全结束,安东尼的舰队还在作战。这本
身就足以表明安东尼和克莱奥帕特拉的撤离是早就安排好的。克莱奥
帕特拉没有像传说里描写的那样因恐惧而慌乱地逃跑;安东尼也没有
被爱情冲昏头脑,不顾一切地追随爱人而去。就算克莱奥帕特拉和安
东尼已经相继离去,剩下的舰队也不见得就毫无希望,他们仍然在努
力地寻找突围的机会。
安东尼方舰队的阵形依然比较完整,屋大维等人无法将其打乱。但随着白天渐渐过去,他们逃生的希望越来越小。在临近夜晚的某个时间点上,风势会完全消失,然后,他们就会彻底失去打破僵局的机会。此时,屋大维的进攻已经使得安东尼方舰队的阵形变得更加紧密,也更加难以逃跑。于是,屋大维开始派人去准备火攻。
屋大维下令向敌舰射出了装着木炭和沥青的罐子。在火箭的配合下,安东尼的木制舰队陷入了火海。船员们赶紧开始灭火。他们先把自己的饮用水泼到了沥青上,然后开始用海水。安东尼的部下或许不太熟悉这种海战秘技。沥青是不溶于水的,对着燃烧的沥青泼水只会让火势进一步扩散开来。于是,他们开始击打火焰,甚至试图用尸体来扑灭火势。但这也无济于事,火焰不停地扩散开来,很快就彻底失去了控制。在此期间,屋大维的海军就在旁边看着安东尼的舰队化为灰烬。[329]战斗结束了。
安东尼的陆军正在撤离,但他们几乎不可能顺利逃生。他们的其中一条可选路线是经由陡峭的山路朝着马其顿前进。或者,他们可以顶着阿格里帕的海军骚扰的压力,沿着科林斯湾撤退。无论哪条路都充满了艰难险阻,而且很漫长,就算他们能够挡住屋大维等人的进攻,补给也是一个难以解决的大问题。对于一支已经饱受疾病侵袭的部队而言,这是不可能完成的任务。既然逃生几乎无望,那么安东尼的军团自然就选择了投降。[330]
穷途末路的爱情
安东尼和克莱奥帕特拉也许在逃跑之时曾经短暂地停留了一阵
子,以便察看己方陆军是否能够撤离。但在得知投降的消息以后,他
们便朝着埃及航去。对于地位较高的俘虏,屋大维在斟酌以后或杀或
饶。接着,他把一部分军队调回了意大利,表现出充足的信心。屋大
维在自己的军帐所在处建造了一根巨大的胜利纪念柱,饰以安东尼战
船的船首,并且将其献给阿波罗。后来,这里更是有了一座纪念此次
胜利的城市—尼科波利斯(Nicopolis),也就是胜利之城。它坐落在山
坡上,注视着屋大维曾经取胜的那片海域。屋大维还下令要求每五年
就在此举办运动赛事,让罗马世界每五年都来庆祝屋大维的胜利,同
时铭记安东尼和克莱奥帕特拉的命运。屋大维把阿克提翁之战渲染为
决定了整个罗马世界前途的重大事件。
此战以后,罗马世界里的几乎所有人都看清了局势。仅从理论上
来说,安东尼还掌握着非常充足的资源。他有很多军团还驻留在叙利
亚和阿非利加。有不少附庸国王还理应对他效忠,派兵前来支援他的
后续行动。克莱奥帕特拉也拥有大量的资金和战船,虽然她的舰队位
于红海。然而,阿克提翁之战干系重大。凡知晓战况者都不难看出这
场战争其实已经结束,没有必要白白葬送自己的性命。安东尼已败,
屋大维即将获胜。安东尼的盟友纷纷叛变,东方的各位国王以及由安
东尼委派至各个地方省份的罗马总督都开始向屋大维求和。最后,只
有埃及还处在安东尼和克莱奥帕特拉的掌控之内。
他们二人肯定也能看清现在的战略形势。此时的屋大维可以调用
巨量的资源,他们根本无法望其项背。于是,他们返回了亚历山大,
等候征服者的到来。他们派出了使者,尝试以外交渠道解决问题,却
并没有取得什么成果。安东尼和克莱奥帕特拉已经失去了谈判的资
格,屋大维没有理由跟他们讲和。就在这个时候,屋大维遇到了一场
兵变,已经退役的士兵又在要求得到奖赏。屋大维只好回到布伦迪西
翁去安抚哗变的士兵。不过,这只是推迟了结局的到来而已。安东尼
和克莱奥帕特拉由此得到了冬春两季的喘息时间。他们竭力召集部
队,准备抵抗到底。此外,为了逃避大难临头的压力,他们在冬天花
了大量的时间在自己最为擅长的事情上—挥金如土,举办奢华的晚
宴,展示自己的富有。他们还特意和朋友们一起组建了一个名为“共
赴黄泉”的享宴团体。[331]公元前30年,屋大维的军队即将抵达埃
及。
埃及的沙漠让这个国家有了抵御外敌的天堑,但是安东尼此时需
要同时抵挡来自东方和西方的入侵(请参考地图6)。之前,安东尼曾经
任命一位骑士科涅利乌斯·伽卢斯去负责指挥西边的昔兰尼加的军
队。安东尼也许认为地位低一级的贵族更有可能为自己尽忠。然而,
伽卢斯还是选择了叛变,甚至还率军向埃及发起了进攻。至于屋大维
的部队,他们很可能从东边的佩鲁西翁(Pelusium)而来。安东尼本想
去东方应敌,但现在却必须到西边处理叛军,因为伽卢斯已经攻下了
一座边境城市帕莱托尼翁(Paraetonium)。安东尼一度认为自己或许可
以说服士兵们回心转意。然而,他失败了。接着,安东尼在帕莱托尼
翁城外驻扎了没多久就得知了屋大维终于抵达了埃及。[332]
于是,安东尼转而率军向屋大维进发。他的骑兵在亚历山大的外围地带遇到了屋大维的部队并且将其击退。然后,安东尼派出了步兵乘胜追击,但他没能给屋大维造成严重的伤亡。不过,他还是深感振奋,声称自己就算是在此刻这样的绝境之中也有扭转乾坤的能力。但是,四面八方都有无数敌军袭来。安东尼不可能真的相信自己有机会逃脱死亡的命运。第二天,他命令海军离开亚历山大。当这支舰队遇到屋大维的优势海军以后,他们举起了船桨,选择了投降。陆军的情况也不容乐观,安东尼带着步兵投身于战场,却遭遇了失败,被迫退回城内。[333]
地图6:埃及
克莱奥帕特拉获悉了己方部队叛变和安东尼被击败的事情,她知道结局将至。此前,她已命人把一部分财物运到了自己的陵墓里。现在,她前去陵墓之内,关上了大门。埃及的女王已经准备好迎接死亡。
很快,全城的人都得知了这个消息。安东尼也不例外。他得到的情报大概是克莱奥帕特拉已死。因此,安东尼拔剑自刎。但就在他倒在地上流血不止的时候,又有消息传来,称克莱奥帕特拉还活着。于是,安东尼命人将他抬去和女王相会。他穿过了亚历山大的街道,抵达了陵墓外,然后被送到窗口处,在克莱奥帕特拉及其仆人的帮助下进入了陵墓。终于,安东尼回到了克莱奥帕特拉的身边,在她的臂弯中离开了人间。[334]
克莱奥帕特拉并没有立刻随安东尼而去。屋大维的使者进入了亚历山大,他们看起来愿意开启谈判,甚至有可能饶恕克莱奥帕特拉及其子女的性命(最后除了恺撒里昂以外,他们确实都没有被杀)。这些使者进入了陵墓,抓住了克莱奥帕特拉,夺下了她打算用以自裁的匕首。然后,克莱奥帕特拉被带回了王宫。屋大维的人小心地看守着她,等待屋大维本人前来。[335]
关于克莱奥帕特拉和屋大维的会面,有一个虚构的故事流传至今。据说,长于诱惑男性的克莱奥帕特拉试图对年轻的征服者屋大维故技重施。但屋大维充满了男子气概,毅然拒绝了。他不是恺撒,更不是安东尼。他有着更加强大、更符合罗马道德标准的自制力。但是,我们基本没有理由相信克莱奥帕特拉会忽然放弃自杀的意图。[336]她先为安东尼举行了丧礼,然后就回到了王宫。接着,她准备了一顿丰盛的宴席,穿上了女王的华服,向屋大维送出了一封信。及至屋大维收到这封信件之时,克莱奥帕特拉已然死去。屋大维破门而入,只见克莱奥帕特拉的两名侍女正在为她们的女王戴上冠冕。这是精心筹划的自杀。克莱奥帕特拉有意让罗马人发现即使是死她也秉持庄严的王家风范。克莱奥帕特拉的侍女也和她一样中了毒。
这位埃及女王的具体自杀手段至今仍然是一个谜,有史料暗示克莱奥帕特拉用了一枚带毒的别针。但在传说当中,她更有可能死于毒蛇之口。一条或数条毒蛇被藏在一堆无花果或是水罐里带进了王宫。伊西丝本就是和蛇有关的女神,对于最后的法老暨伊西丝的化身而言,这种死法或许确实特别合适。[337]最后,克莱奥帕特拉被葬在安东尼旁边。由此,安东尼的愿望实现了,他真的和他的女王一起被葬在了亚历山大。
帝国及其敌人
安东尼和克莱奥帕特拉之死既意味着人们即将开始进一步虚构相
关的传说故事,也标志着君主制的帝国时代即将到来。然而,阿克提
翁之战其实不是决定了罗马世界走向何方的事件,他们二人的自杀就
更没有改变历史的面貌了。即使阿克提翁之战的胜者是安东尼,罗马
世界看起来也不太可能走上截然不同的道路。安东尼和屋大维所在的
关系网络已经掌控了罗马。这场战争解决了位于亚历山大的安东尼和
克莱奥帕特拉以及位于罗马的屋大维形成的两个难分高下的权力中枢
问题。就算安东尼取得了胜利,他也几乎不可能损害这张关系网对罗
马的统治权。如果说罗马必定要从共和国走向帝国,那么从安东尼的
所作所为来看,我们完全可以说他其实比屋大维更加激进、更加急
切。当然,安东尼也许会让亚历山大在他的帝国里扮演更加重要的角
色,他和克莱奥帕特拉所生的子女大概也会构成帝国的第一个王朝。
但是,罗马和意大利终究是帝国的地理中心。无论安东尼对克莱奥帕
特拉的爱意有多么深刻,他应该还是会在罗马度过不少的岁月。
因此,安东尼和克莱奥帕特拉之死的意义恰恰就在于人们所虚构
的那些故事。[338]安东尼和克莱奥帕特拉正好可以被重塑为帝国的敌
人。而且,他们二人与帝国的对立关系要体现于他们的人生经历和生
活方式当中。于是,他们就成了为爱痴狂、沉迷于色欲、女性化、东
方化、必定灭亡的人物,这些属性也被渲染为同帝国与罗马相对立的
属性。随着罗马皇帝对政治和社会的掌控力越来越强也越来越全面,
安东尼和克莱奥帕特拉便逐渐代表了帝国在意识形态领域内的敌人。
无论真相究竟如何,安东尼和克莱奥帕特拉的历史意义就是让他们的
敌人成为与爱为敌之人,又让爱侣成了帝国的敌人。
[1]今名莱夫卡扎(Lefkáda)。—译者注
[309] 请参考Sally-Ann Ashton, Cleopatra and Egypt (Malden, MA: Blackwell, 2008), xi,她直言自己未能成功地找到“真正的”克莱奥帕特拉。彻底剥除相关文本中的虚构成分既是不可能的,也没有特别大的意义。不过,还是有很多人勇敢地朝着这个方向做出了努力,比如, Michel Chauveau, Cleopatra: Beyond the Myth, Ithaca (NY and London: Cornell University Press,2002); Joann Fletcher, Cleopatra the Great: The Woman Behind the Legend(London: HarperCollins, 2009); Stacy Schiff, Cleopatra: A Life (New York: Little,Brown, 2010),他在作品的第7页写下了这样的话:“在探寻克莱奥帕特拉的本来面目之时,我们需要一边排除那些许多人信以为真的假象和老生常谈的宣传话语,一边抢救那些所剩不多的真相。”相比之下更为实在一些的作品是Stanley M. Burstein, The Reign of Cleopatra (Westport, CT: Greenwood, 2004)。关于这些谣言和奥古斯都之间的关系,请参考Robert A. Gurval, Actium and Augustus: The Politics and Emotions of Civil War (Ann Arbor: University of Michigan Press, 1995)。Diana E. E. Kleiner,Cleopatra and Rome (Cambridge, MA: Belknap Press of Harvard University Press, 2005),她认为克莱奥帕特拉就好像是罗马世界的“明星”,同时代的人会对其生活产生无限的遐想。关于克莱奥帕特拉的形象,请参考Peter Higgs and Susan Walker, Cleopatra of Egypt: From History to Myth (London: British Museum, 2001)。
[310] Dio, 49.34.1.
[311] Suetonius, Divus Augustus , 69,他只引用了一部分。
[312] 请参考Riet van Bremen, The Limits of Participation: Women and Civic Life in the Greek East in the Hellenistic and Roman Periods (Amsterdam: Gieben, 1996),此书指出,男性和女性都会以家庭为单位参与公共生活。
[313] Dio, 49.40.
[314] Dio, 49.41; Plutarch, Life of Antony , 54.
[315] Plutarch, Life of Antony , 24和54提及克莱奥帕特拉被宣传为伊西丝。
[316] 请参考Rolf Strootman, “Queen of Kings: Cleopatra Ⅶ and the Donations of Alexandria”, Kingdoms and Principalities in the Near East , 139-157, edited by Ted Kaizer and Maria Facella(Stuttgart: Steiner, 2010)。他对封赏仪式有着相似的解读。
[317] Dio, 50.1.
[318] Dio, 50.2.
[319] Dio, 50.4.
[320] Res Gestae , 25.
[321] Dio, 50.11.
[322] Dio, 50.12-13.
[323] Dio, 50.13.
[324] Dio, 50.15.
[325] John C. Carter, The Battle of Actium: The Rise and Triumph of Augustus Caesar(London: Hamish Hamilton, 1970), 213-214,他得出了同样的结论。
[326] Dio, 50.31.
[327] Plutarch, Life of Antony , 66; Dio, 50.31-33.
[328] Carter, The Battle of Actium , 217-223对于这场战斗中风况所起的作用展开了推测。
[329] Dio, 50.34.
[330] Dio, 51.1.
[331] Plutarch, Life of Antony , 71.
[332] Dio, 51.9.
[333] Dio, 51.10; Plutarch, Life of Antony , 76.
[334] Dio, 51.10; Plutarch, Life of Antony , 76-77.
[335] Dio, 51.11; Plutarch, Life of Antony , 78-79.
[336] Dio, 51.12.
[337] Dio, 51.14; Plutarch, Life of Antony , 86.
[338] 关于这些故事,请参考Lucy Hughes-Hallett, Cleopatra: Queen, Lover,Legend (London: Bloomsbury, 1990)。
第十三章 奥古斯都的诞生
阿克提翁之战并不意味着安东尼和屋大维之间的战争已经结束。但是随着事态的发展,这场战斗最终演变成了安东尼阵营的全面崩溃:所有人都明白了谁会败亡,问题只是那一幕要怎样上演而已。对于屋大维而言,他还有别的事情需要处理。这场战争把恺撒派势力撕成了两半,安东尼的密友和部下应当受到怎样的处置呢?而且,屋大维极少在东方建功立业,东方人几乎不知道屋大维是何等人物。
罗马的西部领土大多被划分为各个省份,由中央派出的总督进行
统治。东方领土的安排则更加复杂,今天的希腊以东的那些土地很多
都是在比较晚的时候才接受了罗马人的统治。在种种原因的影响下,
罗马人不愿意把这些新领土划分为直属于中央的省份,反而更热衷于
扶植当地的附庸国王,让他们替罗马中央执掌权威。这种做法尤其盛
行于公元前1世纪60年代庞培的征服以后。一般说来,这些君主都很依
赖罗马的支持。为此,他们需要出兵协助罗马展开军事行动,还要用
金钱来体现他们的忠诚,虽然这些资金往往会被罗马的将领克扣一部
分。
对罗马贵族来说,这样一套让各地君主依附于罗马人的地方统治
体系是有一些好处的。例如,他们可以和这些君主建立良好的私交(安
东尼和克莱奥帕特拉的私交就非常深)。这种私人关系可以大大提升他
们的名望,因为和国王们结伴而行显然可以体现他们的突出地位。此
外,附庸国王的存在还给贵族们提供了赢利的空间。这些君主会对罗
马“朋友”慷慨解囊,以便让他们出手帮助自己维护利益。但是,当
罗马的政治精英们发生内斗之时,这套体系的缺点就暴露出来了。这
些远居各地的君主必须小心翼翼地考虑自己应该加入哪边的阵营。然
而,无论考虑得多么仔细,他们还是很有可能站到失败者那边去,这
是所有面对内战之人都难以避免的厄运。具体而言,在安东尼和屋大
维相争的这次内战当中,东方的诸位国王其实没有选择的余地。在过
去十年的时间里,他们一直都处于安东尼的势力范围内。安东尼肯定
已经除掉了所有不忠于他的君主,中立则几乎是不可能的。然而,和
屋大维作对是很有风险的事情,他素有绝不手下留情的名声,这些国
王难免担心屋大维取胜之后杀人灭国。
除了附庸国王以外,罗马东部领土的政治版图当中还有不少希腊
城邦(póleis,单数为pólis)的存在。希腊城邦内部的政治结构比较独
特:首先,官员们会组成统治城邦的委员会,但官员的任期一般不
长;其次是议会,其成员通常是地主贵族;最后是公民大会。简而言
之,希腊城邦和罗马的政体差异主要在于官员的权力。希腊官员的权
力较小,更依赖于贵族议会和公民大会。大多数的城邦都算是民主政
体,但城邦内的富人往往拥有更加强大的权威。所以,我们可以称之
为有限度的民主政体。每一个城邦一般都只控制着较少的土地,这个
地区的政治版图就是由大量的小城邦构成的。在亚历山大大帝的征服
以后,希腊的城邦开始活动于当地的数个王国(它们是这个地区的军事
强权)的范围之内,城邦和王廷之间的关系网就这样诞生了。
屋大维给这些城邦带来了一个新的问题。之前,罗马派出的总督
就好像只是某个大国的外交使节一样。在罗马的统治下,各个城邦还
是能够运用它们早已熟悉的外交手段。它们会派使者去罗马的精英圈
子里打点关系,用荣誉来收买人心。然而,屋大维时代的罗马发生了
很大的变化,权力现在集中于屋大维一个人身上,传统的罗马国家机
关似乎已经失去了实权。既然屋大维才是最高决策者,那么寻求罗马
元老的支持看起来就意义不大了。而且,屋大维不会像之前的总督那
样在短暂的任期结束以后就失去权力。总而言之,希腊的城邦现在需
要和它们的新主人建立起良好的关系。
赢得阿克提翁之战的屋大维仍然马不停蹄。众所周知,他之前在
取得胜利以后都不留情面地对敌人施以报复。就算是以当时的血腥标
准来看,其手段也不可谓不残酷。至于那些和安东尼为伍的罗马贵
族,我们不清楚屋大维具体是如何处置的,只知道他或杀,或罚,或
饶。其中被处死者的遭遇让人不禁回想起屋大维击败卡西乌斯、布鲁
图斯以及赢得佩鲁西亚之战以后的做法。他延续了一贯的作风,再度
表现得像是一个暴戾恣睢、草菅人命的独夫。后来,贵为皇帝的奥古
斯都把阿克提翁之战描绘为意大利和东方之间的对抗,还把自己塑造
成捍卫传统、维护秩序的人物。但那毕竟是后来的事情,此时的屋大
维看起来丝毫不打算掩饰自己手中生杀予夺的大权。
现在,屋大维把他的影响力施加到了东方,各地的附庸国王必须
摆正自己的位置。当年,安东尼曾经因人力、物力不足而在战争中向
这些君主寻求帮助。之后,他投桃报李,让这些国王得到了很多好
处,许多君主都扩张了自己的领地。但是,既然屋大维已经来到了东
方,那么当初安东尼赠予的利益就都不算数了。此外,有三位国王被
罢黜,一位被处死。没有遭殃的君主大概会感激屋大维不杀不废之
恩,庆幸自己还能保住权位,不会介意自己的领土发生怎样的变动。
况且,屋大维还把被废黜的国王的领地转交给了那些对他示以忠诚、
友好的君主。
在东方的诸位国王当中,统治着犹地亚的希律是除了埃及的克莱
奥帕特拉以外最为显赫的君主。在他之前的王朝因追随帕提亚人而被
安东尼麾下的将军索西乌斯给消灭了。之后,安东尼就扶持希律上了
台。希律原先并不算是犹地亚上流社会的一员。因此,犹地亚的传统
权力关系网络看起来不太愿意坐视希律入主犹地亚,他面对着颇为强
大的反对势力。然而,希律坚信安东尼会给自己提供可靠的援助,便
果断出手铲除了所有的政敌和对手,包括圣殿里拒不合作的大祭司。
希律还和马尔库斯(Malchus)的阿拉伯君主国展开了斗争,大胆地尝试
扩张自己的王国。正是因为忙于和马尔库斯作战,希律才未能亲自赶
到阿克提翁去支援安东尼。在得知了屋大维已经取胜以后,希律杀死
了现任大祭司,把自己的家人送到了比较安全的沙漠堡垒马萨达
(Masada),然后就动身前去拜见屋大维。
屋大维在罗德岛上接见了希律。这位来自犹地亚的国王既没有换
上丧服,也没有卑躬屈膝地摇尾乞怜,而是秉持自尊、身着盛装而
来,虽然他还是除去了象征着王权的冠冕。接着,希律开口了。他声
称自己是安东尼的挚友,若非阿拉伯的战事缠身,他必定会去阿克提
翁和安东尼并肩作战。而且,他虽然未能亲自参战,但还是为安东尼
提供了不少的粮草和资金。也就是说,希律自称会对朋友和恩人尽
忠,值得像屋大维这样的大人物对他加以信赖。假如屋大维愿意和他
缔结友谊,他同样会对屋大维鞠躬尽瘁。[339]
如果这则记载属实,那么希律就是很精明地把政治现实摆到了屋
大维的面前。东方国王们的政治手段一直很简单,屋大维肯定很快就
能想明白其中的利害关系。他应该已经知道犹地亚有很多人反对希
律,这位国王是凭着反复的大清洗才保住王位的。如果屋大维选择处
死希律,那么(经受了多次清洗的)犹地亚就没有人能够稳住局面了,
内战在所难免。最后,屋大维保留了希律的地位,而希律也没有辜负
屋大维的期待。当屋大维日后来到犹地亚之时,希律为他献上了丰厚
的礼物。屋大维的军队乃至其他有可能帮上希律的人都享受到了类似
的待遇。显然,让希律感恩戴德比砍下他的脑袋更有意义。
从公元前31年夏末到第二年初,屋大维基本都在小亚细亚和希
腊。他应该是在忙两件事,一件是准备去埃及结束这场战争,另一件
就是和希腊的各个城邦建立友好关系。城邦的精英们早就迫不及待地
想要讨好这位新的恺撒了。而屋大维的主要需求是资金,曾经花钱和
安东尼缔结友谊的这些城邦现在必须也向屋大维提供大量的资金才能
讨得他的欢心。不过,渐渐地,屋大维和希腊城邦发展出了新型的政
治关系。一种新的政治文化开始流行于东方的土地之上,这就是帝国
政治的运行方式。
亚历山大之城
这种新型的政治文化在埃及初见端倪。安东尼和克莱奥帕特拉被
击败以及克莱奥帕特拉自杀以后,托勒密王朝迎来了终结。屋大维根
本不可能让克莱奥帕特拉的后代继承王位、延续王统,因为这场战争
乃至相应的宣传战都过于激烈,让屋大维失去了宽恕的余地,他不得
不把埃及降格为罗马的一个省份。这种事情有一套传统的流程。屋大
维需要指定一位总督,然后先给埃及做好临时的安排,再把各项事宜
通报给元老院,让元老们加以审核。大概还会有专门的一项法案出
台。不过,在设置省份之前,屋大维仍须解决一个重要的问题:亚历
山大的命运。
罗马军队有毁灭城市以儆效尤的传统。这些年来,地中海沿岸地区已经有许多极其雄伟的城市都被罗马人夷为平地。迦太基在被摧毁以后的一百年内都是一片荒地,古老而壮观的科林斯也没有逃脱类似的命运,最负盛名的雅典同样被苏拉的部队洗劫一空,西边的西班牙和高卢地区也有不少城市沦为废墟,虽然史书往往对这些城市着墨不多。总之,肯定有很多人担心亚历山大也会遭遇毁灭。
亚历山大是古典时代最伟大的城市之一,其历史、建筑、规模(不
下于三十万人口)、文化都出类拔萃。它是地中海世界的第二大城市
(仅次于罗马),摧毁这样的一座城市会让屋大维的敌人和东西方的各
个势力都为之震撼。在后来的征服战争当中,屋大维并没有拒绝这种
惩戒性施暴的手段。更何况,按照屋大维的说法,此次战争的敌人非
同寻常。后来流行的文本浓墨重彩地把这场战争描写为不同的神明和
不同的道德之间的战斗,称其为捍卫罗马、意大利文化的战争,克莱
奥帕特拉和埃及的“威胁”得到了大量的渲染。所以,毁灭亚历山
大、抹除托勒密王朝的这座大都会是合乎道理的。然而,屋大维并没
有选择这条道路,他放过了亚历山大城。
对此,屋大维给出了三个理由。第一个理由是对这座城市的神明
的尊重。塞拉皮斯(Serapis)是一个特别的神,他同时具备希腊和埃及
的属性。有些人怀疑他是托勒密王朝专门为了新兴的亚历山大而捏造
的新神,但希腊人和埃及人并没有这种想法。而且,对于神灵,他们
往往只会做出某些发现或者在故事里加以详细的描写,而不会有意地
创作出新神。塞拉皮斯比较复杂,他的形象和宙斯最像。有时候,人
们会把他们相提并论。但埃及古都孟菲斯(Memphis)的公牛神阿匹斯
(Apis)、羊神阿蒙(Amun)、伊西丝的丈夫奥西里斯也都和塞拉皮斯相
似。埃及人相信法老具有神的某些性质,对其加以崇拜。塞拉皮斯就
凭着与众多神明相关的属性而为法老所用。此外,安东尼一度被塑造
为奥西里斯的化身。这说明罗马人并不怎么介意把人和神联系在一
起。他们同样可以利用这套象征体系。安东尼走过的路,屋大维也可
以走。
对伊西丝和塞拉皮斯的信仰不只存在于埃及,在公元前1世纪初,
罗马人也接受了这种崇拜。三头同盟成立之初就曾经颁布法令在罗马
城内建造一座新的伊西丝和塞拉皮斯的神庙。今天的我们恐怕永远也
不能完全理解罗马人究竟是怎样看待塞拉皮斯的。而且,对塞拉皮斯
的供奉显然在当时引发了一些争议—罗马人内部有着不同的意见。塞
拉皮斯大概更受平民的欢迎,而这一点可以解释为什么安东尼和屋大
维都有意成为塞拉皮斯信仰的支持者。总之,屋大维决定尊重塞拉皮
斯,把自己和这位少见的在地中海沿岸世界拥有众多信徒的神灵联系
在一起,而他的所有言行都会很快地被传回罗马。
不毁灭亚历山大城的第二个理由是屋大维对亚历山大大帝的崇
敬。屋大维早就开始利用亚历山大的形象来提升自己的名望,因为当
时的罗马人几乎可以说是痴醉于这位年纪轻轻就征服了东方的君王。
例如,关于亚历山大,尤里乌斯·恺撒的传记里有两个不同版本的故
事。公元前67年或公元前66年,恺撒正在西班牙。第一个版本的故事
称恺撒在阅读亚历山大的生平时骤然落泪,因为在亚历山大征战四方
立功无数的年纪,恺撒还没有取得什么成就。在另一个版本里,恺撒
同样表达了这种伤感之情。只不过,这一次的直接原因是他在伽迪斯
[Gades,加的斯(Cádiz)]遇见了亚历山大的雕像。[340]
这个故事大概率是捏造出来的,其作用就是为恺撒后来的伟大事
业做好铺垫。不过,我们可以由此看出当时有抱负者会以亚历山大为
榜样。比如,伟大的庞培[他的这个“伟大”(Magnus,即Great)的名
号也和亚历山大大帝(Alexander the Great)有关]在出征东方得胜归
来以后,认可了人们给他肖像上有些发福的圆脸配以和亚历山大相似
的发型。此外,在阿克提翁之战打响以前,屋大维也已经开始尝试把
自己的形象和阿波罗以及亚历山大联系在一起。在阿克提翁之战以
后,亚历山大看起来就更加适合于年纪尚轻的屋大维了。他是深受诸
神庇佑的东方征服者,他肆意地动用武力,他的伟大甚至令其跨越了
凡人和神明之间的分界线。
屋大维在亚历山大之城命人按照亚历山大的形象给自己塑造了一
些雕像,其中有一尊被称为密罗伊(Meroe..)头像,现藏于大英博物
馆。这尊头像就把屋大维塑造成了亚历山大。在绝大多数的肖像里,
亚历山大的脖子都会扭出一个比较大的角度,这大概是象征着他在遥
望神灵。而屋大维的密罗伊头像也扭了类似的角度。此外,其发型也
和亚历山大的标准发型相似,虽然稍短了一些。我们或许可以推断,
屋大维在埃及人面前就是以这种形象出现的,他用这些肖像把自己描
绘成了新的亚历山大。
身处亚历山大之城的屋大维还造访了亚历山大的陵墓。当然,这
也是托勒密诸王的墓穴。屋大维命人取来了遗体,然后打开石棺,以
便审视亚历山大的面庞。他给亚历山大的遗体戴上了金冠,然后为他
献上了散落的花瓣。不过,亚历山大毕竟已经死了将近三百年了,就
算是有最好的防腐手段,他的遗体也难免变得非常脆弱。因此,新的
亚历山大把旧的亚历山大的鼻子给碰掉了一块。这幅景象或许让亚历
山大之城的居民倍感紧张,这可是他们最宝贵的君王遗体。于是,他
们询问屋大维是否想要看一看托勒密诸王的尸体。对此,屋大维表
示,他想要看的只是国王,而不是尸体。[341]这个说法很有意思,所
以他后来又用了一次。有人问他是否要去看一看公牛神阿匹斯(埃及人
会用动物来表现神灵,这在古典时代堪称独树一帜),屋大维的回答
是,他通常只会膜拜神明,而不是牲畜。
第三个不毁灭亚历山大城的理由是屋大维和阿雷欧斯(Areios)之
间的友谊。当时的大多数罗马贵族都通晓希腊文化。而且,从公元前2
世纪中叶或更早一些的时候开始,罗马人还特别欢迎希腊的哲学家来
访,以至于营造出一种独特的贵族文化氛围。哲学家们常常受邀与罗
马的权贵为伴,到意大利南部越建越多的豪宅别墅里参加学术讨论。
拥有一个过从甚密的哲学家已经成了精英地位的标志,就好像拥有别
致的庭院、希腊(或希腊式)雕像和文雅的谈吐一样。因此,我们毫不
意外地发现屋大维和亚历山大的哲学家阿雷欧斯相识。此外,这种现
象还提醒了我们不应把这个时代的文化和冲突理解为近现代的民族国
家之间的概念。在阿雷欧斯的影响下,亚历山大的居民窥见了屋大维
的学术修养,得知他珍视希腊的教育和文化。一言以蔽之,他不是一
个野蛮的征服者。
屋大维还对亚历山大人民发表了演说,亲自解释了这一点,虽然
听众大概在之前就已经有所耳闻。屋大维在演说时非常罕见地使用了
希腊语。征战四方的罗马人(和历史上其他的征服者一样)向来致力于
让被征服者学习自己的语言,他们一般会用拉丁语对战败者讲话。然
而,此时的屋大维不仅对亚历山大的哲学家阿雷欧斯示以尊重,还使
用了希腊语对亚历山大人民发言。由此,屋大维发出了一个鲜明的信
号:希腊人可以与他和谐共处。这其实是亚历山大大帝的传统,希腊
人对此很熟悉。
屋大维迅速地接手了埃及统治者的既有传统。虽然他也许说过自
己不会膜拜牲畜,但是在上埃及地区的布奇斯(Buchis)神庙里,我们
可以看见有关于屋大维膜拜公牛神布奇斯的史料。而且,这份史料是
一系列铭文的一部分,它们都描写了埃及的统治者在向传承逾千年的
诸神献上祭品。也就是说,屋大维不仅把罗马的资金投入了埃及的神
庙和祭坛里,他本人还在神庙的铭文里得到了法老一样的待遇。埃及
的小城市俄克喜林库斯(Oxyrhynchus)有一份来自“恺撒元年”(公元
前30年或公元前29年)的文档,显示当地的某个神庙里有四个点灯人在
起誓为神庙效劳的时候提到了“身为神以及神子的恺撒”。[342]自尤
里乌斯·恺撒成神以来,屋大维就一直在使用类似的头衔。他在货币
上的称谓是“神子恺撒”(CAESAR DIVI FILIVS)。俄克喜林库斯的这
些点灯人显然知道这一点,把这个头衔纳入了自己的誓言。但他们同
时还延续了埃及的传统,把屋大维本人也当作了神。
为了庆祝自己与亚历山大人民化干戈为玉帛,屋大维给这座城市注入了一大笔建设资金。有关此事的最佳史料来自罗马,而不是接受资助的亚历山大。今天,梵蒂冈的圣彼得广场中央屹立着一座方尖碑,而这座方尖碑原本和其他的方尖碑一起在埃及的赫利俄波利斯(Heliopolis,太阳之城)伫立了许多个世纪。这是人们献给太阳的礼物。后来,人们把它迁到了亚历山大。然后,大概在卡里古拉皇帝的命令下,这座方尖碑来到了罗马。最终,又过了很长的一段时间以后,它才在圣彼得广场中央安家落户,挺立至今。在对这座碑加以考察之后,人们发现这座方尖碑上有一些原本镶嵌着铜字的槽。这段铭文的内容大概是:
奉皇帝、神子恺撒之令,工程长官(Praefectus Fabrum)、格奈乌斯之子盖乌斯·科涅利乌斯·伽卢斯建造了这座尤里乌斯广场。
科涅利乌斯·伽卢斯就是之前受安东尼之命去镇守昔兰尼加,接着反而率军在公元前30年从西边进攻埃及,帮助屋大维引走了安东尼的兵力之人。我们稍后还会提及他的事情。
亚历山大的尤里乌斯广场大概建于公元前30—前29年。当时,亚
历山大得到了大规模的改建,尤里乌斯广场就是其中的核心项目。此
外,恺撒庙(Caesareum)也是兴建于此时的标志性建筑,虽然建造这座
庙宇本来或许是克莱奥帕特拉的意思,因为尤里乌斯·恺撒毕竟是她
的情人,也是恺撒里昂的生父。亚历山大的恺撒庙和屋大维在罗马建
造的尤里乌斯神庙(Temple of Divus Julius)形成了遥相辉映的一
对。不过,埃及的这座恺撒庙会成为供奉每一位恺撒的庙宇,把成神
的尤里乌斯·恺撒和他的继承人都囊括在内。
屋大维走在了人和神之间的分界线上,他的这种做法利用了东方
人神化统治者的传统。埃及人对法老的膜拜自不必说,其他希腊化的
东方国度大多也有类似的习俗。而且,罗马的宗教传统里其实也有相
像之处。罗马的建城始祖罗慕路斯和埃涅阿斯都被尊为神明。不久前
成神的尤里乌斯·恺撒则复苏了这种传统。所以,俄克喜林库斯的那
几位点灯人不是奇怪的泥古之人。他们不是没能理解新来统治埃及的
罗马政权,也不是不懂罗马人的异国习俗,而是遵循了屋大维的意
愿,将他奉为新诞生的神明恺撒。
公元前30年末或者公元前29年初,屋大维开始返回罗马。他没有
直接航向罗马,而是选择了环地中海而行。小亚细亚半岛上的各个城
镇纷纷派出使者来拜见屋大维。以弗所(Ephesus)和尼西亚(Nicaea)人
民请求获许把神庙献给罗马女神(Roma,象征着罗马城)和尤里乌斯·
恺撒。帕加马(Pergamum)和尼科米底亚(Nicomedia)人民恳请把他们的
庙宇献给屋大维本人(可能还有罗马女神)。帕加马还获许举办赞美屋
大维的运动赛事。之前也有人享受过这种近似于神的待遇,比如希腊
化时代的诸位国王以及某些罗马总督。但他们的规模都无法与屋大维
相提并论,也不像屋大维这样堂而皇之。[343]
对于在深厚的一神教传统滋养下成长起来的人而言,把一个人尊
奉为神看起来似乎没有什么道理,反而有点邪教的色彩。但对古典时
代的人来说,这是很正常的。他们向来相信人有可能成为神,最著名
的例子就是赫拉克勒斯。大多数人还相信诸神会时常造访人间,他们
认为每个人都有灵魂,而灵魂是有一定的神性的。埃及人更是认为法
老就是某个神圣的灵魂的化身。因此,法老仿佛就是神明。类似的思
想观念在近东地区盛行了许多个世纪:国王和神明之间有着特殊的关
系,而且这就是他们为王的原因。不过,尽管有着这些统治者崇拜思
想的铺垫,但像屋大维那样直接宣布自己有着神的属性乃至把自己当
作神明供奉起来还是极其罕见的。由此,屋大维表明了自己不同于之
前罗马政坛上的所有人物。
罗马人和东方人早就有了比较密切的交往,后者肯定已经很清楚
罗马的状况了。毕竟,罗马和希腊城邦的构造其实没有很大的差异,
统治罗马的无非就是由地位大致相等的贵族们组成的议会(元老院)。
然而,在安东尼彻底落败以后,各地的城市做出了前文所提的种种创
举。这说明它们已经认识到了一个无可争辩的事实:屋大维全然不同
于寻常的罗马元老。而且,他也不同于那些继亚历山大以后统治东方
的君王。屋大维独一无二。他是神。不过,虽然这些使者看起来纯粹
是东方的各城市议会自主派出的,但我们很难相信他们会不谋而合地
想到这种如出一辙的主意,还同样在这个时候派出了使者,也许他们
在暗中收到了指示。
看到整个东方都无比热切地向自己表达了忠心,权威得到确认的屋大维便满载着埃及的财富,渡过亚得里亚海回到了意大利。自阿克提翁之战以来,元老院有将近两年的时间来好好地准备迎接凯旋的屋大维。现在,元老们即将为他献上与其相称的隆重表彰。
庆功
在赞美屋大维这件事情上,元老们表现得特别积极。在阿克提翁
战役结束以及亚历山大陷落之后,元老们争先恐后地出台了一系列歌
功颂德的决议:他们表决同意为屋大维击败了克莱奥帕特拉而举办一
次凯旋仪式;布伦迪西翁是屋大维奔赴战场的起点,也是他凯旋的港
口,因此元老们决定在这座城市建造一座凯旋门,还要用战争中缴获
的武器来加以装点;罗马的广场上也要兴造一座凯旋门;尤里乌斯神
庙(或许尚未竣工)将被饰以在阿克提翁之战中缴获的敌舰的船首;每
五年还要举办一次歌颂屋大维的庆典,虽然其具体内容不明,不过,
这种节庆想来应该会有祷告、献祭、比赛(大概是角斗)和戏剧这些常
见的感谢神明的公共活动;屋大维的生日和他的捷报被公之于众的日
子都被定为感恩日(同样会有祭祀活动);元老们还宣布维斯塔贞女、
元老还有其他的罗马居民(包括儿童在内)都会前去大道上迎接屋大维
胜利返回罗马,元老院和人民将一起向屋大维表达深切的感激之情;
[344]亚历山大陷落的日子被定为幸运日,而且,亚历山大的居民必须
从那一天开始重新计历。显然,这象征着新时代的到来。
罗马的宪法有了一些微调,屋大维得到了保民官的一部分权力。这具有特别的象征意义,因为保民官是罗马平民的权益的捍卫者。此举相当于宣布他要成为平民的新的代言人。之后,在司法领域,屋大维将拥有最高的决定权;在宗教领域,祭司们在祈求神灵祝福罗马元老院和人民之时必须提及屋大维的名字。屋大维已经成了罗马的第三大组成部分。罗马当局甚至还宣布在所有的晚宴上都要准备一份专门献给屋大维的祭酒。这些都是史无前例的特殊荣誉。
公元前29年夏,屋大维回到了罗马,同时迎来了又一轮的荣誉加
身。赞颂诸神的圣歌里加入了屋大维的名字。他有权像参加凯旋仪式
一样头顶桂冠出席所有的节庆活动。他可以任意地指定神职人员加入
祭司团,无论当时是否有职位空缺。元老院还关闭了雅努斯神庙
(Janus)的大门,表示战争已经结束。[345]整个城市都来迎接屋大维凯
旋(虽然他事先声明了平民不必前来)。执政官献祭了公牛以庆祝他的
归来,这也是史无前例的宗教仪式。接着,屋大维对罗马人民发表了
讲话。他宣布每一个成年男子都可以得到四百赛的奖金,这个数额足
以让一个人安度整整一年。屋大维称赞了统率舰队立下大功的阿格里
帕,士兵们也得到了奖赏。屋大维还代表他当时年仅十二三岁的外甥
马尔凯卢斯向罗马城内的儿童发放了奖金,这是他第一次展露出想要
构建一个王朝的意图。屋大维没有收下意大利各地人民为他收集的金
币。但就算如此,罗马城也已有了无数的财富。除屋大维赠予罗马人
民的奖金以外,随他一同返乡的士兵们也带来了埃及的大量财宝。据
说,在他们返回以后,罗马城的利率从平时的百分之十二降到了百分
之四,物价也有所上涨。[346]
公元前28年,屋大维得到了“首席元老”(princeps senatus)的
地位,也就是元老院的第一人。这意味着在元老们商讨事宜的时候,
他的意见最为重要。“首席”(princeps)即“第一人”。这个称呼有
着比较悠久的历史。之前也曾有一些名望较高的元老被称为“首
席”,享有全国第一人的美誉。但当时这个称呼基本只是荣誉头衔,
不包含实权。到了后来,至迟在奥古斯都时代的末期,这个头衔才具
备了更加重要的意义。奥古斯都的地位其实是由各种权力和头衔拼凑
起来的,他没有某个统括一切的头衔。我们现在常常使用的“皇帝”
(emperor)这个词的原型只是罗马人对战功赫赫的将军(imperator)的
赞美之词而已,其最初的适用范围是很狭窄的。“元首”(princeps)
这个称呼算是以一种不太正规的方式表明了屋大维独特的显赫地位。
后来的罗马人使用的“principatus”(principate)这个词既可以指代
某个人领导国家的时期(“某某人时代”),也可以用来指代早期罗马
皇帝统治国家的制度(所谓的“元首制”)。[347]
然后,屋大维举办了凯旋仪式。他和他的部下在长达三天的时间
里游行于罗马城内各处。在此期间,他们既向诸神献上了祭品,也向
全城的居民展示了极其丰厚的战利品。第一天的凯旋仪式是为公元前
35—前34年的达尔马提亚战争而举办的。在此之前,屋大维一直无暇
以凯旋游行来庆祝这一次的胜利。第二天纪念的是阿克提翁之战。游
行队伍看起来还带上了描绘着此次胜利的巨幅宣传画。第三天则庆祝
了埃及战事的胜利。按照传统,这一天的重头戏本该是让戴上镣铐的
克莱奥帕特拉跟着游行队伍走遍全城。但既然埃及女王已经自杀,他
们只好用塑像来替代了。不过,她和安东尼所生的龙凤胎亚历山大·
赫利俄斯和克莱奥帕特拉·塞勒涅都在游行队伍里面。而她和恺撒所
生的儿子恺撒里昂当然已经死去。一般说来,俘虏都会在游行结束以
后遭到处决。但这一次,屋大维展现了仁慈之意。来自埃及的财宝也
被装在车里跟着游行队伍供所有人观赏。接着,屋大维本人乘着战车
游遍了全城。另一位执政官和诸位元老都跟在他的身后。[348]严格说
来,屋大维可能只举办了两天的凯旋仪式来纪念达尔马提亚和亚历山
大的战事,因为庆祝内战的胜利不是很光彩的事情,第二天的活动只
是游行而已。不过,这种细枝末节的事情似乎很快就被人遗忘了。
[349]屋大维的庆功活动还没有结束。他把一座庙宇献给了密涅瓦
(Minerva)。大概进行了好一阵子的元老院翻修工程现在已经结束,其
名称按照尤里乌斯·恺撒的名字被更改为尤里乌斯元老院(Curia
Iulia),时人想必也能看出其中的讽刺意味。元老院里还添置了一座
来自他林敦(Tarentum)[1]城的古老的木质胜利女神像,上面装点着来
自埃及的战利品。每当元老们召开会议之时,他们就会为胜利女神献
上祭酒,同时再度回忆起屋大维击败了安东尼。取自埃及的战利品有
很多被放在了古老的罗马城广场中心的尤里乌斯神庙里。此时,这座
庙宇已经完工且得到了祝圣。还有一些财宝被送至罗马城内最为古老
也最受尊崇的卡皮托里翁三神庙—供奉着朱庇特(Jupiter)、朱诺
(Juno)和密涅瓦。
屋大维还在庆祝胜利的运动赛事上大肆挥霍。各种家养或野生的动物都被送入竞技场遭到屠杀,其中包括罗马居民从未见识过的一只河马和一只犀牛。罗马贵族们亲自走上了跑马场进行比赛,甚至有一位元老参加了角斗。在屋大维的命令下,来自苏维汇(Suebi,日耳曼人)和达契亚(Dacia,多瑙河以北)的俘虏之间展开了一场战斗。[350]屋大维还发明了一种叫作“特洛伊游戏”(Lusus Troiae)的新型赛事,让贵族青年比拼马上的功夫。
节庆、建筑、运动赛事、凯旋游行、各种形式的荣誉,还有发放给全体罗马居民的奖金,这一系列庆功活动的规模都是史无前例的。在如此盛事的映衬下,所有人都能够明白屋大维东征归来是一个重大的历史事件。
这些庆功活动的背后其实别有深意。随着阿克提翁之战结束、安
东尼和克莱奥帕特拉死去,屋大维已经毫无疑问地成了罗马政坛的主
人。然而,谁也不知道他接下来会做什么事情。很多人都难免有些畏
惧,因为屋大维完全有可能像某些前人一样发动新一轮的清洗。元老
们表决同意向屋大维颁发种种特殊荣誉的原因与其说是对战胜者的感
激,不如说是深深的畏惧。他们极其迫切地想让屋大维看见自己的忠
心。与此同时,屋大维则以种种举动来安抚元老和罗马人民。其中,
象征意义最大的或许就是关闭雅努斯神庙的大门。依据传统,每当罗
马人民走向战争之时,这座神庙的大门就会被打开。鉴于罗马历史上
内外战争频发,在过去的几百年间,这些门其实很少有关上的机会。
但是关闭大门就象征着和平的新时代已经到来。我们不知道这个决定
究竟是由哪方做出的(也许经过了协商),但双方都愿意接受这个结
果,愿意以此来表示他们衷心地希望战争就此结束,所有人都能够回
归正常的和平年代。
不过,虽然战争或许真的结束了,但是过去的事情并没有被遗
忘。屋大维没有抛弃他的一贯政策。值得注意的是,为了巩固他和平
民的关系,屋大维大方地向罗马平民送出了巨额的奖金,让他们知道
屋大维确实是平民的保护者与大恩人。对于让罗马社会四分五裂的内
战,屋大维不仅不加掩饰,反而以各种手段来庆祝自己的胜利,不给
败者留丝毫的情面。凯旋仪式或许只能算是昙花一现,但今后长期存
在的感恩节庆日会一次又一次地把屋大维的胜利摆到人们的面前。罗
马城内的各种胜利纪念建筑和纪念品也会让人们永远铭记阿克提翁和
亚历山大的战事。更何况,元老们还颁布了法令,要求人们在私人宴
席上为屋大维准备祭酒。这条规定不一定能够强制落实,但它光是存
在就已经有了意义。我们大可以想象一下战死者的亲朋好友们面对这
条规定会作何感想。
在屋大维时代的罗马城,安东尼的踪影被抹去了一些,但人们依
然能够在很多场合感受到克莱奥帕特拉的存在,这让人不禁觉得有点
奇怪。各座建筑内摆放着的埃及工艺品以及展示于尤里乌斯神庙前的
船首都让人联想起这位埃及女王。各神庙里的埃及宝物也一边给庄严
的罗马圣地增添了光彩,一边彰显着克莱奥帕特拉的存在。诗人们依
旧公然传颂着她的故事。最为关键的是,以克莱奥帕特拉为模型的维
纳斯金像依然保留在恺撒建造的维纳斯母神庙内。所有人都知道,当
他们过来瞻仰维纳斯女神的仪容之时,他们看到的其实是克莱奥帕特
拉,她不会为人们所遗忘。屋大维需要克莱奥帕特拉在帝国政权的宣
传当中扮演一个重要的反面角色,帮助屋大维在多年以后把他的政权
塑造得正气凛然。
当然,尽管克莱奥帕特拉没有淡出罗马人的视野,但屋大维显然
更是无比突出的存在。他获得了很多宗教方面的荣誉,让罗马人不仅
要在圣歌中赞颂他,还要为他献上祭品。屋大维在帕拉提翁山上为自
己建造了一座新居,还令其和旁边新建成的阿波罗神庙构成了一个整
体。阿波罗是受屋大维偏爱的神祇,阿克提翁之战的胜利就被他归功
于阿波罗。公元前28年,这座阿波罗神庙在盛誉之下开放了。[351]这
些挺立于山坡之上的白色大理石柱本身就是了不起的胜利纪念品,它
们为阿波罗提供了新的安身之所。维斯塔神庙也加入了这片建筑群。
我们不难想到,屋大维的本意或许就是让人觉得有三位神明共居于帕
拉提翁—阿波罗、维斯塔还有屋大维。
在战神广场上,阿格里帕正在建造一座宏伟的新神庙—万神殿。在公元前27年,阿格里帕第三次担任执政官之时,这座神殿举办了落成典礼。他们的初案是让屋大维的雕像屹立在万神殿的中心。那样一来,万神殿就会成为供奉着活人的庙宇。显而易见,他们就是想让罗马人把这位年轻的罗马之主看作神。除万神殿里的计划以外,屋大维的密友和罗马人民还已经用铸造神像的黄金和白银在罗马城内竖立了一些屋大维的雕像。[352]
罗马共和国属于罗马公民,其政治文化强调的是平等。当然,他
们的平等在现代人眼里难免显得有些古怪:国家领导人享受着“更加
平等”的地位;全国的居民被划分为三六九等。但罗马共和国至少还
承认理论上的平等,身为全国之精英的元老就是这种观念的最佳代
表。无论他们内部有着多么巨大的分歧、何等激烈的竞争,他们基本
上都认为元老之间理应彼此尊重,认可他人的成就,互相建言,携手
并进,一起为罗马而努力。共和国时代确实有伟人诞生,个别人似乎
还太伟大了一些。但是,就连马略、苏拉、庞培乃至恺撒都无法与屋
大维相提并论。屋大维是非常特别的,他的超然地位让其他的罗马人
不得不煞费苦心地去寻找一种合适的政治语言来加以描述。所以,我
们大概可以理解他们为什么要把屋大维奉为神明,而屋大维又为什么
要尝试着把自己塑造为人间之神。在神的面前,共和国的基本框架自
然就失去了意义,没有人能够和神并驾齐驱,平等是不可能的。
但是,和神共处并非易事,当人间之神也会遇到不小的麻烦,后来的卡里古拉皇帝就是例子。所以,公元前28年和公元前27年,屋大维开始调整自己的名分。万神殿成了供奉所有神明的庙宇。屋大维的雕像被放在了入口处,而不是中央。身为万神殿建造者的阿格里帕也得到了一座雕像。至于屋大维的金银雕像,它们都被熔掉,然后铸成了货币。至此,在阿克提翁之战以后一度被屋大维采用,并且在他巡视东方之时仍然受到重视的神化计划就这样突然消失了。
屋大维需要一个更加合适的新形象。他一边寻找政治伙伴(虽然起
初可能只有阿格里帕),一边考虑传统的问题。他开始对共和国的平等
理念示以尊重。我们很难想象他会自愿地做出这种改变。他当然已经
取得了无数次的胜利,整个罗马都唯他是从,胆敢挑战者大多已死。
他还用各种各样的纪念建筑、物品、仪式来不停地彰显自己的权威,
改变罗马的面貌。但是,屋大维遇到了阻力,并非所有人都像官方公
告里声明的那样对这位新的恺撒充满了感激之情,他必须妥善解决自
己的前途问题。三头同盟已亡,安东尼和李必达都已死去。或许,他
可以让罗马继续处于紧急状态之下,假装他还在为恢复共和国而战,
从而继续把持着莫大的权力。但这种做法未免太过拙劣。于是,为了
在正常时期保持着既有的特殊地位,屋大维必须建立一种新秩序。公
元前28年,屋大维陷入了前人在内乱之后所遇到的那种困境。几乎别
无选择的屋大维似乎不得不恢复旧时代的制度。在经历了这些年的动
荡以后,共和国显然已经死去,但现在,它仿佛还能死灰复燃。
共和国复苏
即便是在公元前30年,屋大维也还面临着反对派的威胁。假如是
在几年以前,元老院里或许就会有反对的声音,某些知名政治人物可
能还会离开罗马,以此表明自己的反对态度。但到了这个时候,屋大
维的反对者只能隐秘行事了。从表面上看,此时的罗马政界无比团
结,所有人都对屋大维一片丹心;但事实上,没有人会被这种假象欺
骗。当然,在这种政治环境下分辨异己是比较困难的。其中或许有一
些人敢于直抒胸臆(虽然没有被记录下来),但是大多数人都披着伪
装,只在某些时候趁机给屋大维政权使绊子。我们只能借助于蛛丝马
迹,隐约地看见屋大维的新政权和反对者们展开了争论和交易,以求
排除道路上的阻碍,但我们几乎看不到足以牵动全局的重大事件。
大约在公元前30年,马尔库斯·李必达被除掉了。据说,他和布
鲁图斯的姐妹尤妮亚密谋在恺撒返回罗马之时行刺。尤妮亚的身份使
得这个据说存在的密谋和当初的那些行刺者联系在了一起,让人觉得
有人想要再为罗马除去一个暴君。这位李必达的父亲就是三头之一的
那位马尔库斯·李必达。自从屋大维在公元前36年夺走他的军权以
后,仅保留最高祭司一职的李必达就过上了流放的生活。屋大维似乎
经常对李必达加以羞辱,一直到他约在公元前12年去世为止。[353]小
李必达是个比较有声望的政治人物,他或许不满于自己的父亲所受的
待遇。而尤妮亚虽然是一介女流,但她的家族背景和旧日的人脉让她
有了一定的影响力。在屋大维派驻于罗马的代表麦奇纳斯(Maecenas)
发现了阴谋以后,李必达大概甚至都没有经过审讯就遭到了处死,尤
妮亚则结局不明。[354]
第二个事件比较复杂。公元前30年或公元前29年,罗马将军马尔
库斯·李奇尼乌斯·克拉苏在马其顿作战。这位克拉苏是那位著名的
庞培和恺撒的盟友克拉苏的同名孙子,与他敌对的是某些异族部落—
巴斯塔奈人(Bastarnae)、默西亚人(Moesians)和吉泰人。在和巴斯塔
奈人交战之时,身为将领的克拉苏罕见地亲自上阵,还杀死了巴斯塔
奈之王戴尔多(Deldo)。这几乎堪称罗马人前所未有的壮举。克拉苏有
资格凭此得到一项特殊的荣誉—“丰获”(spolia opima),而屋大维
对此加以阻挠。
屋大维利用了一个程序上的问题。克拉苏是被屋大维派去马其顿
的,严格说来,他只是屋大维的代表。于是,屋大维声称只有独立掌
握军权者才有资格得到“丰获”。听闻此言,人们连忙去遍稽群籍,
然后找出了一个史例。在浩如烟海的罗马传说故事当中,有一个叫作
科苏斯(Cossus)的人曾经被授以“丰获”,所有相关资料都显示科苏
斯当时是一位保民官,受制于另一位高级官员。但是,有一次,屋大
维正在监督朱庇特·菲利特里乌斯神庙(Temple of Jupiter
Feretrius)的修复工作(据说,科苏斯当年就是把“丰获”献到了这座
神庙里),就在工程进行之时,人们发现了一块亚麻布。上面的文字显
示,科苏斯是在他担任执政官期间献出“丰获”的。想必很少有人会
相信这么一份内容正合屋大维所愿的史料只是恰巧在这个时候出现,
至少身为史家的李维(Livy)是不相信的。然而,没有人能够指责屋大
维捏造文本。[355]
这个故事里的屋大维看起来未免有些患得患失,他不希望让身为
贵族子弟的克拉苏得到一个连他也未曾拥有的特殊荣誉。显而易见,
克拉苏既不是屋大维的反对者,也不可能拥有足以挑战他的实力。克
拉苏的军权来源于屋大维的信任,他的职位也是由屋大维亲自指定
的。但就算如此,屋大维也不能容忍他来妨碍自己垄断所有的荣誉。
公元前28年,屋大维开始把自己的特殊地位化作罗马政治的常
态。这一年,屋大维和阿格里帕一同担任执政官。之前,在处于紧急
状态下的公元前31年、公元前30年和公元前29年,屋大维也都担任执
政官。当时的他几乎一直身处海外,留在罗马的另一位执政官不得不
独自管理这座城市。然而,在返回罗马以后,屋大维似乎基本上无视
了同僚的存在。每位执政官原本都有三十名扈从,他们手执法西斯(棍
棒和斧子的组合),以此代表执政官拥有惩戒罗马公民的权威。但是,
自从公元前31年屋大维开始连任执政官以来,他执意要求所有的扈从
都随他出行。两位执政官本应是共掌权力的同僚,而屋大维的这种做
法直观地反映了这种理想状态的消亡。而且,这是他有意为之的象征
性举动,其意义就是展示他大权独揽的地位。不过,在公元前28年,
他改变了主意。
六十名扈从不再全部跟随着屋大维,古老的习俗得到了恢复。阿格里帕在公元前28年和公元前27年都与屋大维并列为执政官,并且正常地享有三十名扈从。其实,从宪法和法律的角度来看,扈从分配的恢复没有什么值得一提的意义。然而,这是一个标志,意味着罗马政治往正常的状态迈出了重要的一步。在公元前28年的某个时间点上,屋大维正式宣布持续了十余年的紧急状态就此结束。[356]
严格说来,这次的国家紧急状态和三头同盟挂钩。他们三人理应只是为了重建共和国才接受极大的权力的。一旦三头同盟消亡,紧急状态的法律依据也就变得含糊不清。人们很难说清楚现在仍处于紧急状态的原因是屋大维以执政官的权力下达了命令,还是元老院颁布了对抗安东尼的法令。不过,看起来也没有什么人真的在乎这种事情。但是,在公元前28年,屋大维决定着手结束紧急状态了,公民的权利得到了恢复,屋大维还专门铸造了纪念此事的金币(请参考图6)。金币上刻画的屋大维脚边有一盒卷轴,他正在把其中的一份交给一位感激不已的公民。金币的一面印着“皇帝·恺撒神子·执政官·第六次”(IMP·CAESAR DIVI·F·COS·Ⅵ),另一面则是“他恢复了罗马人民的法律和权利”。同为执政官、积极参与政事的阿格里帕根本没有被提及。屋大维依然没有准备好让其他人也和他一样走上台前,就算是最受他信赖的阿格里帕也不行。不过,至少正常的法律得到了恢复。这就意味着再也不会有不经审判而处死公民以及没收公民财产的事情了。战争结束了,三头同盟的使命想必已经完成。
公元14年,屋大维给罗马人民留下的遗言—《圣奥古斯都行述》(Res Gestae Divi Augusti)—在他亡故以后面世了。这位开创了帝国时代的首位罗马皇帝对自己的一生做出了这样的结论:
在我第六次和第七次担任执政官期间,内战之火已然熄灭,全国一致听我号令。于是,我把共和国还给了罗马元老院和人民。[357]
屋大维和阿格里帕首先需要确认共和国现在有条件自行处理各项事务。他们开展了人口普查(结果为四百零六万三千名公民),[358]为罗马人民举办了一次净化仪式,还整顿了元老的队伍。
公元前28年的元老人数或许超过了一千,其中有一部分人还是按照传统途径从低级官员开始逐步升入元老院的。但还有不少人在恺撒或者三头同盟执政时期得到了提携,直接成了元老。屋大维公开表示要审查元老们的资格,并且希望有人能够主动让位。无论原因如何,有一些人确实很配合。接着,屋大维和阿格里帕要求元老们互相担保彼此都有资格继续担任元老。他们希望某些人会因此感到尴尬,进而主动辞职。最后,屋大维和阿格里帕亲自审视了剩下来的元老,除去了一些他们觉得不合格的人。
这一套流程的设计是为了让这件事情看起来不那么偏颇,但还是难以避免地引发了争论。被迫离开元老院的人深感不满。据说,屋大维一度要穿着胸铠、在十位密友的保护下去主持元老院会议。离去的那些人其实很多是当初为恺撒或者屋大维效劳才成为元老的,屋大维现在的做法相当于背叛了他们。[359]但屋大维和阿格里帕依然认为有必要让元老院恢复一定的威望,为此,他们已经准备好牺牲一部分追随者。
公元前27年1月,屋大维来到了元老院。他交出了执政官的职位,然后依照罗马传统,宣誓声称自己在任期内处事公正、谨遵法律。在此之前,他从未遵守这个传统,因为当时的他不受法律的约束。随后,在刚刚恢复了地位的元老们面前,屋大维第七次受任为执政官。他的同僚阿格里帕则是第三次。
1月13日,屋大维对元老们发表了讲话。这是一个非常关键的历史
时刻。根据现存的史料,此次讲话标志着罗马政治正常化的进程已经
步入了最后一个阶段。屋大维交出了地方省份的控制权,元老院和人
民能够决定地方总督的人选了。这一步同时意味着屋大维放弃了手中
的庞大军队和巨额的财富。为此,元老们给屋大维颁发了新的荣誉。
他的新居会被饰以橡树叶冠,得到这项荣誉的通常是拯救了罗马公民
的性命之人。而他的门旁会种上月桂树,这是阿波罗和胜利的象征
物。元老院里还会摆放一块金色的盾牌,宣示屋大维身上最为根本的
四项美德:勇(virtus)、仁(clementia)、义(iustitia)、忠
(pietas)。[360]
这次事件几乎必定早在屋大维的计划之内。为了这一天的到来,
他和阿格里帕已经做了至少一年的准备。不过,这还不是最终的安
排,还有一些事情尚未解决。三天以后,元老们再度相会。这一次,
他们展开了更加详细的讨论。最后的结果是,屋大维有权控制西班牙
的绝大部分地区、高卢、日耳曼尼亚、叙利亚、塞浦路斯、埃及、腓
尼基(Phoenice,叙利亚沿海地区和黎巴嫩)和奇里乞亚。除了马其
顿、达尔马提亚和阿非利加(今天的突尼斯)以外,这些由屋大维掌控
的省份已经包括了所有时常面临军事威胁的地方。之后,元老们又给
屋大维颁发了一项殊荣—他们让屋大维有了一个全新的名字。这一年1
月16日,以奥克塔维乌斯之名出生、以恺撒之名立业的那个男孩成了
奥古斯都。[361]
从公元前28年开始,到公元前27年1月最终协议的出台,屋大维成
功地重塑了自己的权力。三头同盟时代的特殊权力被他抛到了一边,
元老院得到了改革,法律的权威得以恢复,共和制度全面复苏,屋大
维认可并恢复了元老院和人民的最高权威,元老院则报之以无上的荣
誉。然而,我们还是能够察觉到奇怪的地方,没有任何迹象表明刚刚
得名的奥古斯都会离开政坛。他仍旧是地位超然的政治人物,统治着
无比广大的领土。他依然担任着执政官的职位,并且会不间断地担任
到公元前23年6月为止。
从古典时代开始,包括史家卡西乌斯·狄奥在内的很多后人都把
公元前27年1月庆祝共和国恢复的元老院会议视作帝国诞生的标志。
[362]不过,狄奥也看到了其中的矛盾之处。现实往往是复杂、混乱
的,政治就是如此。共和国的恢复确实意味着传统的政治运作方式又
回到了罗马,但罗马的政治精英们还得再花十年乃至更久的时间来掌
握如何在一个自相矛盾的政局里行事—重新确立的共和制度与一个拥
有巨大权威的人物并存。公元前27年1月,罗马人创制了奥古斯都。接
下来,他们还须切身体会这件事情的意义。
[1] 即今天的塔兰托(Taranto)。—译者注
第十三章 奥古斯都的诞生
[339] Josephus, Antiquitates , 15.6.约瑟夫斯的记录很详细,但某些
内容有可能是他编造的。
[340] Suetonius, Caesar , 7; Plutarch, Life of Caesar , 11.
[341] Dio, 51.16; Suetonius, Augustus , 18.
[342] P. Oxy . 1453.
[343] Dio, 51.20-21.
[344] Dio, 51.19.狄奥的文字看起来像是在引用罗马的官方布告。
[345] Dio, 51.20.
[346] Dio, 51.21.
[347] Dio, 55.9. Res Gestae , 14; Res Gestae , 7. Res Gestae ,
13有奥古斯都本人运用“元首”(princeps)这个词的实例。
[348] Dio, 51.21.
[349] Fasti Triumphales Barberini记载了古典时代举办的历次凯旋仪
式,其中有公元前 29年8月13日和8月15日纪念达尔马提亚和埃及战事的凯旋仪
式,却未曾提及有关阿克提翁的凯旋仪式。
[350] Dio, 51.22.
[351] Dio, 53.1; Propertius, 2.31.
[352] Dio, 53.22; 53.27.
[353] Res Gestae , 10; Dio, 54.27;也可参考54.15。
[354] Velleius Paterculus, 2.88.
[355] Livy, 4.20; Dio, 51.23-37.
[356] Dio, 53.2.
[357] Res Gestae , 34.
[358] 罗马人之前所做的普查只统计男性人口。而屋大维和阿格里帕的这次很可能有一些调整,其具体情况尚无定论。不过,综合各方意见以后,我们大概可以说他们这次普查统计了女性人口,同时或许把儿童人数也计算在内。
[359] Dio, 52.42; Suetonius, Augustus , 35.
[360] Dio, 53.2-11; Res Gestae , 34; Ovid, Fasti , 1.589-90; Fasti Praenestini(January 13) .
[361] “奥古斯都”的含义大概是“尊敬的”,但这个词也有“增长”“壮大”的意思,暗示着奥古斯都会让罗马发展壮大。
[362] Dio, 53.17.
第十四章 奥古斯都的共和国
公元前27年1月16日,罗马元老们亲身经历了一个非同寻常的历史节点。也许,他们会深思自己究竟做了什么。这也难怪,因为在这三天时间里,他们一起见证了罗马政治传统的恢复、共和国的重生。然而,奥古斯都依旧是罗马政局里独一无二的角色。对于罗马传统政治文化而言,奥古斯都的存在就和他的养父当年一样格格不入。
从某个角度来看,这次达成的协议仿佛是历史的重现。在过去的
一百年里,共和国遭遇了许多次震动整个罗马的大危机,但在每次危
机以后,罗马的政治制度总是能够大致恢复为原来的模样。罗马政治
文化的核心要素是人民主权和贵族统治,罗马革命对这种秩序发起了
挑战。士兵们颠覆了共和国,以恐怖的手段对待贵族阶层,许多贵族
或是被杀或是被夺走了财产。在三头同盟时期,意大利地区的财富经
受了大规模的再分配,意大利的人口分布也随着老兵们入驻殖民地而
发生了重大的变化。时至公元前30年,屋大维已经成为一张巨大的政
治关系网络的中心人物。他由此控制了无数的资源,成为地中海世界
毋庸置疑的主人。
然而,就算奥古斯都已经是大权在握的统治者,他也还面临着具
体如何统治罗马的问题,他还是需要地主、贵族们来担任军官、祭
司、法官、市长和较低级的官员。他手中的确凝聚了莫大的权力,他
大概可以凭此扫除五百年共和国历史积攒下来的种种传统,然后从零
开始。但是,奥古斯都自己就是一个传统的罗马人,他也是在保守的
等级制度文化下成长起来的。罗马不仅指代着意大利半岛中部的那座
城市,还意味着那一套守旧的文化和传统,要扫除元老院和被元老们
奉为圭臬的传统,就势必要给罗马的古老秩序也画上一个句号。这也
就相当于抛弃罗马的光辉历史,建立另一座全新的城市。严格说来,
创造一个全新的罗马并不是完全不可设想的事情。但是,安东尼或许
就是前车之鉴。公元前1世纪的罗马是一个超级大国的政治、文化、宗
教、经济中心,像安东尼那样转而以亚历山大为首同样不是不可设想
的事情,却非常难以实现,有些人大概就是因此才选择了对抗安东
尼。
不过,罗马的政治精英们未必会一味地因循守旧。除了罗马本身
的历史以外,他们还能借鉴于希腊世界里各种各样的城邦、联盟、王
国。虽然未免有些雾里看花之嫌,但是罗马人确实对别国的政治传统
有所了解,还有可能在某些情况下加以效仿。如前文所述,奥古斯都
曾经尝试着把自己的形象塑造成神。他参考了君主制的埃及、波斯和
希腊化诸王国,仿照了它们神化统治者的传统。但他最终效仿出来的
结果非常新颖,具备罗马的特色,不同于这些君主国,甚至还发展出
一套独特的意识形态和社会结构。罗马的君主有着更加强大也更加血
腥的权威,他们受到的约束较少。而且,罗马的君主制在很大程度上
违背了传统。公元前27年,在罗马城的中心,奥古斯都的周围是这座
城市的各个纪念建筑,它们就像是传统的化身。奥古斯都的面前则是
身着紫边白底托加袍的列位元老以及古老的神殿和诸神。此时的奥古
斯都是否已经大胆地设想出一整套全新的罗马之道了呢?
极少有史料能够表明奥古斯都是一位卓有创见的思想家。古代的
史家喜欢想象奥古斯都为属于他的全新国家设计未来蓝图的景象,甚
至还会把他最亲近的顾问阿格里帕和麦奇纳斯也加进来,设想他们在
一起抽象地讨论着该如何治理罗马。然而,奥古斯都很可能并不是一
位高瞻远瞩的政治制度设计师。他和其他的绝大多数革命者一样,深
受过往历史的束缚,常常试图从过去汲取智慧,用以解决当下的问
题。他和其他的绝大多数政治人物一样,忙于应付眼前的麻烦,通常
只能就特定的问题找到特定的解决办法。而罗马人则和其他民族一样
需要在政治生活中体会到安全感。在动荡的时期,他们需要得到安
抚。革命会造成很多问题,因为整个世界都会因革命而变得上下颠
倒,让人们难以用传统来指导自己的社会、政治生活。人民需要安
定,但只有他们所能理解的社会、政治秩序才能让他们感觉到安定。
也就是说,他们需要一套熟悉的秩序。奥古斯都承诺过要为罗马人民
带来和平,但光凭内战的结束(以雅努斯神庙大门的关闭和凯旋仪式的
举办为标志)还不足以实现真正的和平,奥古斯都必须让社会秩序稳定
下来。
但是,公元前28年和公元前27年的罗马政局显然有着内在的矛盾
之处。奥古斯都遇到的是根深蒂固、干系重大的全新问题,他不能选
择忽视,因为这些问题不会自行消失。在这些问题的影响下,罗马政
治的模式不得不改变,罗马人不得不经历一场革命。罗马革命纯粹是
实事求是的结果。它不是在某个伟大的乌托邦理想的引导下产生的,
其根源就是罗马社会内部的政治斗争。军队摧毁了元老们的权力,为
三头同盟的掌权做好了铺垫。而包括后三头同盟在内,所有的政治领
导人都必须处理好两件事—如何满足追随者的需要、如何维持住自己
的权威。正是为了解决这种极其现实的问题,安东尼和屋大维才采用
了有别于罗马传统的方式来宣传自己的权力和统治。因此,尽管安东
尼和屋大维之间的确有着不少的差异,但他们身上的相似之处更是多
得引人注目。
然而,渐渐地,屋大维还是转向了比较保守的做法,恢复旧貌成
了他所建立的新政权的核心。不论是重建神庙、政治机关,还是重塑
道德风气,奥古斯都把自己塑造为保守的政治文化的代表。差不多自
屋大维得名奥古斯都开始,就有一些保守的思想家倾向于仅从表面上
看待奥古斯都的所作所为,把屋大维的新名字看作新时代的标志,把
保守的奥古斯都政权和屋大维时代的暴力统治割裂开来。如果以鼓吹
道德教化的保守观点来看,我们很容易忽视奥古斯都政权的矛盾之
处。奥古斯都或许确实说着传统的话语,以传统的方式统治着罗马,
但他本人的存在、他在罗马政治当中的核心地位、他的一言一行显示
出的莫大权力都全然违背了罗马的传统。现代的历史学家们有时候似
乎忘记了奥古斯都的过去,忘记了他的权力基础,反而专注于他巩固
了地位以后的举动。但是,当时的罗马人恐怕不会这样健忘。
公元前28年和公元前27年的共和国的恢复只是屋大维新出台的保
守政策的第一阶段。为了让旧时代的政治文化复苏,屋大维必须同时
恢复元老院的权威,因为这一整套制度的正常运转是离不开元老院
的。他们是执政官的顾问和后盾,为执政官的行为赋予了道德的力
量,而要让元老们发挥出这个作用就必须先让元老院具有权威。但
是,让元老们重获权力又难免会导致奥古斯都的地位遭遇质疑。于
是,虽然奥古斯都政权有必要恢复元老们的权力,但这件事的最大阻
碍恰恰是奥古斯都本人的权力。
影响奥古斯都政权立足的最大难题就是这个矛盾,奥古斯都必须
妥善地解决自己的地位问题。他现在拥有的权势就算纵观罗马历史也
无出其右者,但他无意像苏拉那样在复古改革完成以后急流勇退。在
公元前28年1月,屋大维的统治依据是紧急状态下虽然不明晰但毋庸置
疑的莫大权力。当然,屋大维的权力归根结底来自听命于他的强大军
队和平民大众对他的支持。但紧急状态的存在让他合法地掌握了凌驾
于法律之上的权力,虽然他在运用这种权力之时还是利用了执政官的
传统身份。然而,在他宣布紧急状态结束之后,这种权力就显得不合
时宜了。异乎寻常的权力总是难以在正常时期找到存在的依据,这是
个让很多独裁政权都困扰不已的问题。因此,在开启奥古斯都时代的
过程当中,屋大维抛弃了这种权力。不过,奥古斯都的权力本就不依
赖于法律的认可,他的根基是金钱和暴力。这种宪法层面上的调整几
乎不会影响到他的实权。
法律是为政权提供统治正当性的一种传统手段。但既然法律无能
为力,奥古斯都政权就把自己的统治正当性的来源解释为人们对奥古
斯都的一些个人品质的尊重。换言之,他正是凭着这些个人品质才打
破了元老之间人人平等的惯例,成为超群绝伦的存在。我们必须带着
这种观点去看待元老院颁发给奥古斯都的荣誉:其宅邸的特殊标志、
他和神明的联系、元老院里的那个赞颂其美德的金色盾牌。奥古斯都
本人也对这种变化做出了解释。他声称在公元前27年以后,他的权力
和其他官员是相等的,他胜于旁人的地方不在官职,而在于他的“权
威”(auctoritas)。[363]“权威”既是政治属性,也是个人属性。奥
古斯都的统治依据从三头同盟时代合法取得的违法权力变成了他凭着
自己的优异品质而获得的个人权威。
奥古斯都的统治经由多年连任执政官而得到了巩固。执政官的连
任并不是什么新鲜事,最著名的例子大概就是马略,他在公元前2世纪
末多次连任执政官。但是,之前的例子都是为了应对危机才出现的,
马略得以连任是因为国家需要他凭着出众的能力和声望来解决国家的
危机。而在公元前27年,我们很难说罗马遇到了什么威胁。奥古斯都
连任执政官的理由看起来似乎不太充分,他在紧急状态结束以后继续
统治罗马的理由只能是他具备了特别优秀的道德品质和领导才能。但
是,元老治国的核心就是分享官职以及让元老们(在同一等级内)保持
平等。因此,奥古斯都依然是让元老们头疼的异常存在。
不过,把政治个人化还造成了一些别的影响。既然奥古斯都拥有
的是个人的道德权威,那么他就需要让人们看到他的道德约束力和领
导才能。因此,在整个奥古斯都时代,我们都能看到他在努力地以各
种方式展示这些与政治挂上了钩的个人品质。他的主要手段是在战场
上建功立业,但他也曾试图在宗教和家族领域显示领导能力。奥古斯
都时代的罗马新秩序需要严格的约束,需要剔除那些导致了百年动荡
的混乱因素,只有深刻的社会改革才能还罗马以和平。
但这种和平是有代价的,这是奥古斯都政权不愿让人了解的事情。奥古斯都政权的严格约束压制了共和国自古以来的自由。虽然听起来或许有些别扭,但一定程度上的混乱其实是民主(或伪民主)制度运行过程中不可或缺的组成部分。共和国时期的罗马政治本就是有些混乱的,竞选犹如战斗,精英之间时常爆发非常激烈的竞争。剔除旧制度当中的混乱因素等同于摧毁传统政治的一大支柱。罗马得到了和平与秩序,而代价就是失去自由,接受奥古斯都的统治。
属于军队的政权?
传统的罗马政治史偏爱讲述贵族之间的故事,但其他的政治力量同样不容小觑。元老们是在屋大维的胜利纪念品环绕下展开政务讨论的,他们每时每刻都能由此回忆起(虽然他们应该永远也忘不了)屋大维的敌人最终都落得怎样的下场。不过,最让他们噤若寒蝉的还是奥古斯都手中的军权。
奥古斯都受命掌控了许多地方省份,其中的绝大部分都驻扎着为
数众多的军队。让这样规模庞大的军队继续听从奥古斯都指挥的理由
是这些省份都频发战事,而奥古斯都既有崇高的威望又有充足的军事
经验。当然,他分身乏术,不可能直接指挥所有地方的军队,他会派
精心选出的亲信去代表他统率部队。不过,虽然有代表的存在,但奥
古斯都和阿格里帕还有后来奥古斯都家族里的核心角色都长期身处地
方省份,和军队待在一起。毕竟,这些军团是他们最重要的支持者。
总之,奥古斯都成功地维持住了对军队的掌控。
罗马军队有着巨大的人力需求。二十八个军团共十四万的罗马男
性需要离开意大利,去地中海世界的各个角落为国效力。而且,其时
限长达十六年。他们的报酬是定期发放的薪水和不定期发放的奖金,
虽然奖金后来也有了固定的发放规定。根据人口普查的结果,此时的
罗马公民总数为四百万出头。也就是说,罗马的人力有大约百分之十
一在军队里,这些人就是最直接受益于奥古斯都的统治的群体。而
且,在之前的内战结束以后,有不少的老兵退伍后拿到了殖民地里的
大量土地。这两部分军人相加就构成了一股人数众多、实力雄厚的势
力。
除了军团以外,奥古斯都还有别的部队。在公元前27年的最终协
定出台以后,他首先在意大利设立了一支卫队,其薪水是普通军团士
兵的两倍。这种卫队早有先例,共和国时代的将军们也曾设立过这种
部队。尤里乌斯·恺撒就有一支规模较大、发挥过许多作用的卫队。
而奥古斯都的卫队很可能有大约五千人,具备比较强的实力。虽然这
些卫兵大多被奥古斯都分别派往意大利的各座城市,留在罗马的人数
其实很少,但这毕竟是突破了共和国时代惯例的事情,一般的执政官
可不会有这样的直属军队。他们的存在非常直观地表明了奥古斯都的
权力究竟来自何方,同时也说明了军队仍然是罗马政局里相当重要的
一股力量。[364]
公元前27年1月的事件标志着罗马政治的程序恢复了正常,但罗马
政治本身已经发生了变化。罗马政治运转的方式和不少的政治文化都
保留了共和国时代的风貌,以贵族阶层的传统和价值观为核心。然
而,奥古斯都还牢牢地把持着大权。不过,这种矛盾的状态至少给政
治讨论提供了空间,因为奥古斯都政权需要遵守旧时代的规矩,以免
奥古斯都被当作独夫。但共和国时代的规矩显然不会允许有奥古斯都
这样独揽大权的人物存在。因此,在公元前27年1月,元老们并不确定
自己究竟促成了什么,也说不清新的政治秩序的本质。不过,就是这
种不确定为政治的发展留下了宝贵的空间。
共和国恢复以后的政治局面
公元前27年下半年,奥古斯都离开了罗马,准备开始治理他的省
份。他先去了高卢,打算入侵不列颠,[365]但这个计划因故被搁置
了。于是,奥古斯都转而在高卢展开了人口普查。这年末,他离开了
高卢,来到西班牙亲自指挥比利牛斯山区的战事,一直到公元前24
年。虽然在这期间,他都担任着执政官的职位,但他从未觉得有必要
返回意大利。[366]在这场战争结束以后,他让一部分军人退役,在西
班牙设立了一个殖民地。
在奥古斯都外出之时,意大利的事务看起来大多是由阿格里帕来
处理的。他正忙于在罗马的战神广场上兴造建筑,其重点项目是尤里
乌斯会堂(Saepta Julia)。这是罗马选民们集会表决法案、选举低级
官员的场所。在为会堂命名之时,阿格里帕没有使用自己的名字,而
是使用了奥古斯都的名字。同样在这一时期,阿格里帕建造了一座浴
场(罗马城内耗资最多的公共建筑之一)和一个被称为尼普顿大厅
(Basilica of Neptune)的建筑。这个尼普顿大厅里展示着纪念奥古斯
都海战胜利的画作。阿格里帕还主持了奥古斯都的女儿尤莉亚和奥古
斯都的外甥马尔凯卢斯的婚礼。此外,阿格里帕在他自己的居所遭遇
火灾以后,入住了奥古斯都在帕拉提翁山上建造的宅邸。阿格里帕不
只是奥古斯都的左右手,他还分享了奥古斯都的权力。奥古斯都的这
幢宅邸当然已经在公元前27年得到了元老院颁发的荣誉,但随着阿格
里帕的迁入,它看起来越发像是一座皇宫了。[367]
然而,奥古斯都等人面对的事情并不总是这么简单。大概在公元
前25年的时候,负责治理埃及的科涅利乌斯·伽卢斯因政治斗争而丧
命。当初,公元前30年下半年,屋大维在动身返回罗马之际任命他为
埃及总督。这或许是个合乎实际的决定,却引发了不小的争议。伽卢
斯恰巧是一位知名的诗人,但他不是元老,而是次一档的骑士。而一
般说来,像埃及这样规模较大、地位重要的省份都会由元老来管辖。
伽卢斯一度忙于管理刚刚成为罗马省份的埃及。他既要在埃及主
持建立罗马的统治秩序,还要前去镇压一场大规模的叛乱。到了公元
前29年4月15日,伽卢斯已经在命人制作纪念胜利的铭文。他自称在十
五天内制服了叛军,占领了五座城市,然后率军跨越了埃及的边界,
进入埃塞俄比亚,并且在当地建立了罗马的霸权地位。[368]伽卢斯的
总督生涯似乎非常成功。然而,他的敌人已经蠢蠢欲动。
一个叫作瓦列里乌斯·拉尔古斯(Valerius Largus)的人对伽卢斯
发起了控告,他提出的名目让人感到有些费解。他声称伽卢斯在埃及
竖立自己的雕像,还制造了吹捧他自己的铭文。这当然都有可能是真
的。但按照罗马法律,这种自吹自擂的行为很难称得上是犯罪。经过
一番争论,奥古斯都和伽卢斯决裂了。然后,伽卢斯又因一个含糊的
罪名而遭到了起诉,他的处境变得越发艰难。虽然看起来有些不可思
议,但这一回,据说伽卢斯在暗中策划革命。之后,他被定了罪,遭
到了流放,他的财产被转交给奥古斯都。接着,伽卢斯自杀了。据
悉,在听说伽卢斯的死讯时,奥古斯都流下了眼泪。考虑到他一生中
明明杀人如麻,这种动情的表现让人不禁感到有些意外。
成功除掉了伽卢斯的瓦列里乌斯·拉尔古斯并没有享受到多少的
喜悦。有一次,有一个人带着一个书写板,在一堆朋友的陪伴下靠近
了拉尔古斯,然后问他是否认识自己。拉尔古斯表示他不认识。然
后,这个人就叫他的那一群朋友都过来见证拉尔古斯的回答。此外,
有一个名为普罗库莱乌斯(Proculeius)的人也有类似的举动,他是奥
古斯都身边的圈子里的人。每次偶遇拉尔古斯之时,普罗库莱乌斯都
会用手紧紧地捂住嘴巴,以此表示在拉尔古斯面前说话是很危险的。
[369]
伽卢斯之死让我们得以看到奥古斯都时代早期的罗马还未完全稳
定下来,奥古斯都政权随时准备动用暴力。不过,伽卢斯的政治地位
不是很高,他是不可能威胁到奥古斯都政权的。也许,他说了某些不
该说的话,然后被拉尔古斯汇报了上去。伽卢斯是极受奥古斯都信赖
之人。如若不然,他不可能得到埃及总督这样重要的职位。但是,包
括他在内,有许多人都会在接下来的这些年里逐渐发现,帝国时代有
了新的规矩。无论伽卢斯究竟做了什么或者说了什么,至少他让奥古
斯都感觉到有必要惩处一下这位朋友了。但就在这个时候,元老们介
入了。伽卢斯不属于元老之列,他是奥古斯都政权的受益者。在当时
的政治条件下,反对奥古斯都之人不会公开挑战他本人。因此,虽然
元老们在斥责伽卢斯之时表现得对奥古斯都忠心耿耿,但其中某些人
很可能只是想要铲除这么一个奥古斯都政权培养起来的新贵而已。
帝国时代的政治让友谊的面貌也不得不发生改变,而友谊是罗马
政治文化的核心要素。因此,伽卢斯事件反映出的是一个相当重大的
转变。罗马精英们向来珍视畅所欲言的自由,但伽卢斯事件宣示了言
论自由的时代已经结束。无论伽卢斯受到了什么指责,支持奥古斯都
的那些元老都只能附和,以此展示他们对奥古斯都的忠诚,因为此时
公开站在伽卢斯那边就相当于宣布自己是现政权的敌人。而且,奥古
斯都当时不在罗马,他几乎没有干涉这件事情。伽卢斯是在一种可怕
而强大的推力下走向死亡的。时人或许少有察觉,但当奥古斯都表明
他反对伽卢斯之时,伽卢斯就已经死了。
公元前24年上半年,在离开了将近三年以后,奥古斯都开始从西
班牙返回罗马,得知此事的元老们纷纷表决同意给奥古斯都颁发更多
宗教和政治领域的荣誉。这几乎要成为一项新传统了。元老们要建造
一座奥古斯都和平圣坛(Altar of Augustan Peace),用以庆祝他胜利
回归。奥古斯都还得到了免受法律的强制要求的权利。虽然他的权力
并没有因此而增长,但这项特权进一步凸显了他的特殊地位。此外,
元老们还给莉薇娅(Livia,奥古斯都之妻)的儿子提比略、奥克塔维娅
(奥古斯都的姐姐)的儿子马尔凯卢斯颁发了荣誉,仿佛在宣布现在这
个共和国的本质其实是君主制。提比略获许提前五年满足各项公职的
年龄限制,并且即刻被选入了元老院。马尔凯卢斯刚刚和奥古斯都的
唯一后代尤莉亚成婚,元老们直接任命他为第二档次的罗马官员(裁判
官),将他选入元老院,同时允许他提前十年参选执政官。[370]在自相
矛盾的奥古斯都的共和国里,传统的共和国官职被保留了下来,并且
成了奥古斯都政权的门面。但这些官职都会被元老院交给奥古斯都的
家族成员,其唯一理由就是褒奖这位实际上的君主。
奥古斯都政权矛盾的本质引发了人们的不满。他宣布了共和国已经得到恢复,却依然手握重权,他的家人甚至也得到了荫庇。所有人,尤其是元老,都不可能不知道这两种现象是互相矛盾的。罗马的保守政治文化不停地受到挑战,人们越来越无法忽视奥古斯都的本质是一位专制君主。当奥古斯都的共和国在公元前27年1月被创造出来之时,人们肯定能够清晰地看到这一点。后来,奥古斯都没过多久就离开了罗马,让这种本质得到了些许的掩盖。然而,随着他的归来,人们不可能再假装这个共和国还是以前的那个共和国。在接下来的两年内,这种潜在的不满情绪会酝酿出一场巨大的政治危机。
奥古斯都共和国的危机
公元前23年1月,年仅三十九岁的奥古斯都第十一次就任执政官。他已经史无前例地连任了九年。在这一年较早的某个时候,罗马又一次受到了周期性流行病的侵袭。病魔当然不会在意人的社会地位。奥古斯都患病了,而且一时之间高烧不退,他的身体渐渐衰弱下去。看起来,他很有可能会一命呜呼。于是,他把亲信和一些国家官员召到了身边,然后把各种官方文档交给了另一位执政官,其中包括了详细的军队部署和财政方面的记录。由此可见,另一位执政官之前无权查看这些文档。奥古斯都还把自己的玺戒交给了阿格里帕。这些举动显然意味着他决定把民政权力交还给正规的国家官员,同时让阿格里帕成为他的私产及政治继承人。[371]
随着病情的恶化,奥古斯都的医生安东尼乌斯·穆萨(Antonius Musa)变得越来越焦急。最后,他拖着奄奄一息的奥古斯都去洗了一次冷水浴,这种快速降温的手段居然成功地让奥古斯都退了烧。
这次疾病让许多人开始考虑奥古斯都死后会发生什么事,元老们议论纷纷。有人说,他打算把整个国家交给他指定的继承人。当然,从法律规定和实际运作来看,共和国是不可能被这样转交出去的。共和国的官员依法掌权,也势必要依法卸职。奥古斯都固然可以像恺撒一样指定私产继承人,但这种做法不是转移政权所属权的公认程序,其政治意义是不明确的(虽然无疑会有很大的意义)。但如果指定下一任的国家领导人,那就相当于宣布罗马现在就是一个君主国。
对于这种传言,奥古斯都不得不做出回应。他带着遗嘱来到了元老院,提议宣读遗嘱。没有人表示同意。首先,要求他读遗嘱会显得自己不信任这位权势滔天的大人物。其次,他既然主动提出要宣读遗嘱,那么肯定不会读出什么不利于他的内容。而且,遗嘱是私密的文件,理应在订立者死后才公之于众。罗马人会在遗嘱里把财产分享给朋友,表明自己是个忠于友谊之人。换言之,遗嘱是订立者对自己的社会关系的确认。因此,罗马人认为遗嘱是非常重要的。元老们当然不愿意公然强迫奥古斯都宣读这么一份私密之极的文档。
此时,有可能成为“皇位继承者”的有两个人:其一是年纪尚轻
的马尔凯卢斯,其二是奥古斯都的政治伙伴阿格里帕。如果以后来的
皇位继承案例来看,即使马尔凯卢斯没有官职,也没有政治、军事经
验,他也应该会继承皇位,因为他既是和奥古斯都关系最近的男性亲
属,也是奥古斯都的女婿。但奥古斯都向来不感情用事。就算是在公
元14年,他似乎也计划着让权力最大、经验最足因而也最有个人权
威、最有政治影响力的亲属来成为第一位接手皇权之人。因此,在公
元前23年的政治环境下,奥古斯都只会选阿格里帕来当他的政治继承
人。
阿格里帕是一位身经百战的将军,他也在罗马城内主持兴造了许许多多的建筑。而且,中下层的罗马人看起来也很爱戴他。当奥古斯都身处西班牙的时候,阿格里帕实际上在代表奥古斯都管理罗马。虽然他的家族背景比不上马尔凯卢斯,但马尔凯卢斯的经验毕竟太少。阿格里帕得到大多数军人拥护的可能性要大得多。况且,奥古斯都把玺戒传给了阿格里帕。
我们不清楚传玺戒这种举动究竟具有怎样的意义,当时的罗马人
或许也难以做出定论。但至少,这种举动留下了政治猜想的空间。阿
格里帕起码由此得到了某种超然于法律之外的权威。看起来,玺戒的
传承意味着就算奥古斯都去世了,罗马也不会脱离恺撒派势力的掌
控,因为阿格里帕会凭此而有权继承奥古斯都的政治地位。不过,如
果说奥古斯都政权还能勉强算是共和国历史上的例外,那么其继承者
的出现就让它显得不像是例外,而是某种可以承继下去的制度创新
了。随着罗马的政局变得越来越紧张,阿格里帕便奉命到东方去替奥
古斯都巡视诸省,他又一次成了奥古斯都的代表。阿格里帕的东方之
行就好像是奥古斯都之前去高卢和西班牙逗留的那三年。他的离去让
他得以完全避开旁人的攻击,也让那些执着于共和制度的元老暂时安
分下来。[372]
奥古斯都正承受着不小的压力。公元前23年7月,他离开了罗马,到城郊的一处圣地去庆祝“拉丁节”(Feriae Latinae)。7月1日,奥古斯都在节庆上辞去了执政官的职务,指定卢奇乌斯·赛斯提乌斯(Lucius Sestius)为继任者。赛斯提乌斯是布鲁图斯的拥护者,而且一直到现在都还在公开地赞扬布鲁图斯诛杀暴君的行为。这个继任的人选不太可能没有经过事先的挑选。奥古斯都想要由此来表明共和国真的恢复了,现在的政府就是正常的共和政府。
然而,实际情况依旧有别于共和国时代,奥古斯都取得了保民官的权力(tribunicia potestas)。他并没有担任保民官,但他拥有保民官的权力和职责。由此,奥古斯都宣示了属于他的政治版图。他会按照宪法和法律,以人民守护者的身份限制执政官的权威。从某种意义上来说,这一举动让奥古斯都政权回到了三头同盟时代。当时,后三头提出的兴兵理由就是反对一小撮元老侵犯人民的权利。而现在,元老们或许成功地让奥古斯都交出了执政官的职位,但他不会就此放弃。
正当政坛上风云变幻之时,奥古斯都不幸遭遇了一场悲剧:马尔
凯卢斯病逝了。他也和奥古斯都一样发了烧,穆萨也试着给他洗了冷
水澡,但这一次没有见效。就算阿格里帕会在奥古斯都万一病逝之时
继承他的政治地位,马尔凯卢斯也仍然是未来的继承者,他的死亡让
奥古斯都失去了所有的男性近亲。马尔凯卢斯得到了火葬,其骨灰被
放在了台伯河畔战神广场上的奥古斯都陵墓当中。这座陵墓会成为奥
古斯都的家族公墓,在未来的五百年里纪念着罗马的第一代皇室(请参
考图7)。卡皮托里翁山脚尚未完工的一座剧院被命名为马尔凯卢斯剧
院(请参考图8),即使经过了两千年的岁月洗礼,这幢宏伟的建筑也依
然让人惊叹不已。
四五年后,维吉尔的伟大作品《埃涅阿斯纪》问世了。这是一部
讲述罗马建城史的神话史诗,其中有一幕预言的场景。维吉尔让主人
公埃涅阿斯来到地下世界,看到了一系列领导着罗马从难民聚居的小
城镇成长为征服世界的大帝国的英雄人物。[373]想来,维吉尔最后应
该会以光荣无限的奥古斯都时代收尾,他在其他的预言场景里确实就
是这么安排的。但在这一幕当中,最后出现的是年轻的马尔凯卢斯的
亡魂和他在战神广场上的葬礼。这一幕的寓意是,马尔凯卢斯原本会
成为最伟大的罗马人,但就连诸神都为此感到嫉妒,出手夺走了他的
性命,让罗马人民失去了一位英雄。一般说来,很多人都青睐于英年
早逝、天妒英才之人,畅想着这些人如果活了下来,实现了自己的抱
负,是否能够解决所有的问题,让历史产生“另一种可能”。但是,
维吉尔为马尔凯卢斯所写的这个故事看起来和皇室很有关系,尤其是
考虑到马尔凯卢斯在去世的时候还根本没有取得什么值得一提的成就
(和其他的这类人物不太一样,比如,遇刺的美国总统约翰·F.肯尼
迪)。
尽管奥古斯都政权能够大张旗鼓地纪念去世的马尔凯卢斯,把他
的名字长久地留在罗马的建筑上,但奥古斯都对权力的掌控开始显得
有些脆弱了。马尔凯卢斯之死震动了奥古斯都政权。如果说维吉尔是
抓住了一些民众在马尔凯卢斯的葬礼上表露出来的态度,那么这场葬
礼本身则清晰地宣示了罗马已经拥有了君主制的基础。许多人,尤其
是平民表现得仿佛罗马已经是一个君主国了。虽然公众表达出这样的
态度可以算是对奥古斯都政权的支持,但同时也有一定的风险。参加
了葬礼、目睹了这一切的元老们都知道马尔凯卢斯还只是个孩子,他
们会清楚地意识到奥古斯都交给他们的这个所谓恢复了的共和国里有
一个皇室一般的家族存在,公众为这样一个年轻而几乎没有政治经验
的男孩深切哀悼,正是证明了他们愿意让这个家族以皇室之身统治国
家。奥古斯都共和国的君主制与共和制并存的双重性质暴露无遗。
我们或许可以把奥古斯都辞去执政官职务的举动视为一场正在发展的政治危机的结果,把阿格里帕派去东方可以让他免于和元老们发生正面冲突,也表明了阿格里帕在帝国政权中的独特地位。可是,皇位继承人和恢复了的共和国格格不入,就连奥古斯都本人也是如此。如果共和国真的已经恢复,那么辞去了执政官职位的奥古斯都就没有理由再留在罗马了。他本就有治理地方省份的职务在身,逗留于罗马只会让他成为君主制本质的最好证明。自公元前49年恺撒渡过卢比孔河以来,元老院的权力一直都处在个别强权人物的严重干扰之下。假如元老们真的能够让奥古斯都离开罗马,他们就可以重获久违的统治地位。
虽然现在的政治局势已经比较复杂了,但奥古斯都还遇到了一场
和政治密切相关的审判。这次审判的直接当事人是曾经担任马其顿总
督的马尔库斯·普里穆斯(Marcus Primus),他应该是克拉苏的继任
者。马其顿是个战事频发的省份,普里穆斯在任期间和当地的奥德吕
赛人(Odrysians)发生了冲突。他的作战很成功,但他在作战之时率军
跨越了自己的省界。严格说来,这是违法的。大约在公元前23年,他
回到了罗马,然后立刻就受到了指控。普里穆斯和奥古斯都走得很
近,他掌控的马其顿是一个很重要的省份,驻扎着大量的军队。奥古
斯都显然不太可能会坐视一个有可能与自己为敌的人掌握马其顿。为
普里穆斯辩护的就是和奥古斯都关系很亲密的卢奇乌斯·穆雷纳
(Lucius Murena)。不过,普里穆斯的自辩词有可能给奥古斯都带来一
些麻烦,他声称自己走出省界是因为马尔凯卢斯(这大概会被看作在代
奥古斯都传讯)或奥古斯都本人传来了命令要求他这样做的。
然而,不管是奥古斯都还是马尔凯卢斯都没有下达这种命令的权威。以罗马的标准来看,马尔凯卢斯只是一个没有任何公职的男孩,他没有权力对普里穆斯这样的高级官员下达指示。奥古斯都其实也不行。如果马尔凯卢斯确实参与其中,他的角色会十分有力地证明奥古斯都真的正在罗马共和国里打造一个凌驾于法律之上的王朝。如果传讯的是奥古斯都本人,情况会稍微好一些,因为奥古斯都当时还是执政官。但这还是有君主制作风的嫌疑,因为共和国的军事政策向来由元老院掌握。
这是一场政治审判,其目的是摧毁普里穆斯的政治生涯。如果陪
审员们对他的说法表示认可,宣判他无罪,那么这几乎相当于宣布奥
古斯都和马尔凯卢斯就是事实上的皇族。如果他们表示反对,那么和
奥古斯都交好的普里穆斯的政治前途就毁了。让所有人深感意外的
是,奥古斯都出庭做证了。他宣称普里穆斯所说的命令根本就不存
在。穆雷纳大怒,他质问是谁传唤奥古斯都出庭的,奥古斯都又为什
么要以证人的身份出庭。奥古斯都回答:“共和国。”他在捍卫共和
国。然而,其实他只是想要保护不宣之秘。他不能让所有人都知道自
己无视了元老院的权威,遑论马尔凯卢斯分享权力之事。接着,陪审
员们开始表决。一些人投了无罪票,但大多数人并不打算用这种方式
来宣布奥古斯都在撒谎。普里穆斯完了。[374]据我们所知,普里穆斯
是奥古斯都的朋友,他肯定也和帝国的其他高层人物有着非常密切的
关系。然而,奥古斯都依旧选择了牺牲他的政治前途。
不久以后,大概在公元前22年,有人密谋刺杀奥古斯都。我们永
远也不可能了解这种阴谋的真相。不过,这次的两个主要嫌疑人分别
是法尼乌斯·凯皮奥(Fannius Caepio)和上文提及的卢奇乌斯·穆雷
纳。他们都在被捕之前逃离了罗马。于是,他们遭到了缺席审判。负
责此案的是莉薇娅(奥古斯都的妻子)之子提比略,[375]这也是他第一
次处理重要的公务。但即使是在这种情况下,提比略也无法让陪审员
们一致同意判决有罪,这使得奥古斯都出台了法案,规定今后每一位
陪审员的判决都会被公之于众。这项新法非常有助于让各位陪审员在
这种政治审判中做出有罪的判决。凯皮奥在逃亡途中被抓回了罗马遭
到处死。之后,凯皮奥的父亲解放了所有在凯皮奥的逃跑路上出手保
护过凯皮奥的奴隶。某个背弃凯皮奥的奴隶还被在脖子上挂上了告示
牌,被带到罗马广场上示众,最后被钉死在十字架上。凯皮奥的父亲
这是在向所有人宣布他相信凯皮奥无罪,同时也表达了他对奥古斯都
的抗议,暗指奥古斯都蓄意杀害凯皮奥。
相比之下,我们不是很确定穆雷纳究竟是如何死去的。穆雷纳的
人脉很广,他的家族和帝国高层的关系很近。他的兄弟普罗库莱乌斯
是当初亲手抓住克莱奥帕特拉的人,也是科涅利乌斯·伽卢斯的朋
友。穆雷纳的姐妹提兰提娅(Terentia)是麦奇纳斯的妻子,而后者又
是奥古斯都身边的亲信。不仅如此,我们一般还认为提兰提娅是奥古
斯都的情人。穆雷纳还有一个兄弟本来会成为公元前23年的执政官,
却在即将受任之时去世了。[376]另外一个兄弟还曾在一些年前指挥过
阿尔卑斯山区的军队。
普里穆斯和穆雷纳(伽卢斯或许也算)的下场都充分表明奥古斯都会为了政治目的而抛弃朋友。长期与奥古斯都共事之人应该不可能不知道他会干出这种冷酷的事情,但罗马人通常还是认为他们的政治秩序是依托于私交网络和彼此之间的恩情而存在的。穆雷纳的倒台尤其令人吃惊,奥古斯都的追随者因此产生了分裂。麦奇纳斯跟提兰提娅说了她的兄弟正遭到调查,然后提兰提娅就告知了穆雷纳,让他逃跑。[377]
麦奇纳斯和提兰提娅或许展现了家人之间互帮互助的关系,但在当时,家族和政治基本是分不开的,他们的行为可以被视作背叛。
在之前的两场重要的政治审判当中,各位陪审员至少是不相信奥古斯都的。现政权露出了獠牙,实现了自己的某些目的,但代价就是让许多人看清了共和制度其实没有恢复。一些元老开始明显地表现出反抗的意图,发轫于公元前28年的奥古斯都共和国看起来即将终结。
奥古斯都仍然有选择的余地,他有军队和资金。但动用军队会让罗马再次陷入内战,还会让奥古斯都被大多数人当作独夫。以权力的实质(金钱、军队)来看,奥古斯都占着上风。元老们也都明白奥古斯都掌握着庞大的政治资源,所以愿意认可他的显赫地位。但是,回首晚期共和国的历史,我们会发现元老们向来不会因此放弃他们的原则。元老们相信自己的权威和传统,相信自己有权利统治这个国家,相信元老治国是罗马的唯一出路。为了让罗马延续下去,奥古斯都需要和元老们达成和解。这是一场互相恐吓的政治比拼,一边的底牌是暗杀,另一边则是重新开启大规模的内战。不过,无论如何,在公元前22年,奥古斯都正准备前去地方省份。在这种情况下,难免会有一些元老认为己方正在逐渐获胜,奥古斯都的权力正在衰落。
但是,三年后,奥古斯都回来了。那时,他的地位已经变得无比稳固,自以为即将取胜的那些元老将再一次切身地体会到政治斗争是何等的现实而残酷。
第十四章 奥古斯都的共和国
[363] Res Gestae , 34.
[364] Dio, 53.11.
[365] Dio, 53.22.
[366] Dio, 53.28; Res Gestae , 12.
[367] Dio, 53.23; 27.
[368] Friedhelm Hoffmann, Martina Minas-Nerpel and Stefan
Pfeiffer (ed.), Die dreisprachige Stele des C. Cornelius Gallus:
übersetzung und Kommentar (Berlin and New York: Walter de Gruyter,
2009).
[369] Suetonius, Augustus , 66.2; Dio, 53.23-24.
[370] Res Gestae , 12; Dio, 53.28.
[371] Dio, 53.21.
[372] Dio, 53.22.
[373] Aeneid 6, 752-885.
[374] Dio, 54.3. Velleius Paterculus, 2.91.
[375] Suetonius, Tiberius , 8.
[376] 穆雷纳的兄弟瓦罗(Varro)的故事比较复杂,有一些文本没有把瓦罗包括在执政官的名单当中。不过,Fasti Capitolini把瓦罗·穆雷纳视作公元前23年1月的执政官。但是,他接下来遇到了某些事情(铭文残缺,不得而知)。
[377] Suetonius, Augustus , 66.3.
第十五章 罗马的混乱与奥古斯都的权力
执政官选举通常开始于前一年的年中。刚刚辞去公元前23年执政官职务的奥古斯都并没有竞选公元前22年的执政官,治理罗马的职责传到了其他人手里。虽然他或许做好了相应的计划,但奥古斯都并没有随阿格里帕一起去地方省份。自公元前32年以来,这是元老院第一次在不包括恺撒的两位执政官带领下展开传统的新年宣誓和献祭仪式。
公元前22年一开始就不太顺利:冬季的风暴十分强烈;台伯河河水泛滥成灾;罗马本身也受到了雷暴雨的侵袭,一些著名的雕像被闪电击中;洪水还带来了疾病;罗马的粮食储备消耗殆尽,城市陷于饥饿之苦。
于是,平民发起了暴动。他们拿下了广场,把元老们围困在元老院里,并且要求元老们让奥古斯都担任独裁官,不然就火烧元老院。手持法西斯的执政官扈从被平民带出了元老院,一起去找奥古斯都。两位执政官就这样被夺走了权威的象征。找到奥古斯都以后,人们请求他来担任独裁官,掌管罗马的粮食供给。奥古斯都夸张地撕破了自己的衣服,露出了胸膛,以此表示自己如果担任独裁官就会遭遇刺杀。不过,他最后还是同意了处理粮食供给的问题。毕竟,他是平民的保护者,也是他们在危难之际的避难所。五天以后,粮仓满了。[378]
奥古斯都一直都在细心地维持着他和罗马平民的关系。自他步入政坛的那一天起,他就在努力地把自己塑造为平民利益的捍卫者,试图将自己与保民官的权力和责任联系在一起,成为人民的代表和保护者。早在公元前36年,他就使用了一些保民官的象征。公元前23年,他还在卸任执政官的同时取得了保民官的权力。由此,奥古斯都表明了自己就算不再是元老院的领导者也会继续保护人民的利益。
奥古斯都丝毫不吝于用金钱来宣示自己的立场。凭着尤里乌斯·
恺撒的遗产,他给至少二十五万人送出了每人三百赛的奖金。公元前
28年,他又给类似规模的群体发放了每人四百赛的奖金作为阿克提翁
和亚历山大战事的胜利纪念。公元前24年,他从西班牙归来,再一次
送出了每人四百赛的礼物。这个数额的资金大概足以支撑两个人以比
较低的消费水平在罗马度过一年。公元前23年,奥古斯都给每位罗马
居民提供了十二份粮食配给,受惠者数目同样至少有二十五万人。
[379]
奥古斯都直接送给罗马城居民的经济利益已经达到了一个非常庞
大的规模。三次奖金的总额分别是七千五百万赛、一亿赛和一亿赛,
他在公元前23年购入的粮食则价值四千万赛。[380]也就是说,在阿克
提翁之战结束以后的六年时间里,奥古斯都花费了两亿四千万赛的资
金来直接援助二十五万罗马平民。每位登记在册的罗马男性都得到了
九百六十赛,每个罗马人勉强维持生活的费用为每年两百到三百赛。
由此可见,奥古斯都给罗马的贫困家庭提供了不小的帮助。
但奥古斯都给罗马经济注入的资金还远远不止这些,他和阿格里
帕实施了规模极其浩大的建筑计划。许多罗马自由民都需要工作,而
在机械化到来以前的时代,搬运、建筑业往往提供了非常多的就业岗
位。[381]在一般情况下,有百分之十到百分之十八的城市男性居民工
作于建筑行业。[382]但帝国时代开头的这几十年并不一般,阿格里帕
和奥古斯都正在让罗马改头换面。当然,以工资形式来到平民手里的
资金并不像前文所提的奖金那样轻松、直接。但是,各行各业的工作
者—切割、运输石块者,搬运木材和砖块者,砌墙者,装潢者,制作
神像者,制作金属配件者,制造、修复建筑工具者—都不难看出这些
浩大的工程的存在基本要归功于奥古斯都。而且,这还没有算上食品
和其他商品的贩卖者,他们是第二大受益群体。如果奥古斯都不在
了,这些支撑着他们生存的工作也会随之消失。
新工程当中虽然有很多用以装饰或纪念的建筑,比如剧院、凯旋
门、纪念碑、神庙以及奥古斯都本人的宫殿,但也有一些非常实用的
建筑。阿格里帕就致力于建造水渠,他修复并改良了马尔奇乌斯渠
(Aqua Marcia),新建了尤里乌斯渠、少女渠(Aqua Virgo)和阿尔西艾
提努斯渠(Aqua Alsietina),让罗马城的供水量增加了百分之五十
多。[383]水是非常重要的资源。新鲜、干净的水能够让所有的城市居
民都受益良多,无论他们富贵与否。罗马的居民数量在前一百年里增
长了很多,已经远远超出了既有基础设施的承载范围。供水量的不足
难免会导致罗马城的居民被迫使用脏水,用水量受限,还要花不少的
时间和精力去寻找、运输可用的水。水渠是当时横贯意大利乡间的主
要设施,许多峡谷里都建有高架渠,所有从新的水渠中受益之人都能
切身地感受到阿格里帕对罗马人民做出了实实在在的贡献。这些水渠
等同于他们的政治声明,其他的任何人都不能以这种非凡的手笔来帮
助罗马城的平民。
精英阶层的各位史家习惯于把这种皇家政策蔑称为“面包与马
戏”,令其看起来像是收买人心(也就是说是一种腐败)或是意在让广
大群众忽视政治形势的麻痹政策。然而,当时的罗马社会是极其不平
等的。在这种社会里,很多人都非常贫穷,他们的生计真的是一个大
问题。阿格里帕和奥古斯都则以实际行动表明了他们愿意用国家的资
源来帮助平民,大幅提高他们的生活水平。在公元前28年到公元前23
年之间,他们二人把令人瞠目的大量资源投入了民生领域。其他的任
何一名元老甚至整个元老院都无法与之相媲美。
这种肚子政策的根本原理是很简单的:全体人民越穷就越渴望生
活补助,也就越支持为他们提供了金钱、食物和水的人。对于穷人而
言,最理想的情况就是政治精英们能够感觉到他们其实在某种意义上
依赖于穷人,然后主动通过社会补助来赢得穷人的支持。奥古斯都在
罗马平民身上投入的巨量资源,相当于认可了罗马公民都有权分享国
家的财富。但如果认为这是大公无私的奉献之举未免又太天真了一
点,阿格里帕和奥古斯都确实是在用这些资源换取平民的支持。显
然,他们这么做是为了能够在未来与元老发生冲突之时得到罗马平民
的助力,虽然他们当时还不知道自己具体会遇到怎样的冲突,但有智
慧的政治家总是会未雨绸缪。
动用巨额资金来赢得平民的爱戴,其实就是把广大平民纳入奥古
斯都的私人关系网络,军队和平民由此都成了奥古斯都的追随者。与
奥古斯都的行为构成鲜明对比的是,许多元老都只会秉承多年的传
统,对罗马平民不屑一顾。这主要是因为他们普遍相信自己的地位依
赖于贵族同伴,而不是贫穷的平民。但奥古斯都和阿格里帕却知道,
元老是不可靠的盟友。从公元前22年开始到公元前19年,奥古斯都将
收到这笔巨额投资的回报。
公元前24年,奥古斯都给罗马人民发放了礼金。如果以小费视
之,其规模未免太大了一些,但看起来,他花这笔钱是有政治意图
的。公元前23年,奥古斯都给罗马人民提供了额外的粮食。这次的慷
慨之举并不是为了纪念什么政治事件,奥古斯都看起来只是想要帮助
大家弥补去年意大利歉收造成的供粮漏洞而已。歉收一般会导致罗马
市场上的粮价上涨,有可能会让某些市民承受饥饿之苦,进而带来政
治动荡。我们没有可以用来揣测公元前23年收成的信息,不过大概在
公元前22年较早的时候,台伯河谷遭受了洪灾,特大降雨有可能冲毁
了比较早的那批作物。在这相邻的三年里,罗马人民经历了两次甚至
三次歉收。
罗马的农业是相当发达的。罗马农民会种植很多种类的作物,会
尽量抵御某些农业风险,也会购买一些实用的工具。他们有酿造葡萄
酒、生产橄榄油的设备,也有保存、运输食物的手段。但是,世界上
所有地区的农业都难以承受异常的降水和气温带来的打击,地中海沿
岸地区尤其如此。降水过多或过少都会导致农作物难以正常生长。一
般说来,大约每四年就会有一次普通的歉收,每十年更是会有一次几
乎颗粒无收的情况出现。连续出现的歉收还会让农民没有时间和资源
来恢复正常的生产。在极端情况下,他们甚至会不得不暂时离开自己
的田地,去其他地方寻找食物和工作。[384]而在难民眼里,最明显的
去处就是罗马城。
罗马人民成功地利用自己的政治权力让罗马的政治精英们为罗马城准备了价格稳定的粮食供给。这项政策从晚期共和国开始,在帝国时期也一直延续了下去。但是,这部分粮食并不能满足全城人口的需要。受惠的大概只有二十万男性,他们的家人和很多不在名册上的人都得依靠粮食市场来维生。
我们可以设想一下,假如某个田产不多的农民在年成一般的时候
卖一半吃一半,那么在收成下降一半的那些年里,他就只能把当年的
全部收成都用于自身的消费了。如果某个农民通常卖七成吃三成,那
么在减产一半的时候他就得吃这一年收成的六成,只卖剩下的四成,
但市场上看到的是,他卖出的粮食只有平时的二成了。所以,农业产
出的一点小波动都会严重地影响城市的粮食供应。大地主面临的局面
是类似的,因为他们在歉收之时必须把更高比例的作物用于供养他们
的佃农。
此外,无论是拥有小规模田地的自耕农还是大地主一般都想在灾
年提高粮价以弥补这一年的损失。同时,由于粮食供给确实减少了,
粮价难免会如他们所愿地上升,但是在这种情况下,粮食市场有可能
彻底崩溃。农民(其实更可能是粮食商人)会仔细地考虑在什么时候把
粮食带到市场上去,然后又要以什么价格卖出。就算对供求法则只有
相当粗浅的认识,他们也很可能会伺机把价格抬得非常高。接下来会
发生的只有两件事,而这两件事都是相当糟糕的:这些粮食有可能会
因为买家不愿购买高价粮食或根本就买不起而卖不出去;或者粮食以
虚高的价格被卖出去了,从而使人们更加倾向于囤积粮食,抬高粮
价。我们有可能会看到粮仓里存着粮食,市场上甚至也有粮食(至少高
价可以买到),但许多人却饿着肚子的景象。
奥古斯都在公元前23年为罗马居民提供粮食的举动证明了他认可
罗马城居民获得食物的权利,也宣示了奥古斯都的共和国愿意为其人
民提供生活所需。他买来了食物,将其分发给大家。农民得到了钱,
罗马市民得到了食物。但在公元前22年,奥古斯都已经不再是执政
官,而继任的两位执政官没有出手解决粮食不足的问题。他们或许是
没有足够的资金,或许是没有看到人民的需要,或许只是不愿意出
手。毕竟,元老们都是大地主,而且向来不怎么同情挣扎在水深火热
之中的穷人,他们很可能处于粮食商人的立场上。罗马平民也能想明
白这些事情。在古典时代因食物短缺而爆发的起义当中,平民的攻击
目标始终是富有的地主,因为他们认为这些大地主有意囤积粮食,以
便趁着人民遭受苦难之际大发一笔国难财。
这两位执政官既没有军队也没有警察。显而易见,几万名饥肠辘辘、愤怒不已、支持着奥古斯都的平民突然出现在广场上会给执政官造成巨大的压力。但也许几千人就足以困住各位元老,迫使他们屈服。唯一有条件轻松制止这些民众、保护诸位元老的是奥古斯都,因为他有自己的卫队。然而,他看起来不太愿意让卫兵们去广场上保护元老,打压这群想要让他来拯救自己的民众。
被困在元老院里的两位执政官放弃了象征着他们的权威的扈从。
民众把这些扈从带到了奥古斯都(他肯定在罗马城内)面前,请求他来
担任独裁官。当然,这群民众不是经由正规的程序组建起来的,他们
不是平民会议那样的合法机关。但是,共和国制度的首要原则就是人
民主权,而这次的事件显然体现了人民的意志。从政治的角度来说,
奥古斯都大可以按照人民的意愿,接受独裁官的职位。法律上的细节
想必会有办法解决的,困居元老院的元老们大概很快就会同意批准奥
古斯都担任独裁官。然而,奥古斯都露出了他的胸膛,以这种戏剧般
夸张的方式拒绝了民众的请求。
当时的世界毕竟没有话筒,也没有大众传媒,和一大群愤怒的民
众沟通确实需要用一些夸张的动作来表达自己的意思—这算是一种政
治默剧。奥古斯都的意思很清楚:受任独裁官等于他的死亡。我们或
许可以将其解读为他对宪法极其尊重,宁死也不愿担任独裁官。这种
看法还符合了许多人心中的奥古斯都的形象—试图在自己的权力和罗
马的传统之间寻求平衡的一位宪法改革家。后来,奥古斯都本人则暗
示他当年的拒绝是在谦让,以求符合罗马的道德传统。[385]
然而,这种观点难以让人信服。奥古斯都很可能是在以展露胸膛
的行为来表示自己会步前一位独裁官恺撒的后尘,惨遭元老们的毒
手。[386]他想要让人们相信他是站在平民这边的,他是人民的保护
者,愿意对抗威胁着全体人民的元老。他正是以人民保护者的身份再
次出手处理供粮问题、干涉罗马政务的。奥古斯都的谦让是属于伟人
的谦让,他拒绝担任独裁官是因为真正的权力不在此处。这也是他精
心考虑的结果:受任为独裁官就会坐实其对手的批评,让政治形势倒
退回三头同盟末期的状态,毁掉奥古斯都恢复的共和国,更有可能导
致非常不理想的恶果。
奥古斯都解决了粮食供给的问题。为此,他发明了一个供应粮食
的新职位。在他的介入下,罗马的粮食供应在不到五天的时间里就恢
复了正常。这种惊人的速度让人不禁想要加以思考,就算奥古斯都在
接受请求以后就立刻开始着手准备,向各地省份发出了请求供粮的消
息(尤其是阿非利加、西西里、萨丁尼亚),他的信件也几乎不可能在
五天之内抵达目的地。更何况,他们还得临时准备紧急供粮的船只,
把粮食装上船,然后运到普提欧利(Puteoli)或奥斯蒂亚,接着再用车
辆或者驳船运到罗马。这一系列流程一般要花费好几周的时间。那
么,奥古斯都究竟是如何在五天之内解决粮食短缺的问题的呢?
这里有几种不同的可能性。首先是阴谋论。鉴于奥古斯都控制着
重要的粮食产地西西里,有大量的粮食都在他的掌握之中。当粮食危
机渐渐加重之时,奥古斯都猜想元老们会无法解决这个问题,便有意
地减少了进入市场的粮食数量。第二种可能性是,奥古斯都成功地说
服了意大利的那些粮食商人、农民、地主,让他们放弃了囤积居奇的
打算。毕竟,拒绝奥古斯都的要求向来都有很高的风险。还有一种可
能性是,随着奥古斯都宣布要出手管理粮食供给,手中存着粮食的那
些人很自然地认为奥古斯都会强征存粮,或是会很快地找到其他渠道
的粮食来供给罗马的粮食市场。无论如何,粮价都会在不久以后恢复
正常。也就是说,现在就该出手存粮了。
不管奥古斯都到底做了什么,这次的粮食危机终究是结束了。而且,他飞快的解决速度很可能会让平民们更加相信这些元老不是无能就是歹毒,人为地抬高了粮价,只为谋取私利。总而言之,公元前22年初,罗马政坛上再次出现了两极对立的景象。在此期间,奥古斯都证明了他确实是人民的权利的捍卫者,会为人民挺身而出,对抗元老。
缺席之策:没有奥古斯都的奥古斯都共和国
在年中将至之时,奥古斯都离开了罗马,前去西西里。但他的离去并没有给罗马的政局带来和平。在粮食起义的暴力冲突和凯皮奥及穆雷纳的阴谋发生以后,罗马深陷于混乱之中。[387]即将到来的下一个政治热点事件是执政官选举,这次的选举应该是被推迟到了这一年较晚的时候,因为奥古斯都当时肯定不在罗马城内。
选举过程中发生了暴力冲突。这种事情并不罕见,但这次的起因
不是竞选者之间的矛盾,而是没有参选的奥古斯都的支持者发起的骚
乱。负责选举执政官的是以百人团(centuria)形式组织起来的罗马公
民会议,他们在投票时也要按照顺序经过“桥”。这种会议是有可能
失控的,因为虽然主持会议的官员会尽量维持现场的秩序,但他的声
音有可能会被选民淹没。这一次,选民们扰乱了会议的正常流程。他
们或是投票给没来参选的奥古斯都,或是只愿意选举一位执政官,因
为他们想把另一个位置留给奥古斯都。[388]
人民的意志昭然若揭。在这种情况下,恐怕极少有人敢于一边顶着冒犯奥古斯都的风险,一边公然对抗民意。此时正在西西里岛上的奥古斯都很可能见到了使者又一次前来请求他担任独裁官,接受另一个执政官的职位,但奥古斯都拒绝了。不过,罗马人民至少已经表明了他们不满于公元前23年的安排,他们希望奥古斯都能够继续扮演罗马政治的中心角色。为此,他们不惜用武力来强迫元老们让步。
对于元老们而言,公元前22年发生的事件极其糟糕。奥古斯都展
现了他的权势,而各位元老却只能忍气吞声,还得被广大民众指责为
无能之辈。接下来的公元前21年也未见起色,新执政官马尔库斯·洛
里乌斯(Marcus Lollius)是独自上任的。他的当务之急就是召开选
举,给自己选出一位同僚。这些选举同样引发了激烈的争议。奥古斯
都收到了消息,请求他从西西里回到罗马来恢复秩序。但他并没有同
意,反而把各位竞选人召到了西西里,嘱咐他们在投票期间暂时离开
罗马,躲避风头。最终,(在又一轮暴力冲突之后)其中一人当选为执
政官。罗马之事本应由罗马的官员,尤其是执政官来负责,但洛里乌
斯却无法控制住局面。奥古斯都把各位参选者召集到西西里的行为充
分说明了奥古斯都拥有着巨大的政治权威,这些竞选人犹如他的下
属,而他则是国家的监管者。
奥古斯都不愿返回的原因或许和罗马的政治形势无关。如果在公
元前21年返回,奥古斯都的地位会比公元前23年更高,他可以再一次
向元老提出条件。然而,这并不能解决从公元前24年开始困扰他的政
治问题,奥古斯都共和国的矛盾依旧存在。他有一个更加大胆的计
划。在公元前23年,为了处理帕提亚人带来的麻烦,奥古斯都派阿格
里帕去了东方。帕提亚人既是一个需要解决的问题,也是奥古斯都建
立战功的机会。于是,阿格里帕被召回,奥古斯都开始航向希腊。
公元前21年,当初匆匆离开的阿格里帕终于回到了罗马。后世的
历史学家们猜想他的离开是因为他敌视马尔凯卢斯,想要争夺皇位。
然而,与奥古斯都患病一事相关的史料表明,事实也许恰恰相反,阿
格里帕才是当时更有可能继承奥古斯都的政治地位之人。不管怎样,
马尔凯卢斯后来没过多久就病逝了。阿格里帕此行或许是一种政治策
略,用以避开那些比较倾向于共和制度的元老,但他也在莱斯沃斯岛
上(Lesbos)代表奥古斯都有效地治理了东方的省份,并且为奥古斯都
的大规模东征做了准备。在阿格里帕返回罗马以后,他被顺理成章地
确立为奥古斯都的继承人—阿格里帕迎娶了奥古斯都的女儿、马尔凯
卢斯的遗孀尤莉亚。他早已是奥古斯都政治集团的核心人物。现在,
他更是进入了王朝的中心。这桩婚姻同时也印证了奥古斯都在公元前
23年对阿格里帕做出的安排。
虽然阿格里帕回来了,但罗马人民依旧时常与元老们作对。公元
前21年,罗马城内要选举一位在某个节日期间管理城市的临时官员。
人们因此发起了暴动,甚至直到节日结束以后也没有罢休。[389]同年
召开的下一年执政官的选举活动很可能也受到了影响,罗马人民这一
次也只选出了一位执政官。在公元前20年,盖乌斯·森提乌斯·萨图
尔尼努斯被选为下一年的执政官,奥古斯都再次被选为另一位执政
官。到了第二年,萨图尔尼努斯只得独自上任。阿格里帕应该已经在
公元前21年离开了罗马。他先去了高卢,然后到了西班牙,因为奥古
斯都在几年前取得的胜利看起来还不足以完全稳住局面。[390]
罗马的暴力事件仍未停止,萨图尔尼努斯得到了一队卫兵的保
护。奥古斯都则又接见了一位使者。这一次,他采取了史无前例的做
法—指定自己的代表去担任执政官,虽然我们不知道他究竟是以什么
名义按照什么程序来做这种事情的。又一次,罗马平民向元老们表明
了国家的正常运转离不开奥古斯都的权力,而奥古斯都则又一次用他
的权力给罗马城带来了稳定。[391]奥古斯都的这种实质性统治地位并
无法律依据,但重要的是,罗马离不开他。而且,他有足够的权威来
贯彻其意志。
从公元前22年到公元前20年,平民频繁地出现在罗马的政治舞台上。他们拥护奥古斯都,不惜动用暴力,给罗马带来了混乱。元老们不得不认真地对待他们的诉求。看起来,奥古斯都有可能在背后鼓励平民的活动。毕竟,这些平民总是拒绝选举第二位执政官,我们不禁要怀疑他们是有组织的。
在离开罗马的日子里,奥古斯都的权势不断地增长。元老们难以
成功地应对作乱的平民,还不得不反复地看他们展示自己对奥古斯都
的忠诚。对元老们来说,每一次事件都是教训。民众对元老的威胁能
够直接有效地巩固奥古斯都的地位。相比之下,虽然元老们肯定还记
得奥古斯都掌握着大量的军队,但戍边的士兵终究离罗马太远。在平
民的威胁下,罗马随时有可能陷入无法无天的混乱状态,而奥古斯都
的权力可以维持住秩序。奥古斯都能够把执政官竞选者召到面前,对
他们下达指示,甚至还能指定执政官。共和国的基本运作流程显然受
到了奥古斯都的破坏,但同时却又离不开他。奥古斯都的共和国无法
在没有奥古斯都的情况下运转下去。
公元前19年,元老们的权威即将迎来又一次或许更加强大的挑战。不过,到了那个时候,奥古斯都已经在东方战场的“胜利”荣光之中踏上了归途。
伊格纳提乌斯·鲁弗斯的“阴谋”
关于伊格纳提乌斯·鲁弗斯(Egnatius Rufus),我们所知甚少。公元前21年,他当选为建筑官,登上了政治舞台。建筑官的职责是维护罗马的建筑、举办各种运动赛事,这两件事情都非常有助于赢得民心。身为建筑官,鲁弗斯设立了保护城市的消防队。然而,这个看似简单的举动让他走上了激进的政治道路,甚至最终走向死亡。
对于罗马而言,火灾是个不小的威胁。因为罗马的供水量有限,
而且也没有高压水枪,就算是小规模火灾也不是很容易就能扑灭的。
况且,罗马的建筑是比较拥挤的。多层的住宅楼之间有可能只以一条
窄窄的小巷(最窄为七十厘米)相隔,火势很容易就蔓延到相邻的建筑
上去。此外,当时既没有消防条例,也没有上层的紧急逃生通道。在
大型火灾发生之时,人们往往需要拆毁附近的建筑,以便构成火障。
但就算如此,火势也有可能直接穿过这些由瓦砾构成的火障区。更何
况,当时没有正规的消防队。每当火灾发生,受灾者就只能指望邻居
们自行组织起来,备好水桶,找到附近的水源,带上斧子和其他工具
来挽救自己的家。但凡火势稍大一些,人们就很难迅速地将其扑灭,
只能接受惨淡的现实。
鲁弗斯设立消防队的举措拓展了建筑官维护罗马城建筑的职责。
他让自己的奴隶成了消防队员。为了及时救火,他肯定要在全城各地
安排人手。而且,消防队必须有一定的规模。所以,他也出资招收了
其他人进入消防队。[392]鲁弗斯其实可以把这支队伍用到各种政治会
议上去。此外,消防队给鲁弗斯赢得了不少的人气,罗马人民开始拥
戴他。
任何寻求平民支持或者说试图组织起非精英群体的政治人物都会
被政治精英们怀疑为企图煽动民众犯上作乱的野心家。但是,鲁弗斯
的成功让他信心大振,开始竞选更高一级的裁判官。严格说来,连续
任官是违法的(虽然这条法律没能阻止奥古斯都连任),但在民意的要
求下,这条法律被忽视了,人民主权依旧是罗马政治生活的第一信
条。在卸任建筑官的时候,据说鲁弗斯声明自己把罗马城完好无损地
交到了继任者手里。为此,政治精英们深感不悦,因为从理论上说,
他们都对罗马城负有责任。[393]
接下来的那一年,也就是公元前19年,鲁弗斯宣布了他有意参选
执政官。主持选举的是森提乌斯·萨图尔尼努斯。此时,他还是唯一
的执政官[在奥古斯都指定的卢克里提乌斯·维斯皮洛(Lucretius
Vespillo)回来上任以前],并且已经通过投票表决获得了一队卫兵。
对于鲁弗斯的竞选意向,萨图尔尼努斯公开表示他不会给鲁弗斯参选
的资格。严格说来,负责主持选举的官员必须允许他人参选。但萨图
尔尼努斯有权这么做,虽然他同时也违背了平民的意愿。或许,我们
可以把他的行为看作在顶着民众的压力宣示执政官的权力。然而,鲁
弗斯并不是唯一的受害者。萨图尔尼努斯还禁止了几个人参选裁判
官,我们很难不去猜想这些人可能都和鲁弗斯有一定的关系。当然,
萨图尔尼努斯的这种做法导致了罗马城中再次爆发暴力事件。一位名
为维莱乌斯·帕泰尔库鲁斯(Velleius Paterculus)的史家把萨图尔尼
努斯比作历史上捍卫罗马共和国的那些英雄,但其实我们并不确定事
情的真相。[394]
接下来发生的事件让人难以捉摸。据说,有人发现鲁弗斯正在密
谋刺杀奥古斯都。于是,鲁弗斯还有他不知名、数目也不确定的支持
者就都被杀死了。我们恐怕永远也说不清古代的这些阴谋究竟是真事
还是为铲除政敌而捏造的借口。在鲁弗斯的这次事件里,如果“阴
谋”属实,那么他至少得计划在奥古斯都于公元前19年10月12日返回
罗马以后再动手。然而,在那个时候,鲁弗斯的敌人森提乌斯·萨图
尔尼努斯已经死了。这难免会引人怀疑。虽然萨图尔尼努斯或许是自
然死亡的,但如果没有什么值得大书特书的事情,那么维莱乌斯把他
比作古代英雄的说法就太过夸张了一些。没有史料明确提过有执政官
遇害(如果有就肯定堪称大事)。鲁弗斯的罪名是预谋对奥古斯都不
利,而不是谋杀。但萨图尔尼努斯之死至少算是对鲁弗斯有利。
奥古斯都恰巧也能从中获益。因为从萨图尔尼努斯的表现来看,
他有才干,也有一定的独立思想,并且有能力团结其他的元老。他的
死亡让奥古斯都得以安排自己的人去替代这样一位独立、自信、有影
响力的人物,在公元前19年末的这几个有重要意义的月份担任执政
官。萨图尔尼努斯的继任者为马尔库斯·维尼奇乌斯(Marcus
Vinicius)。维尼奇乌斯是一位著名的奥古斯都派将领,曾在日耳曼尼
亚建立大功。[395]他的出身并不显赫,其家族步入罗马政坛的时间不
久。[396]后来,维尼奇乌斯和奥古斯都在一起玩骰子,他的子孙也都
出人头地。[397]显然,他和奥古斯都走得非常近。
我们必须设想一下鲁弗斯行刺奥古斯都能够得到什么好处。他绝
无可能像奥古斯都那样控制军队。即使他在平民当中的人气也许能和
奥古斯都相比,他也不可能迫使元老们同意让他也享有特殊的待遇。
反观奥古斯都,他铲除鲁弗斯的动机是完全合理的。鲁弗斯挑战了他
对平民的掌控,奥古斯都不可能容忍他的存在。而且,杀死鲁弗斯可
以向罗马元老院和人民发出一个信号。就人民而言,奥古斯都可以由
此凸显自己的权力,让他们明白自己不会容忍这种三心二意的行为。
平民需要奥古斯都的关系网络,他们理应效忠的对象是奥古斯都,而
不是其他人。就算奥古斯都政权和平民之间有着互相依赖的关系,这
张政治网络也是有等级之分的,其中的下属应当服从奥古斯都和阿格
里帕的领导。
而对于各位元老来说,奥古斯都此举的意义比较复杂。首先,无
论鲁弗斯的阴谋是真是假,将他杀死都可以展现奥古斯都的权威。只
要奥古斯都愿意,他随时都可以除掉一位人气较高的知名政治人物。
其次,杀死鲁弗斯可以表明奥古斯都愿意和元老们合作。鲁弗斯在之
前的这几年里一直在威胁着各位元老和执政官,而奥古斯都出手除掉
了他,恢复了政治秩序。这说明元老们可以倚靠他的力量。或许,我
们可以更加露骨地说,元老们需要奥古斯都的保护。在公元前1世纪20
年代早期,元老们看起来在尝试着摆脱奥古斯都的阴影。但到了公元
前23年以后,元老们在一次又一次的暴力事件当中发现自己既没有能
力控制住自己的同伴,也无法约束罗马平民。就在这种情况下,奥古
斯都表示愿意尊重各位元老,并且为他们恢复稳定的秩序。可以想
见,元老们很可能对此报以感激之情。但是,奥古斯都的庇护不是没
有代价的。
鲁弗斯之死为新的政治协定的诞生铺好了路。奥古斯都即将从东方带着一场重大的外交胜利归来。元老们毫不迟疑地为他准备好了又一轮的荣誉,再次表示自己大力支持并且忠诚于他。公元前24年归来的奥古斯都还可以算是对元老治国的最大威胁,但在公元前19年,元老们已经不得不紧张地防范着罗马的平民。此时的奥古斯都反而是秩序的捍卫者。
奥古斯都的共和国依然是自相矛盾的。奥古斯都本人的地位仍旧有违共和制度的传统。然而,现在看来,这种矛盾并不是从三头同盟时代不幸保留下来的偶然现象。公元前23—前19年的历史已经证明了奥古斯都共和国的存在是有必要的,是奥古斯都化解了罗马平民的革命情绪,也是奥古斯都让军队安分地驻守于地方省份。奥古斯都成了罗马社会等级制度的捍卫者。古代的那个罗马共和国只有很少的一部分延续了下来,现在的罗马显然不可能是一个共和国,奥古斯都拥有着君主的权力。但是,如果没有奥古斯都的存在,扎根于旧日的共和国的那一整套社会等级制度就会崩溃。现在,罗马的守旧派已经看清了形势,虽然摆在他们面前的选择看起来不是那么理想。
东方的胜利
公元前23年,奥古斯都接见了来自帕提亚的普拉提斯的使者,与普拉提斯竞争王位的提里达提斯(Tiridates)更是亲自来到了罗马。他们二人都被带到了诸位元老面前说明来意。显然,提里达提斯希望罗马人出兵助他对抗普拉提斯,而普拉提斯当然希望罗马人不要出兵。正是因为他们二人的到来,阿格里帕才被派去了东方准备大举入侵帕提亚。[398]
奥古斯都推迟了他本人的行程。不过,在公元前21年下半年的时候,他应该已经动身了。他先在斯巴达待了一阵子,然后来到雅典。接着,他和当地人发生了一些冲突。雅典娜神像上有血溅到了他的身上。至少,据说如此。于是,奥古斯都及早离开,去了萨摩斯岛(Samos)过冬。反正他本来就要去东方的叙利亚。[399]
此时,普拉提斯已经得知奥古斯都即将率军前来。帕提亚政治史
的详细情况大多未曾被记录下来,但我们可以猜测他和提里达提斯之
间的争斗尚未了结。同时,至少有一些帕提亚贵族认为提里达提斯有
可能取胜,便选择了反对普拉提斯。因此,普拉提斯的地位岌岌可
危。为了保住王位,他只好向奥古斯都求和。公元前53年被帕提亚人
缴获的罗马军旗完璧归赵。当时被俘虏的罗马人也被送了回来,虽然
其中的某些人或许已经在帕提亚过上了幸福的生活,毕竟,这中间隔
着足足三十年。罗马人还试图干涉亚美尼亚(这是罗马和帕提亚相争的
区域)的政事,想要扶植一位亲近罗马的国王。为此,提比略受命率军
去贯彻罗马的意志。接着,奥古斯都开始着手于东方的整体布局。他
扶植了一些小国的附庸国王。
此次东征虽然有雷声大雨点小的嫌疑,但还是给奥古斯都带来了
一场大胜。普拉提斯保住了他的王位,却被迫做出了外交上的让步。
最重要的是,罗马的霸权地位得到了承认。奥古斯都得以宣布东方边
境上断断续续地持续了三十年的冲突就此告终,罗马建立了霸权。这
是克拉苏和安东尼都未能取得的成就。虽然按照罗马的传统,凯旋是
需要经过战斗的,但普拉提斯未经交战就做出了重大的让步也是很能
振奋人心的事情。在罗马人看来,帕提亚人是波斯人的继承者,他们
传承的是一个伟大的古代帝国。公元前5世纪的希腊人就曾经受到他们
的威胁,希腊城邦击败波斯和一百多年以后亚历山大征服波斯都是古
典时代最为重要的历史时刻。现在,奥古斯都让古老的波斯帝国屈服
于罗马的霸权(至少,他是这么宣布的),让罗马人又朝着征服世界的
终极目标迈出了一大步。而且,奥古斯都仅在抵达叙利亚以后的短短
数月之内就光凭武力威胁完成了这一壮举。
奥古斯都大事渲染了此次胜利。他曾经在世界西端的高卢和西班牙取得过胜利,现在他更是把自己的威名传到了遥远的东方。被带回来的那些军旗将被放置在完工以后的罗马城中心大广场上的复仇者马尔斯神庙(Mars Ultor)里。在广场和神庙竣工以前,这些军旗会被暂时保存在卡皮托里翁山上的另一座马尔斯神庙里。[400]奥古斯都又得到了一些荣誉:他的生日成了节日,人们会在那一天举办献祭仪式和庆祝的比赛;他返回罗马的10月12日也被定为奥古斯都节(Augustalia),同样会有献祭仪式;奥古斯都进入罗马城的那扇大门处会设立一座旅人庇护者幸运女神(Fortuna Redux)圣坛。[401]在进城之时,奥古斯都骑着马,带着队伍展开了游行。这不是传统的凯旋仪式,但他显然想表现得像是一次凯旋。对于这套赞美归来的征服者的仪式,罗马的政治精英们很配合。人民和元老都谨遵安排,热烈地欢迎奥古斯都归来。后来,这还形成了一项传统。
在公元前19年返回的奥古斯都有着非常稳固的地位。这几年时间
里反复发生的暴力事件已经让元老们苦不堪言,平民的种种举动无疑
表明了他们不信任元老,希望奥古斯都来统治他们。执政官选举活动
多次失控,元老们甚至不得不请奥古斯都来为他们指定执政官。与此
同时,奥古斯都则在一帆风顺地处理各地城市、王国的事务,并且把
罗马的势力延伸到了已知世界的边缘。从公元前23年开始的混乱状
态,充分说明了元老们已经无力掌控局面,只有奥古斯都才有维持秩
序的权威。现在,奥古斯都回到罗马来向各位元老提供他们自己无法
获得的东西:安全和秩序。但是,要获得这种秩序就必须接受帝国制
度的新规矩。罗马的政治精英们即将和奥古斯都展开划时代的政治谈
判,用自由换取安全,并且接受奥古斯都以君主的身份统治罗马。
[378] Dio, 54.1; Res Gestae , 5; Suetonius, Augustus , 52.
[379] 一份配给相当于养活一个成年男性的食物量,十二份粮食配给的价值大约为八十赛。
[380] Res Gestae , 15.
[381] 虽然奴隶很可能被雇来建造建筑,但奴隶是比较昂贵的资产。自由民更适合这种不定期出现的临时工作。
[382] Janet DeLaine, “Bricks and Mortar: Exploring the Economics of Building Techniques at Rome and Ostia”, Economies beyond Agriculture in the Classical World , 271-296, edited by David J. Mattingly and John Salmon (London: Routledge, 2000).读者也可参考Janet DeLaine, The Baths of Caracalla: A Study in the Design, Construction, and Economics of LargeScale Building Projects in Imperial Rome , Portsmouth (RI: Journal of Roman Archaeology, 1997), 201。
[383] Romilda Catalano, Acqua e acquedotti romani: Fontis Augustei aquaeductus(Naples: Arte Tipografica, 2003), 60.
[384] 请参考Peter Garnsey, Famine and Food Supply in the Greco-Roman World: Responses to Crisis (Cambridge, UK: Cambridge University Press, 1988); Tom W. Gallant, Risk and Survival in Ancient Greece: Reconstructing the Rural Domestic Economy (Oxford and Stanford: Stanford University Press, 1991)。
[385] Res Gestae , 5.
[386] 这是狄奥在54.1当中对此事的解读,虽然他不是很明白奥古斯都为什么要作这样的政治秀,因为狄奥认为奥古斯都从公元前31年开始就已经是一位专制君主了。
[387] 关于各个事件发生的日期,我们主要依靠于卡西乌斯·狄奥的文本,但在某种因素的影响下,狄奥不是很确定公元前22年至公元前19年各事件的发生日期,我们只能用各种资料拼凑起这几年的时间线。
[388] Dio, 54.6.
[389] Dio, 54.6.
[390] Dio, 54.11.
[391] Dio, 54.10.
[392] Dio, 53.24.
[393] Dio, 53.24.
[394] Velleius Paterculus, 2.91-92.
[395] Res Gestae , 12记载了罗马城中要员和执政官卢克里提乌斯曾经前往坎帕尼亚迎接奥古斯都归来。Res Gestae , 11提及在维尼奇乌斯和卢克里提乌斯担任执政官的 10月12日举办了献祭仪式。奥古斯都在Res Gestae ,6中声称他在此二人担任执政官期间得到了风纪官(Cura Morum)的职责。看起来,当奥古斯都返回意大利之时,萨图尔尼努斯已经不是执政官了。而维尼奇乌斯在10月12日或者稍晚一些的时候已经受任为执政官。
[396] Dio, 53.26.
[397] Suetonius, Augustus ,72.
[398] Dio, 53.33.
[399] Dio, 54.7; Plutarch, Moralia 207 F(罗马谚语)。
[400] Dio, 54.8; Res Gestae , 29.
[401] Res Gestae , 11.
第十六章 奥古斯都的秩序
时至公元前19年,元老们已经熟知他们应当为得胜归来的奥古斯都准备好什么东西。在阿克提翁战役结束和克莱奥帕特拉死后奥古斯都返回罗马之时,他们都表决同意给他献上了诸多荣誉。当奥古斯都在公元前24年从西班牙胜利返回之时,元老们又给他颁发了新的荣誉。所以,在公元前19年,元老们群策群力、绞尽脑汁地给奥古斯都准备了神庙、献祭和其他宗教类荣誉。也许有很多人曾经在公元前22年暗自庆幸奥古斯都离开了罗马。但现在,所有人都至少得表现得无比欢迎奥古斯都带着“幸运”返回意大利。
在奥古斯都回到罗马的第二天,元老院表决同意给奥古斯都的妻子莉薇娅的两个儿子提比略和德鲁苏斯(Drusus)颁发荣誉。提比略出生于公元前42年11月16日,其家族为赫赫有名的克劳狄乌斯家族。公元前39年,他的母亲莉薇娅在屋大维的要求下和当时的丈夫离婚了。同时,屋大维也和他当时的妻子斯克里波尼娅(Scribonia,就在她产下屋大维的唯一后代尤莉亚的那一天)离了婚。然后,莉薇娅和屋大维结成了夫妇。当时,莉薇娅还怀着德鲁苏斯,并且于公元前38年初将其产下。提比略的政治生涯开始于公元前22年凯皮奥密谋行刺奥古斯都一案。后来,他奉命率军去干涉了亚美尼亚的政务。[402]到了公元前19年末,虽然提比略已经有了一些军事经验,但他的政治生涯仍然只能算是刚刚开始。然而,他还是获得了裁判官的地位(拥有担任过裁判官之人的待遇)。德鲁苏斯则获准提前五年参选各个公职。[403]这些都是构建王朝的行为,就好像公元前24年马尔凯卢斯得到的拔擢一样。提比略和德鲁苏斯被认为是奥古斯都政权未来的关键人物,对他们的提拔非常有助于宣示公元前19年10月的奥古斯都已经重返罗马政局的中心。
第三位和构建王朝有关的人物当然是阿格里帕。他现在是尤莉亚
的丈夫,他们的第一个儿子出生于公元前20年。之后,他们还生下了
几个孩子,包括公元前19年的尤莉亚,公元前17年的卢奇乌斯,公元
前14年的阿格里皮娜(Agrippina),还有公元前12年的阿格里帕。阿格
里帕早在奥古斯都返回罗马之前就已经去了高卢。他先打了一场小规
模的战争,然后就去了西班牙,对付一个本应已经被制服的部落—坎
塔布里(Cantabri)。这场战争并不容易,阿格里帕还得带着纪律不佳
的士兵作战。不过,他还是终结了这场战争,并且获许举办一场凯旋
仪式,但他拒绝了。虽然在奥古斯都共和国时代曾经有其他人举办过
凯旋仪式,但是从公元前19年起,我们忽然就再也看不到皇帝以外的
人享受这种传统荣誉了。[404]阿格里帕的行为给未来的将军们立下了
范例。从此以后,只有皇帝才能享有军事胜利的荣光。原先杰出的将
领都能得到的赞美之词“imperator”也渐渐地成了君主的专属称呼。
不过,拒绝举办凯旋仪式并不意味着阿格里帕要急流勇退。他既
不是在谦让,也不打算退隐。阿格里帕的女儿维普萨尼娅(Vipsania,
之前的一段婚姻里所生)和提比略成了婚,进一步巩固了他在王朝当中
的地位。公元前18年,屋大维在公元前23年取得的保民官权力失效
了。这份权力固然堪称独一无二,但还带着共和国官制的陈旧规矩—
由选举产生、任期有限,虽然不像其他官职一样有同僚。这种缺憾在
公元前18年得到了弥补。这一年,阿格里帕和奥古斯都一起得到了保
民官权力,阿格里帕就此正式成为奥古斯都的政治伙伴。而且,他也
处在王朝的中心。在奥古斯都死后,这个王朝也将延续下去。或许,
人们不确定如果奥古斯都死于公元前23年的疾病,他的政权会遭遇怎
样的命运。但是,公元前19年的安排无疑说明了就算奥古斯都逝世,
他的家族也会继续统治罗马,阿格里帕会成为掌舵者,提比略和德鲁
苏斯会从旁协助。
奥古斯都在公元前19年的安排还厘清了他和两位执政官之间的关系。在公元前22年之后比较动荡的那几年时间里,并非执政官的奥古斯都常常表现得就像是拥有执政官的权力一样。公元前19年,他取得了执政官权力的名分。当然,他其实早就有了执政官的权力。[405]公元前19年和公元前18年的改革标志着罗马政治的转型。一些研究罗马宪法的历史学家认为此时有第三份重大的协定,修改了之前公元前27年和公元前23年的两次协定。然而,这第三份协定其实不存在。首先,我们看不到明显的协商过程。奥古斯都看起来没有和另一方势力展开谈判。而且,此时的两位执政官都是奥古斯都的人,他们帮助奥古斯都在公元前19年末异常迅速地完成了奥古斯都的改革。等到阿格里帕在公元前18年取得保民官权力之时,奥古斯都早已安排好了构建王朝、确立全新政治秩序的计划。
时至公元前18年,奥古斯都已经掌握了传统政治生活里的所有领域。而且,奥古斯都政权在坚定不移地公然构建王朝。当初马尔凯卢斯的擢升或许还让奥古斯都感到有些窘迫,但年轻的提比略和更加幼小的德鲁苏斯看起来并没有遇到类似的麻烦。这当然也和阿格里帕有着密切的联系,因为他的儿子都是奥古斯都的直系后代。当初有传言称他和马尔凯卢斯相争,但现在没有人再谣传阿格里帕要打压提比略和德鲁苏斯。奥古斯都和阿格里帕共同领导着这个皇室,而提比略和德鲁苏斯都是这个家族的后起之秀。罗马的政治前途就在奥古斯都的皇宫里,奥古斯都的家族正打算世世代代地统治下去。
买下罗马
奥古斯都的权力向来源于他对自己的政治根基的掌握,而这种控制力又和他对国家资源的利用密切相关。换言之,资金是奥古斯都政权的稳定性之源。在公元前44—前43年的战争结束以后,三头同盟的私人关系网络垄断了罗马的权力和资源。到了公元前19年,已经有整整一代的罗马人依附于这张关系网络而成长起来了。一百年以后,史家塔西佗对奥古斯都的崛起之路做出了这样的评价:
奥古斯都以赏赐拉拢军人,以粮食收买民心。他对所有人都许以闲适的美好生活。其势力逐步壮大。他顺利无阻地将元老院、民选官乃至法律的角色都揽于己身,因为他的大敌都已经倒在了战场上或者成了公敌。剩下的贵族们更愿意当他的奴隶,他们拿到了各种荣誉和财富,在新的秩序里沉溺于安逸的日子。地方省份也对这种新的状态感到很满意,它们本就畏惧着元老院和人民的权力,既担心高层人物相争会波及自己,也不愿成为贪婪的高官眼中的鱼肉,因为就连法律也不能阻止他们动用暴力、人脉以及最强大的金钱来为所欲为……[406]
把国家的资源分发给人民的一种最直接的手段就是殖民。[407]在共和国的最后几十年里,罗马人一般在军团士兵退役之时设立殖民地。奥古斯都也曾在战争结束以后让老兵们定居在殖民地里。[408]不过,他还设立了一些看起来没有多少军人定居的殖民地。[409]奥古斯都时代的殖民规模极大。我们没有掌握完整的殖民地名单,意大利以外的殖民地只有一部分为人所知。但整个奥古斯都时代设立的殖民地很可能不下于六十个,涉及的殖民者为三十万到六十万男性,其中应该还有一些不是罗马公民。
就算内战已经结束,奥古斯都也得投入大量资金来满足军队的需要。他声称为了给老兵们寻找土地,他花了八亿六千万赛。因为设置殖民地比较困难,老兵们退役的报酬渐渐地从土地转变为现金。某些老兵或许会更喜欢现金,因为这样一来他们就可以返回意大利和家人相聚,用这笔资金来自行挑选定居地,而不是迁居至地方省份的殖民地。从公元前7年开始,奥古斯都又花了四亿赛来给老兵们发放奖金。[410]在奥古斯都时代一共有不下于三十万名老兵退役并得到了金钱或土地报酬。但奥古斯都的慷慨并不仅限于此。他在《圣奥古斯都行述》中称自己在公元前29年给所有的殖民者都发放了一千赛的奖金,用以庆祝阿克提翁之战的胜利。他还有可能在后来时不时巡视意大利的时候也大方地发放了奖金。[411]
奥古斯都还得解决平时的军费支出问题。从公元前30年到公元14
年,奥古斯都一般都掌握着二十八个军团大约十四万人的军队。这个
数目稍多于罗马成年人力的十分之一。在奥古斯都统治末期,因为潘
诺尼亚(Pannonia)的叛乱和日耳曼尼亚的战事的存在,这个比例有所
上升,也许达到了总人力的百分之十四。[412]服役的相关规定也变得
更加固定了,通常时限为十六年,后来延长到了二十年。[413]最后,
奥古斯都专门新设了一个军费管理部门来负责为士兵们提供薪水和奖
金,其第一笔资金就出自他自己的资产。同时,他开始为了军费而征
收百分之五的遗产税。富人们并不喜欢这个举措,因为他们不认为自
己应该把财产分享给军队。[414]
奥古斯都也继续支持着平民。继公元前23年以后,他在公元前11年(每人四百赛)、公元前5年和公元前2年(每人两百四十赛)都给平民送出了礼物。[415]在他死后,罗马人民(大概是罗马的平民)又得到了每人一百六十赛总额四千万赛的奖金。奥古斯都一生给罗马人民发放的奖金加起来超过了五亿赛。这个数字肯定会让元老们深感震惊。而且,这还没算上他在粮食供给、修建水渠还有各种庆祝活动上花出去的钱。
用金钱换取士兵(及其家人)和平民的支持是比较直白的事情。相比之下,罗马精英们的问题要复杂一些。元老们秉承传统,认为自己理应是罗马的统治者。但现在,奥古斯都夺走了他们的统治权。不过,当时的政治是比较松散的个人化政治。人们往往只关心自己有着怎样的地位,而这个地位又是否与其家族威望相称。
这种松散的性质让奥古斯都有了掌控精英阶层的余地,他需要做
的就是让这些精英感觉自己得到了认可与尊重。于是,他让贵族们分
享了皇权带来的好处,让他们得以免受革命的威胁,安然享受财富。
贵族的地位由此和奥古斯都本人及其政权都挂上了钩。为了让贵族们
感受到尊重,奥古斯都还得做一些小事。他需要记住人们的名字,送
生日礼物,对他们的家族活动示以尊重,在参加讨论的时候平等相
待。总而言之,他要致力于和贵族们维持良好的私人关系,以便相应
地维持住彼此之间的政治关系,从而巩固他的政权。
奥古斯都控制着公职的任命权。也就是说,他有权决定他人的政治前途。他既可以让人擢升至高位,也可以轻易地打压别人。不过,他大概很少觉得有必要去用这种权力铲除某些可能对现政权有异心之人。在奥古斯都时代的后期,执政官的职位常常由出身名门者担任。奥古斯都允许他们取得这样的高级职务恰恰证明了奥古斯都的共和国可以平稳地运转下去,出身显贵的元老们可以在奥古斯都的统治下拥有光明的政治前途。[416]
奥古斯都凭着他的权力把某些交游甚广的贵族纳入了他的关系网络,进而使得任何反对奥古斯都的举动看起来都像是在自取灭亡。无论有意或是无意,奥古斯都最终对元老们采用的策略都顺应了元老们原有的等级秩序。他没有必要把元老院里的人都换成自己的坚定支持者,因为他大可以用权力来对元老们施恩。最后,元老院里的人不是已经受过奥古斯都的恩惠,就是正在求取这种恩惠。
奥古斯都只有在威胁到元老们的个人地位之时才会遇到明显的阻
力,比如,他当初审定元老资格的时候。[417]公元前28年,奥古斯都
改革了元老院的人员组成。这是他恢复共和国的举措之一。在公元前
18年,他再度开始考虑元老的资格问题。这一次,他设计了一套比较
复杂的元老选举制度。奥古斯都会挑选出三十个人,而这三十人每人
会再选出五个人。然后,这里获选的一百五十个人要进行抽签。剩下
来的只有三十个人,他们就是第一批合格的元老。而之前奥古斯都选
出来的三十个人会回到未获选的名册里去。接着,第一批合格的三十
名元老要按同样的程序选出一百五十人,经过又一次抽签,得出第二
批合格的三十人。然后第二批元老又要再选一轮。这整个流程会一直
持续到产生了三百名合格的元老为止。如果说有人想要把奥古斯都当
作一位伟大的政治家,他最好首先来看一看奥古斯都设计的这套制
度。这套制度导致的结果是无比的混乱和腐败,它让很多适合担任元
老的人因为被人遗忘或者没抽到签而落选。某位德高望重的元老发现
他的儿子还在担任元老,而他自己却被开除了。于是,他撕破了自己
的衣服,向人们露出他在为罗马效劳的岁月里留下的伤痕(共和国时期
也有这种例子)。还有一位元老恳求辞去自己的职务,让他落选的父亲
得以留在元老院里。后来奥古斯都本人也察觉了这套流程的失败之
处,于是便拿起了名单,亲手挑选(或开除)元老。[418]
五年后,奥古斯都想到了一个新点子,他调整了在人口普查中被
评为元老的财产要求。共和国时期的元老资格大概是十万赛,奥古斯
都把它抬到了一百万赛,然后立刻就发现了问题。他肯定是想通过抬
高标准来排除那些财力相对较弱、名望相对较低的家族。[419]但是,
他似乎没能较为准确地预测到哪些家族会被排除出去,有些声望较高
的家族忽然发现自己失去了当元老的资格。于是,奥古斯都感觉到有
必要资助这些虽然较穷但是很受敬重的元老。我们可以猜想一下,依
靠奥古斯都的资助来维持元老的地位应该不是什么很光彩的事情。
[420]
奥古斯都实施这些改革的目的并不是除去那些和他作对之人,而是提高元老院的威望。虽然某些元老或许因为一度失去了元老的资格(无论是由于意外还是有意)而感到有些不满,但是元老们的整体地位是得到了提高的,因为他们经过了更加严格的筛选。给奥古斯都带来政治压力的是对个别元老的冒犯。奥古斯都政权因人们追求各自的政治前途而团结了很多人,但在改革元老院的事情上,这种现象反而让他遇到了一些阻力。
奥古斯都的权力限制了元老院的政治地位,但他让元老院在行政
中发挥了更大的作用。他设立了很多官职来负责具体的职务,一般是
让多名官员共同管理一项事务。公共建筑、道路、水渠、台伯河堤与
行洪渠(台伯河素有在冬季因暴雨而泛滥的恶名)还有罗马城的粮食供
应都有了专门的元老官员来负责处理,元老的职业生涯因此变得更为
复杂了。同时,这也是他们在公众面前的新形象。在奥古斯都时代,
元老们通过官职(而不是政治、军事成就或者家族背景)来显示自己的
地位。而这种对于官职的需求让他们深陷于奥古斯都的制度当中,他
们需要奥古斯都的制度来为他们提供地位。[421]罗马精英的本质在不
知不觉中发生了转变。
军人、平民、元老都渐渐地融入了奥古斯都的新制度。他们或是越来越依赖奥古斯都为他们提供金钱,或是为各种荣誉所征服。奥古斯都的权力的本质就在于这张可以满足所有人的关系网络。正如塔西佗所说,奥古斯都把他的支持者都团结在了一起,又对所有的反对者加以利诱。帝国的权力收买了共和国的所有遗产,让自己的地位变得稳如磐石。于是,政治革命成功、掌握了大量资源的奥古斯都开始在文化领域发起另一场与之相称的革命。
文化领域的革命
革命是很奇特的事情。现代的革命者想要改造世界,为此,他们
会夺取政治权力,颠覆原来的政权,还会大力地扫除旧政治秩序的任
何一点残余。但是,掌权以后又该做些什么呢?改变政局,砍掉国王
的脑袋或许并非难事。但要真正地改造世界就得给整个社会带来一场
深刻的革命,改变人们的旧思想,从而铲除原先让国王和朝廷得以存
在的根基。文化领域的革命比政治革命要难得多。很多政权都在这个
阶段遭遇了挫折,陷入无边无际的苦海,导致无数人流血死亡。
和现代的革命不同的是,在奥古斯都的革命当中,没有某种引领
人们前进的意识形态。至少据我们所知,这场革命的领导者并非因改
造世界的意识形态承诺而行动的。不过,这不是在说他们认为罗马的
社会已经完美或趋近完美了。他们毕竟才经历了长达一个世纪的内
乱,奥古斯都的胜利本身就是这一百年历史发展到顶峰的结果。这足
以说明罗马的政治制度有着一些严重的根本性问题。当时的罗马人同
样认为他们遇到的是社会问题,虽然他们对社会的理解和我们有一些
差异。我们最好把他们自己指出的根本性问题称为“道德滑坡”。
在罗马人眼里,道德是政治美德和习俗的根基。道德滑坡意味着
人们的社会、政治行为都变得恶劣起来。道德的范畴涵盖了人和神、
家族、国家之间的关系。道德是一个政治概念。而这种政治文化的堕
落是因为罗马人征服四方建立霸权,获得了太多的利益,导致罗马社
会发生了转变。财富催生出奢靡之风,对财富的渴望扭曲了政治决策
的过程。贪恋财富的罗马人不再是合格的公民,反而互相争斗不已。
而且,这种转变影响了罗马社会的所有阶层。
其实,这种关于罗马人道德败坏的说法是不太可靠的。这种理论
首先设想了一个存在于道德滑坡之前的黄金时代。然而,罗马人或许
认为这个黄金时代大概就在公元前3世纪或者更早一些的时候,但至少
在我们看来,罗马历史上没有哪个时期堪称这种黄金时代。不过,这
种精心炮制出来又简单易懂的说法往往能够引得很多人相信。相比之
下,真相反而没有那么可信了。历史学家们常常会遇到这种毫无胜算
的辟谣之战,因为如果罗马在公元前1世纪遇到的混乱不是一个简单的
集体道德败坏的问题,那么人们很可能就得面对一个更加难以理解、
难以捉摸也更加复杂的问题了。简单的故事能够慰藉人心。而且,道
德败坏论还很合罗马精英的口味,因为这种理论同时指明了一条简单
的解决之道:恢复以往的道德。
罗马的政治思想家们难以设想出新世界的模样,却可以比较轻易地给旧世界蒙上新的面纱。奥古斯都在公元前28年和公元前27年就尝试着恢复一种旧的道德秩序。他改革了元老院的人员构成,开展了人口普查,举办了相关的仪式。最引人注目的是,他在公元前28年修复了一些神庙。这都表明了他愿意恢复一种古老的社会、宗教秩序。这些大体上算是制度层面的改革。此外,我们还能在一首情诗当中发现奥古斯都的其他想法。
普罗佩提乌斯的优美诗作曾经生动地帮助我们理解了奥古斯都时
代早期的文化。此外,他还有一首诗反映了他的女友君提娅在某项
“法律”被撤除之时深感喜悦。曾经,这对爱侣因为这项法律会迫使
他们分离而潸然泪下。但最后,普罗佩提乌斯得意地写下了这样的话
语:“恺撒能征善战,但他的战功在爱情面前分文不值。”[422]我们
无法确切地得知什么样的法律会让这对情侣分开。也许,这项法律要
求所有罗马人必须结婚,甚至规定了非常严厉的惩罚,以至于普罗佩
提乌斯这样坚定的不婚者也不得不违背本心。或许,这项法律还让通
奸被归入了刑事犯罪。普罗佩提乌斯想象了他的庆婚队伍经过君提娅
宅前的景象,为自己失去了爱情而流下了悲伤的泪水。普罗佩提乌斯
和君提娅似乎不可能结婚,因为像他们这样痴迷于爱情之人是不可能
接受婚姻的。
普罗佩提乌斯还在诗篇里明确地提出了意识形态的区别。这项法律和军事有关,其目的是强制要求罗马人生下合法的孩子,以便为罗马的军队提供更加充足的人力。普罗佩提乌斯则声称:“我的血脉不会成为军人。”他认为爱情是超然于恺撒的权力以外的事物。恺撒固然有军队,但他不能控制爱情。在普罗佩提乌斯所写的诗作里,爱情的领域是自由的,它不受奥古斯都的掌控。
其他人看起来也有普罗佩提乌斯这样的想法,那项法律没能在会议上得到通过。罗马的情侣们或许在法律被撤除以后的那天晚上以情侣专有的方式进行了庆祝。普罗佩提乌斯的这首诗面世于公元前1世纪20年代中期,未能出台的那项法律肯定出现在公元前1世纪20年代初。不过,虽然普罗佩提乌斯热烈地庆祝了爱情对恺撒的胜利,但恺撒并不是轻言放弃之人。公元前19年以后,地位更加稳固的恺撒即将着手进行道德改革,向普罗佩提乌斯和其他的情侣证明,恺撒的大权同样可以控制爱情。
奥古斯都的立法工程涉及的范围极广。公元前18年出台的一些早期的法案在后来得到了修改或者延伸。而且,帝国政权十分注重宣扬道德教化。帝国皇室被推出来成为优秀道德的榜样,以身作则,行为世范。他们鼓励人们在艺术作品中表现罗马的传统价值观,对道德模范人物加以褒奖。奥古斯都本人似乎还声称他家族里的女性会给他制作衣服(织衣是罗马已婚女性的传统),虽然传统文献并没有提及皇室女性对这种强制的劳动作何感想。[423]此外,奥古斯都还立法对下列事情做出了或多或少的规定:解放奴隶、过度铺张、衣着、元老及其子孙的婚配、遗产分配、性行为、叛逆。
对性生活加以规定是因为罗马人在这方面的道德观念和现代人有
着很大的区别。罗马人结婚只是为了生育子女,传宗接代,爱情和婚
姻毫无关系。奥古斯都立法鼓励罗马人结婚。公元前18年,奥古斯都
出台了一项法律规定离异女性应当于六个月内再婚,丧偶者可以有一
年的宽限期。后来,在公元9年,这项法律得到了修订,让离异者有了
一年半的宽限期,丧偶者则是两年。看起来,违反这项法律的惩罚和
继承、分配遗产有关。[424]未婚男性同样会遭到类似的惩罚,其继承
权也会受到限制。奥古斯都还实行了一项财产税,尤其针对未婚者的
财产。此外,未婚者似乎不得观看戏剧。[425]
生育了后代的男女则会得到奖励。一般的罗马女性需要有男性代
表才能参与法律事务,而拥有三个孩子的女性(得到自由身的奴隶需要
有四个)会获得独立的法律地位。拥有孩子的男性元老可以更快地在政
治道路上得到晋升。而且,这种奖励不只局限于政治精英阶层。有一
次,奥古斯都正在巡视意大利各地区。大概他是在访问各地的殖民地
和其他聚落,同时也是在巩固他和人民之间的关系。此时,他宣布给
所有为人父者发放奖金,每拥有一个孩子就可获得一千赛。鉴于当时
一名罗马军人的年薪是九百赛,这次的奖金数额堪称非常巨大了。而
且,整个意大利的儿童公民大概有一百万。所以从帝国的角度来看,
这也是一笔不小的支出,虽然这应该只是一次性的奖金。[426]
这一系列法律引发了激烈的争论。某些人为此而集会示威,公然表示抗议。奥古斯都不得不对法条做出了修改,而且有可能是两次。[427]有一次,在奥古斯都统治末期,人们正在剧院示威。面对示威者,奥古斯都把日耳曼尼库斯(Germanicus)和阿格里皮娜放在膝盖上玩耍,用以展示天伦之乐。[428]公元9年,又有人在剧院里示威。于是,奥古斯都把骑士阶层召集到了广场上,对他们进行严肃的批评。[429]奥古斯都还曾于公元前18年在元老院里宣读昆图斯·凯奇利乌斯·梅提卢斯·马其顿尼库斯(Quintus Caecilius Metellus Macedonicus)在公元前131年发表的演讲词“论增加人口”。[430]留传下来的文字寥寥无几,但我们还能从中看出全文的基调:
罗马的公民们,和妻子共处着实是一件麻烦的事情。如果可以,我也愿意赞成不娶妻。但是,大自然的安排便是要我们不得不放弃短期的欢愉,为长远的种族延续而忍受下去。[431]
奥古斯都宣读这份演讲词的目的是把他的改革和罗马的传统道德
观念联系在一起。即便梅提卢斯当年没能成功地说服大家改革罗马婚
俗,他的演说词也能让奥古斯都的改革看起来有着熟悉的传统面貌,
掩盖掉其中的创新气息。因此,面对批评者,奥古斯都可以有底气地
声称自己干涉公民私生活的做法在罗马历史上有过先例。狄奥还记录
了奥古斯都在公元9年对不生育者发表的演讲。虽然我们不确定其准确
性如何,但从他的文本来看,奥古斯都重申了梅提卢斯当年的核心思
想,批评不生育后代者是在威胁罗马的未来,把个人私欲放到了生儿
育女的职责之前。[432]
奥古斯都还出台了一项法律,宣布通奸入刑。在此处,通奸的定
义是已婚女性和自己的丈夫以外的男性发生性关系,双方都会被判定
为有罪。但已婚男性可以合法地与自己的妻子以外的女性发生性关
系,只要该名女性未婚即可。性工作者是不受该法律约束的,她们只
需依照这项或者另外某项法律的规定进行登记。通奸入刑既约束了一
些年轻人的行为,也有助于促进合法后代的诞生。[433]根据这项法
律,通奸者会被剥夺财产,遭到流放。奥古斯都还宣布丈夫都有义务
起诉有嫌疑或者确实犯下通奸罪的妻子。假如丈夫不曾起诉,那么在
该名女子被指控的六十天以后,其他人也可起诉。如果罪行属实,那
么她的丈夫就必须与她离婚,不然就会遭到起诉。[434]
这些法规未免有点道德恐怖的嫌疑。虽然那些鼓吹道德教化者总
是在大肆抨击自己所处的那个时代,认为世风日下、人心不古,但他
们的说法通常没有什么站得住脚的依据。例如,就罗马而言,他们似
乎并没有统计过各个时期曝光的通奸案例数目,也就无从展开数据分
析,但在共和国晚期和帝国时代之初,人们在卧室里做的事情显然比
在古典时代(或后来的其他时代)的其他时期受到了更多的关注。既然
没有人能够说得清哪个时代的通奸行为比较多,那么奥古斯都之所以
立法严惩通奸或许并不是因为通奸行为真的变多了,而是因为人们普
遍担心通奸行为发生而已。
诞生于奥古斯都时代的诗作和其他时代一样热衷于讲述政治人物
的爱情故事,而且同样秉持爱情不受婚姻关系的限制,爱人不限于配
偶的理念。诗人们笔下的爱情往往和传统道德观念推崇的生活方式形
成鲜明的对比。关于当时的大人物尤里乌斯·恺撒、马克·安东尼还
有奥古斯都本人的那些逸闻都会着重描写他们自由地追逐异性的行
为。不论是以罗马人的标准还是现代人的观念来看,这些逸闻都经常
涉及通奸。[435]有传闻称奥古斯都尤好处女,有专人寻来非常年幼的
女子以供他淫乐。[436]还有一些相当露骨的传闻称他和麦奇纳斯的妻
子提兰提娅有着长期的情人关系。在惹得众人不满的通奸法出台以
后,甚至有传言称奥古斯都在公元前16年一度急着离开罗马,去高卢
处理公务,以便和提兰提娅一起躲开旁人的视线。[437]如果这种说法
属实,那么奥古斯都就和他的朋友的妻子维持了至少十五年的半公开
的情人关系,甚至在通奸入刑以后成了罪犯。然而,我们不难想象,
奥古斯都出台的约束私生活的法律大概使得很多罗马人都开始怀着恶
意去对他本人的私生活说三道四。
无论其本人是否有此类行为,从古至今很少有政治人物会公然主张保护通奸者的权利,但奥古斯都时代的这些法律的意义并不在于打压不正之风。重要的是,奥古斯都在宣扬某种理想的社会图景,并且在用法律的手段来强制实现这种图景。无论男女,罗马人都有繁衍后代的义务,他们理应为国家生儿育女。男孩子将来要成为战士,女孩子将来要生出下一代的战士。罗马人关心他们的人口数目,担心罗马人会越来越少乃至没有新生代的战士来捍卫他们建立的这个大帝国。
因此,所有罗马人的私生活都不得不服从于帝国的约束。关于婚姻的规定是把国家的权力延伸到了公民的家中,这些法律之所以不受欢迎大体上是因为它们切实地影响了罗马人的生活。当然,拒绝结婚者可能有各种各样的私人原因。但我们同样必须注意的是,罗马人实行的是均分继承制。也就是说,每一位合法的子女都可以继承到等额的家产。在这种继承制度下,如果一个家族长期只有两个左右的孩子,那么保持家族的地位并不是很难的事情。但随着孩子数量的增加,其难度会逐步地提高。况且,婚姻关系的缔结是以双方的地位为依据的,而地位又最终取决于财富。所以,独生子女很有可能与出身更加高贵者成婚。总而言之,均分继承制大体上意味着较小的家族比较容易提高自己的社会、经济地位,而较大的家族比较容易没落。
应对这种情况的一种有效手段就是好好地安排婚姻。然而,奥古
斯都却出台了法律强迫大家尽快成婚。有些人本来会有意地推迟结
婚,以便积攒起更多的财富,和出身更好的对象成婚,或者通过晚婚
来尽量避免生育过多的子女,个别人甚至还需要照顾到某个子女过多
的兄弟姐妹。但在奥古斯都出台新法以后,他们就必须放弃这些打算
了,不然就会受到法律的惩罚,失去继承家产的资格。在这种限制
下,大家族的子弟难以找到合适的婚配对象。于是,一些或者说很多
罗马人开始试图规避法律的约束。他们会定下期限较长的婚约,或者
和年纪太小、无法成婚的女孩子订婚。但在后来,奥古斯都补上了这
些漏洞。或许有些人因此便尝试了一些在结婚后限制家族规模增长的
手段,比如堕胎、杀婴、减少性行为、避孕,虽然我们几乎对罗马人
的夫妻生活一无所知。
关于奥古斯都的新法遭到反对的原因,除了上文所提的这些非常
实际的考虑以外,观念问题至少有着同样重要的地位。一些人也许和
梅提卢斯的观点一致,认为娶妻是大自然强行施加于己身的不幸之
事,妻子的存在会妨碍他们过上幸福的生活,因为罗马女性一般都会
在家庭里拥有一定的地位,而且至少有一部分女性是反对丈夫拥有情
人的。某些罗马男性或许真的过着当时的情诗里描写的那种生活,和
别人的妻子有着私密之极的关系,结婚大概不利于他们保持这样的放
浪作风。还有一些罗马人也许是难以忍受国家的权力以这种方式运
行。罗马的历史或许看起来像是在鼓吹克己奉公、为国献身的爱国精
神,但要求罗马人为了罗马的利益而繁衍后代仍然堪称令人震惊的侵
犯个人自由之举。更何况,生下来的男性还要为奥古斯都的政权在奥
古斯都的军队里为奥古斯都而战。这恐怕不是很能激发罗马人的性
欲。普罗佩提乌斯就曾经声称他的后代决不会为奥古斯都的帝国梦而
战,其他人或许也有类似的想法。
此外,奥古斯都的婚姻法还让罗马人的房中事有可能被别有用心之人加以利用。之前,一个人大概只能散布谣言说他的对手的妻子人尽可夫,但在奥古斯都时代,他或许就可以把她送上法庭了。男女之间的友情也有可能遭到歪曲,乃至毁掉双方的人生。我们也许还会好奇,对于这种事情,法庭究竟该如何判定证据的有效性。当时可不像现在这样有专人在酒店附近等着拍照做证。一般说来,法庭是不会对“没有合理证据”的事情做出判决的。不过,光是闹上法庭所引发的恶意流言或许就足以造成严重的伤害了。曾经关上门来解决的家务事,现在有可能被公之于众,损伤家族的颜面,甚至导致失去财产,惨遭流放。史家塔西佗对此做出了这样的评价:
民众变得更加可怕了,因为每一个家庭都有可能被告密者毁于一旦。[438]
奥古斯都的这些法律看起来秉持着古老的道德观念,对人民加以冠冕堂皇的约束,让人难以公然表示反对,同时也是皇权套在罗马人民身上的枷锁。[439]
黄金时代
公元前17年5月23日,元老院在执政官盖乌斯·西拉努斯的主持下召开了会议,讨论恺撒·奥古斯都和马尔库斯·阿格里帕主张庆祝的时代节(Secular Games)。这个节日标志着一个时代(saeculum)的结束,同时当然也意味着一个新时代的开始。在充斥着战争和内乱的一个时代结束以后,奥古斯都政权要为罗马人民献上的是一个满溢着希望与和平的全新的黄金时代。
有很多古老的传统在共和国晚期被搁置了起来,时代节也是如此。这项节庆的具体规定尚有争议。据我们所知,罗马人的上一次时代节是在公元前146年,再往前则是公元前249年。这项节庆有可能就是在公元前249年被创造出来的。当时,罗马人深感迦太基人的威胁。他们或许觉得罗马已经失去了诸神的祝福,自己必须做出一些特别的事情来赢回神明的宠爱。于是,他们去查了神谕书,最后认为罗马人得罪的是冥界诸神和罗马的先祖。因此,公元前249年时代节上的仪式庄严肃穆,类似于丧礼,其主旨就是为罗马的列祖列宗和冥界的神明献上敬意。此外,神谕还要求两次时代节之间要有一百零五年或一百一十年的间隔。这是为了让每一个人一生都最多只能参加一次时代节。也就是说,这项节庆的举办标志着有一整代的罗马人已经离世。现在,奥古斯都和阿格里帕即将改造这个原本规模较小而且比较庄重的活动。[440]
元老院在5月23日颁布了法令,试图尽量增加参与此次时代节的民众数目,将其打造为一次盛大的公共节庆。元老们允许各阶层的未婚者及本应受到婚姻法惩罚之人参加时代节。他们希望有尽可能多的人到场,因为这毕竟是所有人一辈子都只可能参加一次的节日。他们还命人用铭文记下了这次庆典,我们今天还能看到一个残缺的版本。[441]
我们掌握的史料始于5月31日夜里的献祭仪式,人们向诸位命运女神献上了九只绵羊和九只山羊。作为主持仪式的祭司,奥古斯都以其铿锵有力的声音带领着大家展开了祈祷。奥古斯都请求诸神让罗马人民的帝国得以继续扩张,变得更加伟大;让罗马人民和罗马军团都享有胜利与安康;让十五人祭司团(主持时代节的祭司)、罗马公民、奥古斯都本人及其家人都得到祝福。接下来是某种表演活动。然后,人们举办了一次神圣的宴会,享宴者是从罗马公民家中选出的一百一十位人妇。
第二天,奥古斯都和阿格里帕向朱庇特献上了公牛。接着是戏剧表演。然后,十五人祭司团宣布降低公民之妻为亡夫服丧的时间要求。在夜幕降临以后,奥古斯都主持了又一场献祭仪式。这一次,他向生育女神埃雷图娅(Ilithyia)献上了糕点。6月2日,奥古斯都和阿格里帕向朱诺献上了母牛。接下来是一场代表罗马女性的祈祷仪式,其流程几乎和前天夜里奥古斯都主持的那一场一模一样。这天晚上的献祭仪式是把一头怀孕的母猪献给伟大的母亲(Magna Mater)。到此为止的活动都谨遵时代节的传统,举办于台伯河畔的某个区域。
6月3日,庆典的中心转移到了奥古斯都的宅邸所在的帕拉提翁山上。人们向阿波罗和狄安娜(Diana)献上了糕点。五十四名少男少女合唱了由诗人贺拉斯(Horace)专门为此创作的一首圣歌。接着,人们转移到了卡皮托里翁山上。在那里,合唱团又唱了一次圣歌。然后,人们观赏了戏剧表演和马车竞赛。在这一天的活动即将结束之时,十五人祭司团宣布接下来有为期七天的希腊语和拉丁语戏剧表演。到6月12日,还有在竞技场里猎杀野兽的表演和马车竞赛。及至这一系列活动告终,人们的生活大概才恢复正常。
奥古斯都和阿格里帕把时代节改造成了一场极其隆重的庆典,其
中的寓意也发生了变化。庆祝时代节不再是为了安抚亡者,而是为了
展望罗马的未来。祈祷仪式是为帝国的扩张、为军团和罗马人民而举
办的,奥古斯都及其家人也得到了祈祷,这显然说明了奥古斯都的王
朝已经成为罗马的一大核心(我们也可以发现元老院和各位官员似乎都
没有被提及)。此外,这次的时代节不仅没有像以往一样为冥界的神明
献祭,反而把祭品献给了生育女神。这是在强调女性和生育的重要
性,赞扬那些即将给罗马生下子孙后代并且为其提供道德指引的母
亲。儿童的地位则体现在歌唱贺拉斯的圣歌的那个合唱团身上。6月3
日,这些宗教活动的举办地点及其本质都有了彻底的变化,节庆的焦
点转移至奥古斯都下令建造的阿波罗神庙。这座庙宇和阿克提翁之战
的胜利有关,而且和奥古斯都本人的居所相邻。此外,十五人祭司团
的领导地位看起来也是全新的设计,其首要目的就是让祭司团内的两
位领导者奥古斯都和阿格里帕得以主导节庆的流程。毋庸置疑,此次
时代节是属于他们二人的庆典。
儿童合唱团(两度)演唱的圣歌名为《时代之歌》(Carmen Saeculare),其内容完整地流传了下来。它的作者贺拉斯是当时最杰出的诗人之一,以抒情诗歌与讽刺诗著称。他看起来和麦奇纳斯的关系比较好,因而进入了奥古斯都身边的社交圈子。这首《时代之歌》开篇提及的是阿波罗和狄安娜,而不是冥界诸神。其主题显然也有着奥古斯都时代的特色:它请求诸神爱护人母,让青年茁壮成长,为奥古斯都要求人们生育后代、尽早结婚的法律赋予力量。然后,《时代之歌》请求命运女神和伟大的母亲让罗马的田地变得肥沃多产。接着,歌词的内容变成了罗马的建城史。不过,贺拉斯对罗慕路斯和雷慕斯着墨不多。他主要描写了埃涅阿斯逃离特洛伊,定居于意大利的故事。之后,《时代之歌》表示希望奥古斯都继续开疆拓土。最终,在比较和缓的曲调下,贺拉斯展望了和平、繁荣的未来。
时代节比较全面地展现了奥古斯都政权的意识形态。我们可以从中看到很多关键的主题:军事胜利、和平、罗马的繁荣、繁衍生息、神明的祝福、法律对罗马人民的约束。节庆活动的核心是对传统的罗马历史加以改编,然后呈现在大家面前。时代节本就标志着某个时代的所有罗马公民都已经离开了人世。这种比较罕见的节庆和希腊人对时代的认识有关。在希腊神话当中有所谓黄金时代的概念。据说,那是一个非常古老的时代,当时的人们无须劳作而能得到自己所需的一切,世界和平犹如天堂。然后,这种原始的理想社会渐渐消亡,后来的时代每况愈下。最终出现的是黑铁时代,充满了暴力与战争。
在诞生于晚期共和国的拉丁诗歌当中,我们常常能看见这种说法。堪称晚期共和国最优秀的诗人的卡图卢斯(Catullus)以及在奥古斯都时代创作了伟大的史诗《埃涅阿斯纪》的维吉尔都曾经运用过黄金时代的概念。[442]卡图卢斯虚构了一个他所处的世界在堕落之前的模样。而维吉尔则畅想了历史的进程会不可思议地逆转,人类会在某位救世主的带领下重新进入黄金时代。
这种认为每一个时代都变得越发糟糕、一步一步堕落下去的说法非常悲观。罗马人一度十分担心自己还会堕落到怎样的境地,但奥古斯都的时代节标志着罗马人的态度焕然一新:时代节即将开启的新时代并不是更加可怕的噩梦,而是再度出现的黄金时代;时代节展现的主题是生育、和平、青春和多产(人和田地)—这些积极向上的内容让人不禁想起了传说中黄金时代的美好图景。奥古斯都和阿格里帕由此宣布了历史即将重新开始,他们会带领人们开启新的元年。
《时代之歌》提及埃涅阿斯是因为奥古斯都尤其重视这个建城传说,奥古斯都时代有很多艺术作品都刻画了埃涅阿斯的故事。例如,罗马城中心的奥古斯都大广场和公元前1世纪第一个十年末期建成于战神广场的那个小巧却别致的和平圣坛。在圣坛墙上的浮雕当中,意大利娅女神(Italia,或和平女神)的形象周围充满了象征着生育的图景,意味着奥古斯都会带领大家再次进入一个和平且生机盎然的时代(如图9)。
奥古斯都政权致力于宣传埃涅阿斯主要是因为尤里乌斯家族自称起源于埃涅阿斯之子尤卢斯。而且,在公元前19年,维吉尔发表了他的史诗著作《埃涅阿斯纪》,重新全面地讲述了埃涅阿斯的传说。这部作品是拉丁语文学史上的传世经典,堪称最具影响力的拉丁语诗。其主要内容是描写埃涅阿斯如何克服了艰难险阻,从特洛伊来到意大利,并且在意大利顽强奋斗,带领其人民定居于拉提翁(Latium)。
《埃涅阿斯纪》呼应了《荷马史诗》中的内容,与《伊利亚特》
(Iliad)和《奥德赛》(Odyssey)都很相像。显然,维吉尔写作的用意不
是为人们提供信史,这部史诗的意义在于以其虚构的罗马建城史来促
使人们反思真正的罗马历史。埃涅阿斯的形象不只是意大利半岛上这
座新社区的创建者,他更是所有罗马人的缩影。埃涅阿斯开拓新土地
的故事能够让人回想起充满了阳刚之气的罗马男性,激起人们对个人
与政治的关系以及命运的本质的思考。为了寻找新的定居之所,埃涅
阿斯必须背弃他的故乡、妻子和爱人。他失去了父亲,还目睹了自己
的朋友遇害。他必须为一座将在许多个世代以后建立起来的城市而
战。他常常被视作一个有缺憾的英雄,人们会在他的身上看到教训,
进而深思一个罗马人应当怎样处事。埃涅阿斯几乎总是被描写为一个
尽忠尽责(pius)之人,他把自己的一生无私地奉献给诸神、人民以及
那个未来即将成立的国家。他的命运让人不禁联想到他的后代及继承
者奥古斯都。罗马刚刚摆脱一场浩劫,在这种时候出现的这样一个有
关于罗马的故事显然能够引人遐想。虽然其中的寓意并不是很直白,
但人们总是能够意识到其存在。
奥古斯都为罗马带来了一个全新的开端,但他并不打算掩饰自己开创的新罗马的本质,奥古斯都给时代节创造的新传统表明了新时代属于专制的君主。参加庆典者或许会感觉这些宗教仪式都是古老的罗马传统。然而,现在的罗马是由奥古斯都和阿格里帕统治的新罗马,他们二人代表的皇族则是新罗马的核心。
奥古斯都声称他在尝试着把罗马恢复到一种古老的理想状态。在《圣奥古斯都行述》中,他写下了这些看起来自相矛盾的话语:
许多古老的传统现已没落。我便以新法使其复苏。而且,我还在许多领域内创制了值得子孙后代沿袭的新规。[443]
奥古斯都罕见地实行了既创新又复古的改革。就算是在公元前131年,梅提卢斯本人也不过是慷慨激昂地发表了演说而已。身为一名古代的保守派,他所提出的主张并不符合当时大多数人的道德观念。他似乎只是一位和常人意见相左的少数派人士而已。至少在我们看来(罗马人自己或许也深知),罗马人远远没有某种统一的道德观。罗马的意识形态是很复杂多样的。而奥古斯都和梅提卢斯的不同之处就在于,他能够用权力把这种古老的少数派主张化为现实,他试图运用国家的权力来重塑罗马社会及其道德。
奥古斯都时代的文学作品和公共庆典都描绘着一种理想的新社会的图景。奥古斯都政权想要以这种新社会的价值观来教育人民。他们想用各种庆典和《埃涅阿斯纪》来教育人民对诸神和奥古斯都尽忠尽责。人民应当为奥古斯都政权献身;男子应当结婚,应当奔赴战场;女子应当为奥古斯都的军团而生育后代。奥古斯都政权呈现在人民面前的未来是一个繁荣、和平的黄金时代,生活于其中的罗马人都要为奥古斯都的帝国效劳。就算以现代的标准来看,这也是极权主义的景象,历史上有许多好大喜功的独裁者都追求过这种梦想。
大概在二十年以后,诗人奥维德(Ovid)曾经抱怨当时的女性不再珍视他的诗作了:
她们仍然会赞美诗篇,却更想得到贵重的礼物。
只要富有,即便是野蛮人她们也毫不介意。
啊,现在确实是黄金时代:
黄金既能带来官位,也能招致爱情。[444]
就像历史上其他的许多政治人物一样,奥古斯都和阿格里帕基本上是在画饼充饥。当然,并非所有人都会为他们所欺骗。罗马社会是很复杂的,而大多数复杂的社会都以权力和金钱为基础。奥维德就以上文的诗作嘲弄了奥古斯都政权营造出来的假象。他同时还流露出一种怀旧之情,追忆着道德滑坡以前的时代,想象着身为诗人的自己在那种时代里可以凭着精妙的诗歌来赢取异性的芳心。因为在奥古斯都的新时代里,诗作不值一提,金钱才是通往闺房的捷径。就算政客们许诺社会的道德水平会得到提高,就算姑娘们盛赞诗文里的真情实意,最终决定一切的还是金钱。无论政治精英们怎样地哀叹,怎样地追求复古,罗马人都不会重拾某种古道热肠。现在的罗马社会太过复杂,再也无法恢复朴素的模样了。在奥维德描绘的社会图景里,身处于这个黄金时代当中的罗马人都汲汲于钱财。政客、军人、平民、女子,无一例外。这样的图景当然与奥古斯都政权所宣传的不同,但恐怕更加符合实际。
[402] Suetonius, Tiberius , 8-9.
[403] Dio, 54.10.
[404] 此前举办凯旋仪式者为公元前28年的卡尔维西乌斯·萨比努斯(Calvisius Sabinus)、盖乌斯·卡里纳斯(C. Carrinas)、卢奇乌斯·奥特隆尼乌斯·派图斯(L. Autronius Paetus),公元前27年的李奇尼乌斯·克拉苏,公元前26年的塞克斯图斯·阿普莱乌斯(Sextus Appuleius),公元前 21年的塞姆普罗尼乌斯·阿特拉提努斯(Sempronius Atratinus)以及公元前19年的科涅利乌斯·巴尔布斯(Cornelius Balbus)。
[405] 奥古斯都甚至都没有在Res Gestae 里提及此事。
[406] Tacitus, Annales , 1.2-4(节选)。
[407] Res Gestae , 28.
[408] Dio, 53.25-26.
[409] 请参考Nicola K. Mackie, “Augustan Colonies in Mauretania”, Historia: Zeitschrift für alte Geschichte , 32(1983): 332-358,他认为这些殖民地是用来安置在西班牙的战争之后退役的老兵的;Barbara Levick, Roman Colonies in Southern Asia Minor (Oxford: Oxford University Press, 1967); Dio, 54.7, 54.23; Andrew Burnett, Michel Amandry, and Pere Pau Ripollès Roman Provincial Coinage(London: British Museum Press, 1992), Vol.1, From the Death of Caesar to the Death of Vitellius (44 b.c.-a.d.69) (London:British Museum Press, 1992), 1650; Harikleia Papageorgiadou-Ban, The Numismatic Iconography of the Roman Colonies in Greece: Local Spirit and the Expression of Imperial Policy (Athens: Research Centre for Greek and Roman Antiquity, 2004); Suetonius, Augustus , 25。
[410] Res Gestae , 16.
[411] Res Gestae , 15.
[412] Velleius Paterculus, 2.113,这些比例的计算基础是认为当时的罗马成年男性人口有一百三十万。不过,关于罗马人口总数,学界有着不小的争论。这里的一百三十万基于对意大利人口的保守估计,比较大胆的估算会认为罗马人口大概有四百万(意大利人口也会相应地提升两倍)。这两种说法的支持者人数是差不多的。我个人采用保守的数字是因为我在参考了埃及的人口比例以后,认为意大利的奴隶人口应该占了意大利总人口的两成以上,那么如果高值估算是正确的,公元前28年的意大利自由公民(除西西里以外)就有一千三百万到一千四百万,意大利半岛的总人口相应地就达到了一千七百万。考虑到人口的增长,奥古斯都统治末期的意大利人口就要超过两千万了,而19世纪中叶的意大利也只拥有两千万人口。因此,我认为奥古斯都时代的意大利人口没有这么多。
[413] Dio, 54.25.
[414] Dio, 55.25; 28.
[415] Res Gestae , 15.
[416] Peter A. Brunt, “The Lex Valeria Cornelia”, Journal of Roman Studies , 51(1961): 71-83.
[417] Suetonius, Augustus , 53-57.
[418] Dio, 54.14.
[419] Dio, 54.26.
[420] Dio, 55.13.
[421] 其证据之一就是元老们越来越热衷于在铭文中列出自己的官职。请参考Inscriptiones Latinae Selectae , 914; 928; 932。
[422] Propertius, 2.7.1-8.
[423] Suetonius, Augustus , 73.
[424] Ulpian, Rules , 13-14.
[425] Gaius, Institutes , 2.111; Gnomon of the Idios Logos , 24-32; FIRA I, 40.
[426] Suetonius, Augustus , 46.
[427] Dio, 56.1-10.狄奥声称在公元9年有一次大型法律改革,但他有可能是把两次改革合为一次看待了。
[428] Suetonius, Augustus , 34.
[429] Dio, 56.1-10.
[430] Livy, Periochae , 129; Suetonius, Augustus , 89.
[431] Aulus Gellius, Attic Nights , 1.6.1.
[432] Dio, 56.2-9.
[433] Dio, 54.16-17.
[434] 和这项法律有关的文字分散在一些文献当中,不是很容易拼凑起来。请参考Michael H. Crawford, Roman Statutes , II (London: Institute of Classical Studies, 1996), 781-786, n. 60。
[435] Suetonius, Augustus , 69,值得一提的是,苏埃托尼乌斯把奥古斯都的通奸行为视作政治需要而不是欲望驱使下的产物。换言之,奥古斯都和这些罗马政界知名人物的妻子睡觉是为了了解她们的丈夫在想些什么、说些什么。我觉得所有的政客都不妨采用这个说辞。
[436] Suetonius, Augustus , 71. 除了热衷于给处女开苞以外,苏埃托尼乌斯还描写了奥古斯都对骰子的喜爱。他对这两件事情的着墨力度是相同的,我们可以由此看出罗马人的道德观念和现代人之间有着多么巨大的差异。
[437] Dio, 54.19.
[438] Tacitus, Annales , 3.25.
[439] Tacitus, Annales , 3.28.
[440] Zosimus, 2.6.其文本显然出自奥古斯都时代对当年的神谕的描述。
[441] Corpus Inscriptionum Latinarum , 6.32323.
[442] Catullus, 64; Virgil, Eclogue , 4.
[443] Res Gestae , 8.
[444] Ovid, Ars Amatoria , 2.275-279.
第十七章 帝国时代
到了公元前18年,奥古斯都政权已经表明了自己是专属于一个家族的政权。族中地位较高的男性越来越频繁地以政权高层的身份出现在公众面前。如果还有共和派人士心存幻想,认为奥古斯都只是自公元前509年以来的共和国历史上偶然出现、转瞬即逝的意外,那么奥古斯都身边逐渐形成的宫廷应该能够迫使他们丢掉幻想,清楚地认识到残酷的现实。现在,国家大权集中于奥古斯都及其身边亲信的手中。而且,这个宫廷属于奥古斯都的家族。罗马显然面临着君主制的未来。以奥古斯都为首的政权高层是不可能轻易放弃这种权力的,而在奥古斯都的关系网络以外的那些人则很难聚集起足够的政治、经济、军事资源来挑战奥古斯都等人。
奥古斯都政权自称为帝国政权。他们给罗马带来了秩序,并且以
严格的纪律来帮助罗马实现其扩张的使命。在公元前30年,屋大维控
制着全国的所有军队。在公元前28年到公元前27年的协定当中,屋大
维和阿格里帕暂时交出了军权,以便把自己的特殊地位化作国家的常
态。但政治权威的正常化并不意味着放弃权威。在公元前27年,奥古
斯都受命掌握了巨量的罗马领土,其中包括构成今天的西班牙的三个
省份当中的两个,四个高卢省份,叙利亚、腓尼基、奇里乞亚、塞浦
路斯,还有埃及。元老院掌控的阿非利加、达尔马提亚和马其顿还驻
扎着大量的罗马军队,但其他的元老院省份都没有多少军力,也就是
西班牙的一个省份、努米底亚、克里特(Crete)、昔兰尼加[利比亚
(Libya)]、亚细亚、比提尼亚(Bithynia)、本都(小亚细亚的四个省份
之中的三个)、希腊和萨丁尼亚。[445]后来,这份协定有了改动。奥古
斯都放弃了塞浦路斯以及最靠南也最和平的一个高卢省份(纳尔博高
卢),但他拿到了达尔马提亚。因为罗马正在往多瑙河方向大举扩张,
而这里就处于战线的中心。
很可能有不少罗马精英会怀疑他们是否真的需要有这样一位凌驾于所有人之上的将军。或许,这种质疑的声音很少公然出现,却显然潜伏于当时的政界。毕竟,在元老院的领导下,罗马已经从一个微小的城邦发展为一个超级大国的首都。既然共和国时代的罗马取得了如此辉煌的成就,那么有人怀疑君主制度会妨碍罗马的发展也就不足为奇了。
为此,奥古斯都向人们许下了征服世界的承诺。后来,至少他宣称自己已经实现了这个目标。《圣奥古斯都行述》是他临终时对自己一生的总结与辩解,这份文本的序言充分说明了奥古斯都政权的本质是和武力扩张分不开的:
以下为神圣的奥古斯都的一生功业的记录。他由此为罗马人民征服了世界。[446]
罗马的国家资源是奥古斯都政权的财力之源,而武力扩张就是其意识形态上的核心。
从奥古斯都的共和国成立的那一年开始,奥古斯都和阿格里帕就
长期投身于战争之中。公元前27年,奥古斯都离开了罗马,前往高
卢,打算入侵不列颠。不过,西班牙的事务让他放弃了原来的计划。
公元前26年,罗马人在多条战线上展开了大规模的战事:阿尔卑斯山
区(指挥者为提兰提乌斯·瓦罗);西班牙,对抗阿斯图尔人(Astures)
和坎塔布里人(指挥者为奥古斯都);日耳曼尼亚(指挥者为马尔库斯·
维尼奇乌斯);阿拉伯沃土(Arabia Felix,指挥者为埃里乌斯·伽卢
斯,此战或许并非发生于公元前26年);也许还有达尔马提亚和潘诺尼
亚(指挥者为马尔库斯·普里穆斯)。虽然罗马方面宣布这些战争都以
胜利告终,但其中不少地区的冲突一直延续到了公元前22年或公元前
21年才真正结束,个别地方甚至持续得更久。[447]
身处后方的罗马人则反复地看到奥古斯都政权在宣扬历次胜利,这种行为或许可以打消某些人的疑虑。但其实,奥古斯都时代的各位罗马将领所干的事情和共和国时代并没有什么区别。他们不会去细究被击败的异族是否真的已经彻底臣服,只会尽早送回捷报,以求获得各种奖赏。军功既可以带来荣耀,也可以为政治权威提供依据。奥古斯都政权强调了罗马的历史使命就是征服扩张。维吉尔还让他笔下的朱庇特预言罗马人会得到(时间和空间上都)“无止境的帝国”。[448]奥古斯都在公元前19年再度宣示了自己的政治权威,而他的依据就来源于这几年内史无前例的军事胜利。
除了宏大的纪念建筑和史诗以外,奥古斯都政权还有别的宣传载体。奥古斯都统治末期,有一幅精美的石雕作品诞生了,我们称之为奥古斯都之石(gemma augustea)。在这幅作品当中,取得了胜利的圣奥古斯都在诸神的簇拥下,向后倚靠着,欢迎一位得胜归来的将军。下面的另一个场景则刻画了罗马的扩张所造成的代价:罗马士兵粗暴地拉扯着女子(显然在暗示强奸);俘虏即将被充作奴隶或者遭到处决;蛮族人流下了泪水。由此可见,罗马人固然会庆祝自己的胜利,把战争粉饰为光荣之举,却不会掩盖其阴暗的一面。
公元前16年,奥古斯都的立法工程已经展开,时代节也已结束。阿格里帕和奥古斯都再次投身于开疆拓土,他们的主攻方向是西部和多瑙河流域。提比略和他的弟弟德鲁苏斯被派去了阿尔卑斯山区,以便积累军事经验和功绩。他们的对手是许多个互不统属的小部落,罗马人称这个地区为雷蒂亚(Rhaetia,主要位于今天的奥地利境内)。阿尔卑斯山区部落民遭到讨伐的原因是抢劫以及杀害了俘虏的罗马男
性,虽然其中有些所谓的罗马男性还在母亲的肚子里,我们不知道他
们用了什么神奇的方法来预测其性别。德鲁苏斯和提比略不仅征服了
这些部落,还开始彻底摧毁当地的政治、社会结构。无数的部落民被
迁走,或是沦为奴隶。许多地方的人口数都有明显的减少。[449]战争
一直持续到了公元前14年以后。不过,我们不太清楚后期的战况如
何。公元前6年,奥古斯都在阿尔卑斯山脉滨海区的拉蒂尔比[La
Turbie,位于今天的法国东南部城市尼斯(Nice)以东]为他们竖立了一
座三十五米高的胜利纪念塔,这是比较罕见的纪念建筑,塔身的铭文
列出了四十五个被征服的部落名。[450]
从公元前17年开始,罗马对日耳曼尼亚的大规模入侵也揭开了序
幕。而且,奥古斯都亲自上场指挥到了公元前13年。[451]据说,这场
战争的起因也是当地居民的野蛮暴行:三个日耳曼部落组成了联盟,
捉拿进入他们的疆界内的罗马人,将其钉死,并且闯入了高卢大肆劫
掠。[452]在奥古斯都离开以后负责日耳曼尼亚战事的是德鲁苏斯,他
大概刚刚从阿尔卑斯山区赶来。[453]公元前12年,德鲁苏斯率军跨越
了莱茵河。我们很难复原他的具体行军路径,因为我们对当时日耳曼
尼亚境内的地名知之甚少(如地图7)。但据说,德鲁苏斯来到了北海
边。他有可能取道于今天的荷兰,然后在不来梅(Bremen)以南建立了
一连串的据点,其位置距离莱茵河畔的罗马要塞大概有三百公里。
[454]
地图7:罗马的北部疆域
公元前17年,多瑙河上游地区的部落朝着地中海南下,东边的马其顿同样遭到了外敌入侵,色雷斯的罗马附庸国王也面临着异族的进犯。我们不确定为什么这些部落会同时行动,也不清楚他们相互之间是否有联系。不过,多瑙河是一条重要的贸易通道,上游和下游居民之间是有理由保持外交联系的。而在他们看来,罗马无疑是史无前例的强敌。到了这个时候,罗马人已经在这块区域施压、扩张了不下于十年了。屡战屡败的当地居民或许想要联合起来抵抗罗马,但他们没有成功。罗马人反而把战线推进到了多瑙河,宣布完全控制了巴尔干和马其顿。[455]然而,军事基地和行省的建立并没有给这块土地带来和平,[456]罗马人的统治并不稳定。
公元前14年末,罗马人再一次宣布了胜利,但仅在第二年,阿格里帕就受命前来管理此地。据说,这是因为潘诺尼亚人又在谋反。我们大概可以认为此时的潘诺尼亚整体上还不稳定,当地人随时都有可能举起反旗。至少,罗马方面的判断就是需要进一步加以管制。阿格里帕抓紧时间在冬天发起了进攻。罗马人有着精良的部队、坚固的工事,还有完善的后勤,具备很大的优势。阿格里帕的军事行动巩固了罗马人对多瑙河南岸的掌控。随后,完成使命的阿格里帕踏上了返回罗马的旅程。
然而,这一次,他未能回到帝国的首都。公元前13年,阿格里帕在坎帕尼亚去世了。[457]自公元前44年以来,阿格里帕一直都是奥古斯都的亲密战友,他们一同经历了对抗卢奇乌斯·安东尼乌斯、塞克斯图斯·庞培以及安东尼的战争。阿格里帕或是统率一支偏师出战,或是陪同在奥古斯都身边。在公元前28年和公元前27年,奥古斯都共和国关键的酝酿期,阿格里帕也在以执政官的身份支持着奥古斯都的
计划。他还曾为奥古斯都平定高卢和西班牙,去东方准备出征帕提
亚。在公元前1世纪20年代中期,当奥古斯都本人身处西班牙之时,阿
格里帕一度是他的代表。在公元前23年以后的那些艰难岁月里也是如
此。罗马城内有许多极其雄伟、壮观的建筑都是在阿格里帕的主持下
完工的。在马尔凯卢斯死后,阿格里帕更是迎娶了尤莉亚(奥古斯都的
女儿),直接成了皇室的核心人物之一。这段婚姻也让奥古斯都有了几
个外孙和外孙女。阿格里帕还曾与奥古斯都一起举办时代节,庆祝新
的黄金时代的到来。在公元前18年,他被授予了保民官的权力。其时
限同样在公元前13年得到了延长。至迟在公元前13年,他还得到了和
奥古斯都一样统治地方省份的大权。严格说来,阿格里帕的权力和奥
古斯都是相等的,在他去世之时,他和奥古斯都是分享权力的政治伙
伴。
奥古斯都亲赴坎帕尼亚看望亡友。然后,他领着丧葬队伍回到了
罗马城,把阿格里帕的遗体暂时摆放在城中心的广场上。接着,他为
阿格里帕发表了吊唁词。1970年,人们在科隆大学的图书馆里发现,
有一份埃及莎草纸文献上记录着这篇吊唁词的一部分内容。这份史料
以希腊语写就,是拉丁语原稿的直译本。看起来,奥古斯都很有可能
把这份吊唁词正式地分发给了各地的省份。[458]从这份残缺的文本来
看,奥古斯都强调了宪法赋予阿格里帕的权力:没人拥有比阿格里帕
更高的权位,就连奥古斯都自己也不例外。不过,虽然他在致辞时强
调了宪法,延续了一贯的作风,但同时,他也凸显了其政权的统治地
位。之后,阿格里帕被火葬,其骨灰被送入了战神广场上的奥古斯都
陵墓里。
据说,阿格里帕在遗嘱里把他的田产赠给了奥古斯都(这不仅包括
意大利的田产,还涉及阿格里帕设法在地方省份获得的资产),人民则
得到了免费的公园和浴场。阿格里帕还要求给每一位平民分发四百赛
的资金。此外,城内举办了吊丧的运动赛事。按照罗马传统,角斗是
其中的主要内容。在五年后的公元前7年,这些比赛又举办了一次。
[459]这种高规格悼念阿格里帕的举措与活动不仅说明了他的重要地
位,还体现了奥古斯都政权成功地垄断着国家的权力。很少有人能够
与阿格里帕的履历相媲美,他的官职、军事生涯、主持过的建筑工程
让许多人难以望其项背。但他的生涯不同于共和国时期的罗马人。在
帝国时代,所有人都无法与皇帝相比,阿格里帕始终次于奥古斯都。
奥古斯都失去了他的首席大将和政治伙伴。如果在二十年前发生这样的事情,奥古斯都政权或许就要遭遇一场严峻的挑战。但是,在公元前12年,提比略(如图10)和德鲁苏斯都已经成长起来,他们都可以接替奥古斯都的老友阿格里帕的位置。虽然看似有些过于焦急,但提比略和维普萨尼娅(阿格里帕的女儿)的婚姻关系被终止了,尤莉亚(阿格里帕的遗孀,奥古斯都的女儿)被许配给了他。这场婚姻标志着提比略成了皇族之中仅次于奥古斯都的第二人。此外,帝国扩张的步伐也没有因阿格里帕之死而暂停。[460]
在日耳曼尼亚,马尔库斯·洛里乌斯受到了攻击,损失了一个军
团。[461]不过,德鲁苏斯继续战斗至公元前10年。在这一年,奥古斯
都和提比略一度在高卢与他会师。[462]德鲁苏斯是公元前9年的执政
官。大概是他先返回罗马出席了就职仪式,然后很快就回到日耳曼尼
亚去指挥新一年的战斗。这一回,他很可能是顺着之前建立的一连串
据点,渡过了威悉河(Weser),向东前进了大约一百公里,抵达易北河
畔。德鲁苏斯由此成了第一位如此深入日耳曼尼亚(如地图7)的罗马将
领。有传说称,他在横渡易北河时遇到了一位身形极高的女子。此人
预言他即将死去,命令他就此返回。于是,德鲁苏斯把他的战利品竖
立起来,用以庆祝自己的胜利,然后就谨遵神谕,开始返回。然而,
在路上,德鲁苏斯如同预言所说的那样患上了疾病。原本大概正在潘
诺尼亚作战的提比略闻讯之后连忙赶来看望他的弟弟。在提比略抵达
之时,德鲁苏斯还活着,但他终究未能再一次回到莱茵河的左岸。
[463]
日耳曼人也许会觉得德鲁苏斯之死能够让罗马人就此收手,把资源转移到其他方向上去。然而,提比略从多瑙河流域来到了日耳曼尼亚,奥古斯都本人也重返高卢督战。显然,罗马方面要把这场战争进行到底。日耳曼人派出使者前来求和,但奥古斯都和提比略把他们当作一个统一的国家来处理了,要求所有的部落都同意遵守和平协议。最终,日耳曼人未能达成一致意见(我们其实也很难想象这么多不同的部落要如何达成一致),奥古斯都和提比略便把日耳曼使者囚禁了起来。日耳曼人现在已经无力抵抗了。[464]但提比略第二年还是身处战场,虽然他在冬天一度回到了罗马就任执政官。[465]
多瑙河流域的居民遭遇了类似的命运,阿格里帕之死并没有导致
罗马人暂缓攻势。潘诺尼亚人确实发动了叛乱,但提比略来了。他刚
刚接受了与阿格里帕的遗孀成婚,或许现在更加乐意地接手了阿格里
帕的军事职责,在潘诺尼亚展开了作战。潘诺尼亚人再度被击败。接
着,提比略再次运用了他和德鲁苏斯几年前在雷蒂亚采用的手段,把
潘诺尼亚人迁走,或是充作奴隶。[466]然而,就连这种手段也未能让
潘诺尼亚得到和平。公元前11年,提比略先是南下至达尔马提亚镇压
一场叛乱,然后返回潘诺尼亚投身于另一场战斗。[467]虽然提比略在
公元前10年来到了高卢,但多瑙河流域的战火仍然没有熄灭。达契亚
人会在未来的一百二十年间给罗马人造成不小的麻烦。而在此时,他
们跨河来犯,让潘诺尼亚又陷入了动乱。提比略只得再度返回维护罗
马的权威,这一次的战斗持续到了公元前9年。然后,罗马人又一次宣
布他们取得了胜利,恢复了和平。[468]
德鲁苏斯之死对奥古斯都的王朝造成了不小的打击,他同样得到了国丧的待遇,国家给他的生母莉薇娅颁发了荣誉以表慰藉。[469]距离阿格里帕之死还不足五年,罗马人民再度陷入了悲痛之中。不过,这一次,他们并不是在哀叹一位出色的国家领导人的离去,而是在痛惜一位英年早逝的皇子。由此,我们可以看到他们对皇室的忠心。他们和奥古斯都的家人之间仿佛是挚友一般亲密,德鲁苏斯的丧礼自然又一次展现了罗马人民的团结一致和皇室的莫大权威。
阿格里帕和德鲁苏斯的相继逝世让皇室的处境变得有些危险,奥
古斯都政权至少需要有一位潜在的继承人,此人必须有充足的经验和
政治地位才能成功地从奥古斯都手中接过政权。简而言之,在这个时
候恐怕骤然就有了不少人想要密谋作乱,因为在公元前12年之前,夺
权成功的条件当然是除掉(夺走权力或者杀死)奥古斯都、阿格里帕、
提比略和德鲁苏斯四个人,而在公元前9年以后,需要铲除的人一下子
就少了一半。不过,帝国的新一代潜在的领导者正在涌现出来。
阿格里帕与尤莉亚之子盖乌斯·恺撒出生于公元前20年,他的弟
弟卢奇乌斯小他三岁。这两个小男孩都越来越多地出现在公众的视野
里。而且,他们都在公元前17年被奥古斯都收为养子。虽然这或许意
味着他们有资格直接成为奥古斯都的继承人,但他们毕竟太年幼了,
罗马人希望由久经考验的领袖来担任皇帝。幼年皇帝要到几百年以后
才开始为罗马人所接受。安东尼娅(Antonia)和德鲁苏斯的长子日耳曼
尼库斯出生于公元前15年5月24日。多年以后,日耳曼尼库斯和他的父
亲一样在御前效劳,但现在还为时尚早。卢奇乌斯、盖乌斯、日耳曼
尼库斯以及提比略的儿子德鲁苏斯(生于公元前13年10月7日)都有潜力
成为罗马的领导者,但他们也都还需要时间。此时,奥古斯都只能把
皇权传承到提比略手中。
不满之人
公元前19年以后,奥古斯都政权的反对者看起来被排挤到了政治舞台的边缘。不过奇怪的是,据说奥古斯都经常穿着胸铠进入元老院,以防有人行刺。而且,大约在公元前18年的时候(后来也有),有“很多人”被指控对奥古斯都和阿格里帕图谋不轨,某些人还遭到了处决。[470]从公元前16年到公元前8年,奥古斯都的绝大部分时间都花在了各地的军务上,但他同时也面临着内部阴谋的威胁。虽然我们既
不知道有哪些人牵涉其中,也不知道阴谋的具体内容,无从判断奥古
斯都究竟面临着多么严重的威胁,但至少我们知道奥古斯都因此修改
了法律,加强了他对罗马政治精英的束缚。为了获取犯罪证据,罗马
人通常会对奴隶严刑逼供,他们似乎认为只有经受了酷刑的奴隶说出
的口供才是有效的。但是,用这种手段获取的有关该名奴隶的主人的
犯罪证据是不合法的。这条法律确保了各位奴隶主在家里所说所做的
都不会在日后成为危及己身的罪证。然而,在帝国时代,一切利益都
要服从于国家。这条法律被规避了,奥古斯都会下令把受怀疑者的奴
隶转交给国家。然后,这些奴隶被刑讯逼供出来的证词就可以被用于
证明其原主人的罪行了。由此,奥古斯都一举让密谋者身边的奴隶都
成了潜在的罪证来源。[471]
这种情况显然会导致一个问题—真正的阴谋和某些不妥当的危险
言论之间的界限并不是很明确,皇帝需要辨别单纯的不满者与真正的
谋逆之人。大动干戈地铲除密谋者是需要付出政治代价的,所有人都
会因此知道有反对的声音存在,团结一致、通力合作的表象会被撕得
粉碎。一些尚未找到同伙的不满之人会发现自己并不孤单,其他人也
许会深受鼓舞,前赴后继地走上反对现政权的道路。而且,以暴力消
灭政敌所产生的恶劣影响还会延续到未来,让后继的皇帝都背负上沉
重的历史包袱。这种行径不仅不能根除政敌,反而会证明自己就是暴
君,让密谋者看起来像是正义的一方。
我们比较了解的只有一起阴谋。公元4年,据说格奈乌斯·科涅利乌斯正在图谋不轨。此次事件的曝光正是因为奥古斯都违背了他的一贯政策。他没有杀掉科涅利乌斯及其党羽。这不是因为一路走来杀人无数的奥古斯都突然感觉到良心不安,而是因为他想要摆脱无休无止的暴力。1世纪的政治家、哲学家塞内加(Seneca)和3世纪的史家卡西乌斯·狄奥为我们保留了某一段子虚乌有的对话的两个不同的版本。据说,在莉薇娅的建议下,奥古斯都把密谋者召到了面前,对他们加以警告,然后就放他们走了。[472]科涅利乌斯甚至还担任了第二年,也就是公元5年的执政官。无论这个故事到底有几分可信,我们都可以看出奥古斯都政权深受反对派的困扰,而且难以摆脱这个泥沼。
有关婚配和性行为的法律依然是人们争论的焦点。最终,在公元9年,骑士阶层发起了一场大规模的集会示威。奥古斯都到场对示威者发表了讲话,称赞了其中已经生育后代者,为他们提供了额外的嘉奖或荣誉,也许还有奖金。对于那些尚无子女者,奥古斯都的态度就大不相同了。他指责这些人是只顾自己享乐、不顾罗马利益的登徒子,还把他们比作杀人犯和神庙的窃贼,因为他们让自己本可以来到人间的后代失去了降生的机会,也就无从接替其父辈去供奉诸神。[473]不过,这一年的两位执政官还是出台了一项法律,修改现行法律中的条款,把重点从惩罚未婚者改为褒奖已婚者—这就是《帕皮乌斯和泊派乌斯法》(Lex Papia Poppaea)。巧合的是,这两位执政官都未婚。
我们可以在文学领域看到对奥古斯都政权的抗议。奥古斯都时代的最后一位著名的诗人奥维德在晚年遭到了流放,其罪名有二:第一个罪名和他的一首诗有关,第二个罪名是某个不为我们所知的“错误”。这是奥维德在一首长诗中告诉我们的,也就是《哀怨集》(Tristia)的第二首诗。[474]在这首悔过求饶的诗中,奥维德捉弄了读者。他不肯说出自己究竟犯了什么错误,因为他不想揭开过去的伤疤。当时的一些读者大概有所耳闻,他们能够明白奥维德在说什么,而像我们这样毫不知情的读者就只能发挥自己的想象力了。到底是什么样的错误会让奥维德这样的知名诗人面临死刑的威胁,然后遭到流放呢?
不过,第一个罪名里的那首诗是明确的:《爱情的艺术》,即奥维德的爱情指南。在这首诗中,奥维德扮演着“爱情导师”的角色,指导阅读此诗的男男女女去寻找爱人。奥维德当然不是在做媒。婚姻是家族大事,结婚与否取决于双方的财富、社会地位、前途以及结亲的联盟效益。奥维德这首诗的主题是寻找私密的性伴侣。他警告读者们不要犯下通奸之罪(“我们歌颂的是安全的性爱;我的诗篇里不会有罪行”[475]),但这个警告看起来只是套话。这首诗的所有内容都暗含通奸的本质(“没有哪个女人真的绝不沦陷”[476])。男方必须到女方的家里,所以,他必须先和对方的丈夫交好;女方则要设法转移丈夫的注意力。[477]《爱情的艺术》就是一本通奸教程,而且正好诞生于通奸属于刑事犯罪的时代。
不过,在《哀怨集》的第二首诗中,虽然奥维德整体上先是低落地承认了自己的错误,然后请求得到原谅,并且为皇室献上了祈祷,但他似乎也有些失态,一度显得有些愤怒。他引用了《爱情的艺术》里的文字,指出自己明确警告了读者们要对已婚女性敬而远之(故意忘记了他也说过所有女性都能手到擒来)。他怀疑奥古斯都是否真正读过他的诗,他还援引了罗马传说里和性、暴力有关的大量内容,他也一一列举了罗马城内男女有可能相遇的地方—剧院、竞技场、奥古斯都和阿格里帕用以装饰罗马的奢华柱廊,以及朱庇特、朱诺、马尔斯、伊西丝的神庙。他指出,这些地方明明都还在正常地运转,整个罗马城到处都是有可能引发犯罪的地点。罗马文化与性爱密不可分,奥维德开始着手揭下这座性爱之城的面纱。他引述了神话传说里有关性爱与强奸的故事。他列举了一个长长的名单,名列其中的都是写过有关爱情与通奸之事,却仍然广受尊重的诗人。奥维德有理有据地质问奥古斯都为什么要来管这么一篇消遣之作,惩罚一个无足轻重的诗人,他明明还需要去征服潘诺尼亚人、色雷斯人和帕提亚人,有诸多要务缠身的奥古斯都竟然会在意一首爱情诗?
奥维德的致歉词演变成了控诉。他攻击了奥古斯都政权的意识形态,揭露了奥古斯都的暴君本质。在他的笔下,奥古斯都残忍而为所欲为,就好像是随心所欲的诸神一样。奥维德还指出了罗马从古至今都很堕落。而在奥古斯都时代,就连他这样的小人物都会因为描写了不合现政权心意的两性之事而成为国家的敌人。当奥维德审视奥古斯都及其政治权力、财富和军队之时,他看见的是一个超乎常理之外的政治人物,他甚至觉得奥古斯都仿佛就是人间的神明。对于奥古斯都政权而言,奥维德的《爱情的艺术》固然不合其意识形态,但也只能算是蚍蜉撼大树而已。然而,这棵大树回击了,奥维德遭到了流放。
权力和意识形态的关系是非常亲密的,权力总是需要用意识形态来说明其正当性。质疑某个政权的意识形态就是在质疑这个政权对社会的意义,对其发起反对就会遭到排挤。在极权政权统治下,许多人或许会遵循官方提出的伟大理念,还有一部分人也许会认为官方的意识形态都是胡说八道。但是,这些人应该也能明白,跟着政权走是有好处的。奥古斯都政权把人民纳入了其政治结构当中,让他们加入帝国的计划,邀请人民与自己同呼吸,为其成功而喝彩,为其损失而悲哀。庆祝战争的胜利和哀悼皇族成员的离世都是例子。奥古斯都政权会向人们提供许多的利益,以便让他们默默地顺从于现在的政治秩序。例如,某个元老或许还在怀念共和制度,但他同时还能看到,在帝国时代,自己和家人都变得更加富有了,还能享受到安全的和平时光,取得地方或中央的权位,或许皇帝本人也会对自己以礼相待。如此一来,他就有可能不会直言自己厌恶现政权了。在这种情况下,人们对现政权的敌意会以两种不同的方式表达出来:或是激化为阴谋,或是弱化为讽刺,而官方对于这两种行为的容忍度都十分有限。我们或许可以和奥维德一起佯作不知,质问像奥古斯都这样备受尊敬、拥护者无数的领导人为什么要来严惩一位调皮的诗人。但所有的罗马人都知道其原因:帝国政权不允许反对者的存在。
宫廷危机:提比略失势
虽然反对派的身影不断出现,给奥古斯都政权造成了一定的麻烦,阿格里帕和德鲁苏斯之死也是不小的噩耗,但是,奥古斯都政权依旧掌控着权力。公元前8年,奥古斯都延续了公元前18年的宪政安排,得到了为期十年的保民官权力。提比略在公元前7年第二次担任执政官。为了表示庆祝,奥古斯都向士兵们和殖民地里的各位老兵送出了礼金,巩固了他和军队的关系。提比略获准举办了一次凯旋仪式,他得以游行于罗马的街道上,宣示自己是奥古斯都的政治伙伴、一位伟大的罗马将军以及未来的皇帝。[478]但奥古斯都本人也得到了新的荣誉。每到奥古斯都的生日,大竞技场(Circus Maximus)内便会举办比赛。罗马历的6月(Sextilis)[1]被重新命名为奥古斯都月,就好像5月(Quintilis)[2]被改名为尤里乌斯月一样。这些通常都是属于诸神而非凡人的特殊待遇。
随着公元前6年的两位新执政官就职,卸任的提比略获得了保民官权力。现在,他拥有了等同于当年的阿格里帕的地位,成为稍低于奥古斯都的政治伙伴。提比略正准备离开罗马,前往亚美尼亚,因为在国王死后,亚美尼亚就陷入了混乱。这块土地也是提比略当年初次执行军事任务的地方。此外,向东方发起一场伟大的远征有助于进一步提高提比略的政治地位,并且再一次体现罗马需要皇室来维持其大国霸权。
但提比略因故未能成行。皇室内部想必发生了争执,而提比略落了下风。然后,他并不打算静候时机卷土重来,反而恳求获准退隐。这场争论很快就变得众所周知。不过,罗马的政治精英们本就消息灵通,政界的大小事务很容易扩散开来。为了自己的儿子,莉薇娅试图出面帮助他和奥古斯都达成某种协议。而奥古斯都则公然批评提比略这种背弃职责的行为,拒绝了提比略的退隐请求。接着,提比略绝食四天。奥古斯都只好屈服。
提比略从罗马来到了罗德岛。之前,他曾经在前往东方的途中落脚于此,对这座岛屿颇有好感。他没有像通常的罗马大贵族那样享受着豪华庄园里的生活,而是住在一个小房子里。他还经常去镇子上漫步,与镇民攀谈。看起来,他真的退隐了。[479]
提比略的引退之举必定给罗马政坛造成了很大的冲击。这种事情几乎毫无先例,以往只有非常年老或者已经孤立无援、走投无路的政治人物才会退出政坛。提比略的情况当然完全不同于这两类人。对于像他这种地位的罗马人而言,参与政治生活可以说已经不是人生选择的问题了,而是与其本人身份密不可分的一部分。退出政界相当于否认罗马的根本性社会价值观念,否定了罗马的等级秩序。而且,这种行为可以被解读成,或者说,其可行的理由是国家已经腐败之极,秉持正义者只能远离肮脏的政坛。后世有人猜测提比略此举是因为他的妻子尤莉亚与人通奸,令其震惊不已。然而,在公元前6年,尤莉亚依旧安然处于皇室的高层。如果仅仅是因为他们二人的夫妻关系遭到了猜疑,提比略看起来不太可能会选择退隐。
公元前6年正好也是盖乌斯和卢奇乌斯登上政治舞台的年份,提比略引退一事恐怕与此相关。当时,年仅十四岁的盖乌斯受任为祭司。对于罗马元老而言,这是一项比较重大的荣誉。而且,在公元前5年执政官的选举活动中(应当开始于公元前6年夏),罗马人民选举盖乌斯为执政官,虽然我们不知道此事发生于提比略离开之前还是之后。无论如何,他的高人气都很可能助长了提比略的不满之情。
选举如此年幼之人担任执政官当然是前所未有的事情。此时的盖乌斯甚至比屋大维当年刚刚继承恺撒的遗产、步入罗马政坛之时还要年轻。对此,奥古斯都遵循了共和国的传统,加以拒绝,还批评人民在选举中支持年轻的盖乌斯。[480]此外,奥古斯都在人民面前强调了他本人依然健在,罗马无须让这样年轻的后辈来担负责任。他也一度公开批评了盖乌斯和卢奇乌斯的生活作风有问题。看起来,他们二人都不太符合罗马道德标准。不过,虽然这些事情或许让奥古斯都感到有些尴尬,但我们同样可以从中看出平民的意愿和罗马政治的前进方向。人们不在乎盖乌斯的年纪,此时罗马宪法的共和制表象并没有明显影响选民的行为,他们只在乎盖乌斯是奥古斯都的外孙。此次选举充分说明了平民的意识形态已经基本倒向了君主制。
对于提比略而言,盖乌斯有很高的人气并不是一个好消息。如果以共和国的传统而论,他们二人之间现在不可能存在竞争关系。提比略已经两度出任执政官,有着多年的带兵经验,他自成年以来就一直处在奥古斯都政权的核心圈子当中。而盖乌斯还只是一个毫无建树的小男孩。然而,民众的意愿再明显不过。奥古斯都这一次或许成功地约束了民众的行为,当然,他有可能也是为了顾及其他元老的意见。但不管怎样,这一次的选举已经证明了盖乌斯和他的兄弟卢奇乌斯迟早会成为众望所归的奥古斯都继承者。
一旦盖乌斯和卢奇乌斯成了新一代的奥古斯都,那么提比略就只
能成为他们的助手兼顾问了,也就是又一个阿格里帕。显然,身为资
历较深、地位较高的政治人物,提比略大概不想拥有这样的命运。位
居这两个如此年轻的孩子之下或许可以算是对提比略的尊严的冒犯。
就算提比略是在盖乌斯得到人们的选票之前离开罗马的,身为一名经
验丰富的政治家,他也不太可能不知道罗马的政治形态将走向何方,
他应该知道这场争端只会有一个结果。随着这两个小男孩渐渐长大,
提比略的地位只会越来越脆弱,他很可能会不得不坐视他妻子的两个
孩子取代自己的位置。
公元前6年的这个问题既和特定的个人有关,也和奥古斯都政权的
意识形态有着密切的联系。罗马已经有长达五百年的共和制历史了。
当然,罗马人深知君主制的运作方式。他们知道希腊世界里那些古老
的君主国是怎样运行的。但奥古斯都的共和国没有直接采用君主制的
外衣,奥古斯都用共和国官职的表象掩盖了其权力的本质。即使是在
奥古斯都去世以后,罗马的皇位也是经过了法律批准的,保留了共和
国的假象。在奥古斯都的共和国里,皇权看起来应该被传给资历较深
之人,而提比略显然很合适。然而,事实上,提比略却面对着一个小
男孩的威胁,其掌权的唯一理由就是他的外祖父是奥古斯都。所以,
此时困扰着奥古斯都政权的问题是两种截然不同的解释统治正当性的
体系都在运行。
尽管许多元老或许支持提比略,但他们原本就是因为这个体系问
题而被夺走了统治权。共和国(至少从理论上说来)以个人成就来论定
人们的地位,而君主国(也是从理论上说来)论血统。如果奥古斯都共
和国在这个问题上表现得像是一个真正的共和国,那么提比略就会被
认作成就更大、地位更高者,他的预期就能得到满足。但那些把选票
投给了盖乌斯的民众显然已经觉得自己生活在一个君主国里,他们更
希望让国家大权随着皇室血脉而传递。考虑到奥古斯都共和国的本质
确实就是自相矛盾的,无论君主派还是共和派看起来都不能说自己的
主张一定正确。但无视提比略的个人预期同样是有一定的道理的。提
比略的既有地位并非源于他自己的才华,奥古斯都早就成了他的继
父,提比略能够拥有现在的国家第二人的地位恰恰就是因为奥古斯都
政权有着君主制的本质。他的问题是这一套把他擢升至高位的政治文
化现在又想要让他位居人后。不过,无论是否有道理,提比略已经在
公元前6年离开了。
此时,奥古斯都的年纪是五十七岁。他还不算太老,但恐怕已经
不能长期担任罗马政坛的一线角色了。然而,他并不打算像继子提比
略一样引退。公元前5年,他亲自出任执政官,再一次宣示了自己的权
威,表明他仍然是罗马的领导者。他利用执政官的权力提携了盖乌斯
和卢奇乌斯。盖乌斯被引荐给了元老院。这位明显缺乏经验的年轻人
将跟在奥古斯都的身边,获得历练。第二年,卢奇乌斯也获得了早早
地进入元老院的特权。盖乌斯还被选为了执政官,不过,是在五年后
出任,那个时候他就有二十岁了。卢奇乌斯同样提前获得了未来的执
政官职位。虽然允许皇族成员提早参选已经成了一种常见的拔擢手
段,但让盖乌斯真的当选仍然称得上是一种罕见的创新。这可以反映
出罗马的政治局势在提比略引退之后变得不太稳定。奥古斯都有必要
通过这种手段向人们证明,未来的罗马也还是会由尤里乌斯王朝来统
治。盖乌斯和卢奇乌斯由此被指定为罗马政坛未来的领导者,他们的
当选可以表明罗马人民依旧大力支持着奥古斯都政权和皇室的子孙。
这是对某些心存侥幸之徒的警告。
在接下来的这几年里,奥古斯都充分运用了各种仪式性手段来强调他的王朝统治了罗马政治生活的方方面面。例如,就在公元前5年(也可能是在公元前4年),骑士阶层正在召开某种私下的聚会。据说,他们自发地称赞了盖乌斯,显示出他们的拥护之意。卢奇乌斯或许也得到了他们的赞美。此时,他们二人都拥有所谓“第一青年”(princeps iuventutis)的名号。这个头衔和奥古斯都在公元前28年得到的“第一元老”(princeps senatus)相呼应。[481]
奥古斯都还试图再次确保平民对自己的支持。在过去的十几年
里,他给平民花钱的场合很少。在公元前13年,他按照阿格里帕的遗
愿送出了礼金。公元前12年,他为了庆祝自己当选为最高祭司而给不
下于二十五万的罗马平民发放了每人四百赛的奖金。而在公元前5年,
为了庆祝他的两个外孙登上政治舞台,奥古斯都决定给罗马城内的三
十二万人提供每人两百四十赛的礼物。[482]然而,奥古斯都政权的地
位依旧很脆弱,盖乌斯和卢奇乌斯仍显稚嫩,奥古斯都则至少需要活
到他们成年。现在,他们二人都只是十几岁的少年,毫无政治经验和
政治地位。假如奥古斯都在公元前2年之前忽然去世,那么提比略也许
就会迅速返回罗马,取得皇位。简而言之,未成年的盖乌斯和卢奇乌
斯仍然不是足以服众的皇位继承人。提比略所受的待遇也可以说明这
一点。尽管他和皇室之间已经有了公开的嫌隙,但奥古斯都仍然给他
留下了一条返回罗马的道路,提比略在离开罗马之前刚刚得到的保民
官权力并没有被收回,尤莉亚也仍然是提比略的妻子。所以,严格说
来,提比略依旧是皇室的核心人物。就算尤莉亚的两个儿子都已经开
始踏上仕途,奥古斯都也没有正式地把提比略的引退化为流放。
但奥古斯都并没有早早离世。公元前2年,他第十三次出任执政
官,并且又一次给平民送出了礼物,其数额仍是每人二百四十赛。但
这一回,他只把礼金送给了有资格获得定价的粮食供应的那二十万男
性。此次的名目是庆祝奥古斯都广场和广场中心的复仇者马尔斯神庙
终于开放。复仇者马尔斯神庙(如图11)是属于尤里乌斯家族的纪念建
筑。早在四十年前,奥古斯都就起誓要修建这座庙宇,用以感谢马尔
斯帮助他向行刺恺撒者复仇。奥古斯都广场用于庆祝罗马历史上诸位
英雄的赫赫武功,是他们引领着罗马从一个不起眼的小村庄成长为称
霸地中海世界的强权帝国。[483]整体说来,这座广场体现了奥古斯都
对罗马历史的阐释—武力扩张。广场中心的马尔斯神庙则展示了奥古
斯都的家族史。
奥古斯都还着手举办了一系列大型活动,比如马车竞赛。罗马城
的贵族青年们表演了“特洛伊游戏”,负责管理这项赛事的就是青年
们未来的领导者盖乌斯和卢奇乌斯以及他们的弟弟阿格里帕·波斯图
穆斯(Agrippa Postumus)。有两百六十头狮子在竞技场中被杀死。其
他地方则有角斗比赛。他们还重演了一次波斯人和雅典人之间的海
战,应该是萨拉米斯海战(Salamis),“雅典人”再次取得了胜利。最
后,人们往一座竞技场里灌了大量的水,然后在表演中猎杀了三十六
头鳄鱼。[484]
这些赛事的奢侈程度展现了罗马帝国的财富和权力。当然,在激烈的搏斗中,有人丧命。把大量的水运到城里来模拟一场海战本身就堪称一个了不起的工程成就。但我们同样应该着眼于被杀的动物。狮子应该是从阿非利加运来的。罗马人需要设法用陷阱抓住狮子,然后将其制服,再通过海路运送到意大利,接着把狮子搬运到罗马城内。这一切都要在没有镇静剂的情况下完成。而那些鳄鱼原先肯定栖息于尼罗河。这些来自远方的生物就是帝国的权势的象征,因为这表明罗马帝国已经统治了那些遥远的土地,有能力把这种奇异的野兽运回罗马,用以娱乐大众。换言之,罗马帝国可以用武力夺取全世界的资源来满足罗马人的娱乐需要。鳄鱼还代表着埃及,猎杀鳄鱼就意味着让观众再次感受到奥古斯都先是征服了埃及,然后让他的家族统治了罗马。奥古斯都政权邀请观众一起为帝国、征服、罗马还有奥古斯都的家族进行庆祝。
人们的回应一如事先所安排的那样。奥古斯都本人的描述如下:
元老院、骑士阶层以及全体人民都称我为国父(pater patriae)。这个称号被铭刻于我住所的入口处、元老院以及奥古斯都广场内元老院表决为我而立的驷马战车的下方。[485]
也有史料称这是平民的主意:当奥古斯都离开罗马,待在安提翁(Antium)之时,平民们派出了一个代表团去向他献上国父的称号。奥古斯都拒绝了。但当他来到剧院的时候,有一群戴着桂冠的人再次请求他接受。接着,瓦列里乌斯·梅萨拉在元老院里又一次提议让奥古斯都接受这个头衔。这一回,奥古斯都含泪同意了。[486]
奥古斯都广场成了罗马人举办某些仪式的场所:当男孩子们获得了参军资格之时,他们会被召集到这座广场上,这大概是为了让他们领略辉煌的罗马军事史,鼓励他们主动参军。[487]各地总督和罗马军团的统帅们会从奥古斯都广场出发前往地方省份;元老院会在这座广场上讨论是否要举办凯旋仪式;而获准举办凯旋仪式者要把凯旋头冠献给这座广场上的神庙里的马尔斯。[488]帕提亚人在公元前20年归还的罗马军旗被献给了马尔斯,后来被转移到广场上的神庙里。奥古斯都广场成了尚武的罗马帝国举办各种仪式的核心场所。
公元前2年的一系列活动让罗马看起来国泰民安。所有人都顺从于国父奥古斯都的领导,而他则掌控着帝国的大量资源并且慷慨地将其用于满足人民的需求。奥古斯都政权的信心得到了巩固。盖乌斯将被派往多瑙河流域积累带兵的经验,卢奇乌斯当然迟早也会随他同去,这两位少年都已经成长到可以出任公职的年纪了。政权的继承问题得以解决,皇室的统治地位再次稳如磐石。而且,奥古斯都本人也还健在。随着时间一年年地流逝,他的两位养子都越来越像是合格的领导者,政权的未来也变得越发光明。暴风雨看起来已经过去,王朝的传承危机仿佛已然解决,提比略东山再起的可能性越来越小。罗马人民,或者说,至少那些倾向于君主制者似乎已经可以开始畅想年老的奥古斯都把国家大权平稳地传递到两位前途无比辉煌的外孙手中。
接着,事态急转直下。
[1] 即现在的8月。—译者注
[2] 即现在的7月。—译者注
[445] Dio, 53.12.
[446] Res Gestae , Preface.
[447] Dio, 53.22-26; 53.29; 54.3-5; 54.11; 54.29; Strabo, 16.4; Res Gestae , 26.
[448] Virgil, Aeneid , 1.261-296.
[449] Dio, 54.22; 54.24.
[450] L’Année épigraphique (1973), 323.
[451] Dio, 54.19.
[452] Dio, 54.21.
[453] Dio, 54.25.
[454] Dio, 54.33.
[455] Dio, 54.20.
[456] Dio, 54.24.
[457] Dio, 54.28.狄奥的意思是,阿格里帕正在返回罗马。但是,从巴尔干出发,途经坎帕尼亚返回罗马似乎绕得有点远。
[458] 关于这份吊唁词,可以参考Michael Haslam, “Augustus’ Funeral Oration for Agrippa”, Classical Journal , 75, (1980): 193-199。
[459] Dio, 54.29; 55.8.
[460] Dio, 54.31.
[461] Virgil, Aeneid , 2.97.
[462] Dio, 54.36.
[463] Dio, 55.1-2.
[464] Dio, 55.6.
[465] Dio, 55.8.
[466] Dio, 54.31.
[467] Dio, 54.33.
[468] Dio, 54.34; 55.2; Virgil, Aeneid, 2.98,他提及色雷斯似乎有一场持续了三年的战争。
[469] Dio, 55.2; 55.5.
[470] Dio, 54.12; 54.15. Suetonius, Augustus , 19,他列举了很多参与密谋者的名字,其中既有像李必达、凯皮奥和穆雷纳那样的政界名人,也有其他地位较低的人物,比如据说犯过伪造罪的卢奇乌斯·奥达修斯(Audasius)、出身于伊利里亚的阿西尼乌斯·伊皮卡杜斯(Epicadus)、某个自认为即将当上皇帝的奴隶提里普斯(Telephus)。他还提到了某个不知名的士兵的一位不知名的仆人忽然带着一把大型匕首出现在奥古斯都的卧室里。这份名单的内容让人不敢恭维。
[471] Dio, 55.5.
[472] Dio, 55.14-22. Seneca, De Clementia , 1.9.
[473] Dio, 56.1-10.狄奥详细地记录了奥古斯都的言论。Suetonius, Augustus ,34表示确有此事。显然,奥古斯都还把他的改革和古老的道德观念联系在了一起(请参考Suetonius, Augustus , 89)。Dio, 54.19还记载了之前不满者的行为。
[474] Ovid, Tristia , 2.
[475] Ovid, Ars Amatoria , 1.32-34.
[476] Ovid, Ars Amatoria , 1.269-270.
[477] Ovid, Ars Amatoria , 1.579-580.
[478] Dio, 55.6; Res Gestae , 16,狄奥记载,奥古斯都是在公元前8年给士兵们颁发奖金的,而奥古斯都本人则在Res Gestae 中称他在公元前 7年给老兵们送出了礼物。
[479] Suetonius, Tiberius , 10-11; Dio, 55.9.
[480] Dio, 55.9.
[481] Res Gestae , 14; Dio, 55.9.
[482] Dio, 55.10; Res Gestae , 15.
[483] 请参考Joseph Geiger, The First Hall of Fame: A Study of the Statues in the Forum Augustum (Boston: Brill, 2008); Paul Zanker, Forum Romanum: Die Neugestaltung durch Augustus (Tübingen: Wasmuth, 1972); Paul Zanker, The Power of Images in the Age of Augustu s (Ann Arbor: University of Michigan Press, 1990), 194-195。关于这座广场和文学的具体信息,读者可以参考 Torrey James Luce, “Livy, Augustus and the Forum Augustum”, Between Republic and Empire,Interpretations of Augustus and his Principate , 123-138,edited by Kurt Raaflaub and Mark Toher (Berkeley: University of California Press, 1990)。
[484] Dio, 55.11.
[485] Res Gestae , 35.
[486] Suetonius, Augustus , 58.
[487] 我们不太确定他们具体是怎样举行这个仪式的。希腊城邦有专门的学校(gymnasium,γυμνάσιον,本义大致为赤裸地训练)来教育年轻人(ephebus,ἔφηβος),他们会举办毕业仪式,但罗马人并没有这样一套集中的教育系统。不过,也许奥古斯都想要采用希腊人的做法。
[488] Dio, 55.10.
第十八章 皇帝之死
公元前2年的某个时候,一位裁判官被派往元老院宣读奥古斯都的信件。恐怕没人能够想到其中有着怎样的内容—奥古斯都表示他已经放逐了自己的独女尤莉亚。她离开了罗马,被囚禁于第勒尼安海(Tyrrhenian Sea)上的一座监狱小岛潘达提利亚(Pandateria)。其罪名骇人听闻:尤莉亚举办了过于放荡的聚会;她和伙伴们在广场,甚至演讲台上痛饮狂欢;她还与人通奸。而且,这不是寻常的通奸。据说,尤莉亚极其淫乱,并且偏爱名门之后。与她有染者包括马克·安东尼之子尤卢斯·安东尼乌斯、著名的格拉古兄弟的族人塞姆普罗尼乌斯·格拉古、知名的卫道士昆图斯·克里斯皮努斯、阿皮乌斯·克劳狄乌斯(其家族或许是罗马城中最为显赫的家族)和西庇阿家族的某个成员。除此以外,还有许多传统文献未曾列举出名字之人。其中既有元老,也有骑士。[489]尤卢斯·安东尼乌斯同时被指控谋逆,遭到了处死。其他人则按照通奸罪论处,被判流放。孤岛上的尤莉亚只能过着朴素的生活。岛上还几乎没有男性,任何男子都必须经由奥古斯都批准才能前去。其中的寓意就是,尤莉亚的欲望太过强烈,就连岛上的看守也有可能为她所诱惑。[490]此外,奥古斯都代表提比略和尤莉亚离了婚。
这个事件既与性爱有关,也是宫廷政治运作的结果。古代的史家大多着眼于性行为的那部分,但君主制度下的性和政治显然是难分彼此的。尤莉亚本人的那几段婚姻就是由明显的政治目的促成的。她正好出生于公元前39年屋大维和她的母亲离婚的那一天。自那以后,尤莉亚一生都是奥古斯都政权高层的重要人物。所以,她应该不太可能没有成熟的政治思想。我们很难相信她会认为自己的性行为是一件私事。同时,与她有关系的男性也应该都知道和奥古斯都之女发生非法的性关系会导致怎样的结果,尤莉亚毕竟是有夫之妇。
指控知名的女性生活作风不检点是一种很实用的攻击手段。其背后隐藏着对女性的恶意揣测,认为但凡想要实现某种政治目的或者出于各种原因而想要维持男性朋友圈子的女性都会以性爱为手段捕获某些不设防的不幸男子。攻击者很容易泼出这种脏水,但当事人却很难有效地证明自己的清白。
这一时期的罗马女性不必深居简出。她们可以结交朋友,参加聚会,拥有自己的社交圈。地位较高的女性通常还会处理私底下的政治事务。尤莉亚很可能享有一处独立的住所,而且大概很豪华。她的朋友想必大多来自罗马社会的顶层,有男有女,都有一定的地位和独立性。这些朋友构成了尤莉亚的权势的一部分。当然,她和奥古斯都以及其他显赫的皇族成员之间的关系或许是最重要的。她的两个儿子很可能会继承这个帝国,尤莉亚很明显就是罗马政坛上的权力中介人,某些有抱负的政治人物大概会考虑借助于尤莉亚来实现自己的目的。我们不难想象,她的身边很容易积累起一个势力较大的圈子,其成员大概想在奥古斯都去世之时分享尤莉亚的政治资源。在公元前2年毁于一旦的就是这个圈子。
尤莉亚的倒台没有明显的原因。我们大概可以认为很多人其实都不相信关于尤莉亚的淫乱行径的说法。尤莉亚身边一位得到了解放的前女奴菲比(Phoebe)在尤莉亚的污名传播开来以后选择了自杀,此事被视作尤莉亚的卑劣道德品质污染了其家人。尤莉亚之母斯克里波尼娅则陪同尤莉亚一起前去潘达提利亚,这既是个人行为,也是一种政治姿态,仿佛在说通奸之事并不属实。对于奥古斯都提出的说法,众人还须审慎地思考一番。五年以后,罗马人民示威支持尤莉亚,要求把她召回罗马,她在人民心中并不是那么不堪。但奥古斯都拒绝了。[491]
在皇室内部,提比略和尤莉亚及其儿子之间有着深刻的裂隙,双方的矛盾非常激烈。即使是在十四年以后提比略登基之时,他也血腥地收拾了尤莉亚的残党。不过,在公元前2年,就算我们很想推测提比略和尤莉亚的倒台有关,也不能忽视提比略本人此时还隐居在罗德岛上。他的影响力一直在衰减,恐怕难以和尤莉亚等人展开竞争。提比略的时代看起来已经过去了。况且,提比略并非尤莉亚倒台的直接受益人,他依然留在罗德岛上,我们没有看到这位戴上了绿帽子的丈夫忽然归来。所以,我们很难说提比略获得了什么好处,也就无从断定是提比略的支持者策划了尤莉亚的失势。
此次事件最有可能源于尤莉亚和奥古斯都之间的矛盾。此时的奥古斯都已经年逾六十,这在当时算是比较老了。而尤莉亚正在贵族中拉拢支持者,以便应对奥古斯都的突然驾崩。这种准备需要做得很妥当才行,但尤莉亚的做法也许显得太急切了一些。以人之常情而论,我们可以理解年事渐高的奥古斯都或许会觉得有些反感。从政治角度而言,尤莉亚的政治集团或许看起来在热切地期盼着奥古斯都时代落下帷幕。不过,光凭这一点,我们难以解释为什么奥古斯都要采用那样残酷的手段,尤莉亚必定做了让奥古斯都认定她在背叛自己的事情。
指责其作风淫乱确实是毁掉皇族女性的最佳捷径,但如果尤莉亚
的倒台只是因为政治上的分歧或者说她在图谋不轨,那么我们就不得
不考虑一下为什么奥古斯都要指责她通奸了。毕竟,通奸的罪名让此
次事件的政治影响扩大了很多。奥古斯都有必要让他的两位继承者的
母亲被视作一个水性杨花的女子吗?只将她定位为奥古斯都的政敌或
许已经足够。如果通奸纯粹是尤莉亚的对手炮制出来的罪名,那么奥
古斯都怎么会没能识破这种花招呢?虽然相关史料看起来只是逸闻,
我们不能全盘相信,但奥古斯都似乎真的认为尤莉亚犯下的不是政治
问题,而是生活作风问题。无论尤莉亚和她的朋友们究竟是否犯下了
通奸罪,我们都不能认为性丑闻只是一个借口。恰恰相反,这就是此
次事件的核心。
控诉尤莉亚在性生活方面有违道德规范是具备意识形态上的意义的。奥古斯都政权长期致力于把道德教化和自己的政治地位联系在一起。早在公元前28年之时,奥古斯都就试图展开道德改革。在公元前18年以后,奥古斯都政权把这种尝试付诸实践。他们认为重新树立古老的道德观念有助于根除内乱,促进帝国的扩张。这些道德改革是奥古斯都为他自己和他的政权寻求统治正当性的途径[实行道德改革时,奥古斯都是监察官(censor),或者说“法律和习俗的维护者”],[492]奥古斯都的君主制政权把自己塑造为传统的捍卫者。显然,他因此遇到了强大的阻力。
不难想象,尤莉亚等人在道德问题上要比奥古斯都宽松得多。君主制度让统治者的家族得以通过奢侈的生活作风来展示其高人一等的统治地位,[493]安东尼和克莱奥帕特拉走过的道路未必不能为罗马皇室所用。奥古斯都时代后期的道德约束是比较严苛的,尤莉亚及其支持者有可能利用人们对奥古斯都的政策的不满,他们需要做的就是以自己的行为展示出罗马皇室的另一种可能的形象。因此,放纵的生活方式具备了政治意义。对待性行为的宽松态度可以被视作一种不同的政治道路的标志,让尤莉亚更接近于普罗佩提乌斯和奥维德,而不是古老的共和国传统。这必定会引发争议。
我们恐怕不能把尤莉亚遭到流放的原因单单归结到某一个点上。奥古斯都和她是父女,他们的关系难免公私并存。宫廷政治无疑和迷宫一样复杂,他们二人之间的争执有关皇室的未来、道德以及罗马政治文化的本质。奥古斯都通过流放尤莉亚再次申明了他将近三十年来宣传的图景仍然不会发生变更。奥古斯都时代的宫廷政治确实非常残酷,奥古斯都不惜用流放独女的极端手段来消除人们质疑其政策的声音。同时,这也再次显示了奥古斯都的权力。无论尤莉亚及其亲信看起来多么有权有势、人脉深厚,只有奥古斯都才能决定罗马皇室乃至罗马前进的道路。
不过,鉴于这个问题干系重大,尤莉亚的流放并没有真的消除反对的声音。后来,人们为了支持尤莉亚而集会示威。我们可以将其与反对婚姻法的示威联系起来,因为这些示威的参与者都是在反对奥古斯都宣传的意识形态当中的核心要素。
尤莉亚的污名并没有对皇权的传承产生明显的影响,此时的两大可能性分别是盖乌斯和卢奇乌斯继承奥古斯都的位置或者提比略成为皇帝,而尤莉亚的突然失势没有妨碍她的两个儿子继续擢升。较为年轻的卢奇乌斯·恺撒被派往高卢去拜访地方上的知名人物,并且熟悉一下帝国的重要省份。盖乌斯则被派往多瑙河流域,但他很快就转去了东方。自提比略受命出征的公元前6年以来,亚美尼亚的问题一直没有得到解决。帕提亚和亚美尼亚结成了同盟,威胁着罗马的霸权,虽然奥古斯都并不觉得有必要在盖乌斯堪当大任之前派人前去。盖乌斯的任务就是去威吓帕提亚和亚美尼亚人。此次事件和公元前20年如出一辙,帕提亚人又一次面对着一位渴望在战争中赢得荣耀的皇子。于是,他们做出了同样的选择—求和。不过,亚美尼亚决定应战。[494]
盖乌斯的东征不仅仅威胁到了帕提亚人。虽然提比略看起来像是
已经安于过着平静的生活,但应该没有人会相信他真的打算在罗德岛
上度过余生。提比略没有完全放弃自己的政治前途,罗马也没有彻底
遗忘提比略。前往东方赴任的各位总督一般都会明智地落脚于罗德
岛,拜见这位曾经的皇位继承人。不过,随着盖乌斯和卢奇乌斯渐渐
长大,提比略的待遇越来越差。高卢地区的内毛苏斯(Nemausus)的公
民决定推倒当地的提比略像。一般说来,这种明显具有政治意味的行
为可以被视作造反,但卢奇乌斯看起来对他们的做法至少有一些赞
同,他让当事者免受惩罚。[495]远在高卢的卢奇乌斯并不能直接影响
提比略,而盖乌斯却在东方掌握着大权,想必他也不能在未经奥古斯
都许可的情况下伤害提比略。
有谣言称提比略正在策划阴谋。据说,他想要收买百夫长来行刺盖乌斯。假如盖乌斯“察觉”了提比略想要杀害自己,那么他或许就可以不请示奥古斯都而将其处死。提比略离开了罗德岛,亲自过来拜见这位年轻的恺撒。年长的提比略不得不忍受屈辱,向他求饶。这充分说明了权力的天平已经逆转。[496]当时有传闻称,在盖乌斯举办晚宴之时,有某个人曾经站起来自告奋勇,要去罗德岛上替盖乌斯把“流亡者”的头颅给带回来。对于提比略而言,东方越来越危险了,于是他请求返回。奥古斯都同意他在公元2年回到罗马。其条件是,他必须继续远离政事。
然而,公元2年,年仅十九岁的卢奇乌斯患上了急病,在8月20日死于马赛。[497]提比略是这件事情的明显受益者,他因此成了各种谣言的主角。而且,事态进一步地恶化了。此时,盖乌斯正在亚美尼亚作战。驻防据点的某位敌将诱骗他前去会谈,然后趁机攻击了他。盖乌斯受了伤。罗马人继续围攻,并且最终击败了亚美尼亚人,取得了战争的胜利。按照罗马传统,获得了胜利的盖乌斯被部下尊为“大将军”(imperator)。但盖乌斯的伤情每况愈下。[498]他派人传讯给奥古斯都,请求暂停职务,以便养伤。奥古斯都无可奈何地同意了,但要求盖乌斯返回罗马。公元4年4月23日,盖乌斯去世了。
流亡者归来
奥古斯都现在几乎别无选择,他收养了提比略以及阿格里帕和尤
莉亚最年幼的儿子阿格里帕·波斯图穆斯。提比略被要求收养了他的
侄子日耳曼尼库斯,后者的妻子则是尤莉亚和阿格里帕的女儿阿格里
皮娜。这一轮家族关系的重组确立了三个潜在的皇位继承人,但只有
提比略具备足够的资历和权威。现在,奥古斯都对他以政治伙伴相
待,提比略很快就被派往日耳曼尼亚去再次展现奥古斯都政权武力扩
张的本质,但是他同时也是罗马政务的核心人物。帕提亚国王派使者
前来罗马,以求修复他和奥古斯都的关系。奥古斯都和元老院接见了
这些使者,但要求他们必须也去拜见提比略。[499]
日耳曼尼亚当时是罗马扩张的主要方向。提比略把罗马的边界推
进到了更加靠东的地带。但是,在公元6年,多瑙河流域的省份爆发了
叛乱。为了给日耳曼尼亚的战事提供源源不断的人力,提比略在达尔
马提亚召集了部队。于是,达尔马提亚人有了一支自己的军队(虽然严
格说来这支部队应该服从于罗马)和一位领导者—一个名为巴托(Bato)
的人。巴托号召这些刚刚集结起来的部队一起反抗罗马统治者,他们
在初期取得的一些成功还引得潘诺尼亚的布留奇人(Breucian)也加入
了造反的队伍,这个部落的领导者同样名为巴托。默西亚总督塞维鲁
(Severus)率军去镇压叛乱,但他的所谓“胜利”的结果是,潘诺尼亚
人依旧为所欲为,而他却撤离了。达尔马提亚的那位巴托带兵南下,
据说罗马人同样击败了他。然而,这些“得胜”的罗马军队也撤离
了。
帝国需要提比略。他领军从日耳曼尼亚回到了南方,以便保护意
大利。战争的形势已经非常严峻,有一个罗马殖民地遭到了毁灭,罗
马人估计叛军有八十万之众。[500]日耳曼尼库斯也受命出征,他所得
到的那支部队是紧急征召而来的,其中除了自由民以外还有奴隶和前
奴隶。[501]值得我们注意的是,阿格里帕·波斯图穆斯明明已经达到
了可以参军的年纪,却没有得到任用。[502]此时,提比略手中控制的
军队包括十个军团(五万人)、七十个大队(三万五千人)、十四个骑兵
单位(七千人)、紧急应征的一万老兵以及色雷斯的附庸国王派来的征
召兵。这些部队加起来至少有十万两千人,而整个帝国平时的军队总
数也不过是二十五万人而已。
这场战争说明了奥古斯都十分依赖于提比略。此外,无论他具体
是如何实现的,提比略成功扫除了其继位道路上所剩无几的障碍。尤
莉亚仍在流放中,盖乌斯和卢奇乌斯都已去世。现在,最有可能挑战
提比略的就是阿格里帕·波斯图穆斯。虽然奥古斯都也把他收作了养
子,但他的处境还是非常危险。很快,他就遭到了政敌的攻击,被逐
出了罗马,[503]其罪名和他的道德品质有关。据说,他的品行不佳,
比较暴躁(会让人联想到疯狂)、粗野。[504]我们不难想象,阿格里帕
也许只是因为自己没能得到任命而感到愤怒。阿格里帕的姐姐尤莉亚
同样被除掉了,她被指控通奸。而她的丈夫,出身豪门的卢奇乌斯·
埃米利乌斯·保卢斯则因谋逆而获罪。[505]奥古斯都还把尤莉亚在帕
拉提翁山上的住所夷为平地。[506]尤莉亚被流放之时有孕在身。于
是,奥古斯都命人杀死了他的曾外孙。尤莉亚本人则于公元29年去
世,她在死时仍然是一名流亡者。[507]
时至公元8年末,潘诺尼亚战事进展顺利。提比略便以征服者的英
雄身份返回了罗马,年逾七十、越来越瘦弱的奥古斯都离开了皇宫,
亲自出城相迎。所有人都能明白,这是年老的现任皇帝在陪伴未来的
皇帝返回皇城。[508]日耳曼尼库斯继续在达尔马提亚作战到了第二
年。这年夏天,提比略重返前线,最终和他一起结束了这场战争。
[509]然后,日耳曼尼库斯回到了罗马,向人民汇报胜利的喜讯,元老
们则又一次报之以各种各样的荣誉。奥古斯都和提比略获准举办凯旋
仪式,游行于罗马的街道上,虽然他们也许表示过推辞。[510]元老们
还表决同意了建造凯旋门,这些都是比较重大的荣誉。相比之下,日
耳曼尼库斯得到的奖励规格不高,但或许更加值得我们关注。此时,
他只有二十四岁,还很年轻,却得到了裁判官的待遇,这是仅次于执
政官的高位。他还获得了在各位前任执政官之后第一个发言表达意见
的权利,这种荣誉和之前的马尔凯卢斯、提比略、德鲁苏斯、盖乌斯
还有卢奇乌斯一脉相承,是属于皇族成员的快速擢升。[511]
随着日耳曼尼库斯开始崭露头角,皇室的未来看起来再次有了保障。奥古斯都现在已经过于年老,无法亲自上阵打仗,但五十一岁的提比略仍处于其政治、军事生涯的盛期。他的侄子日耳曼尼库斯在支持着他。而且,他的儿子德鲁苏斯很快也可以受任军职了。皇室的未来似乎一片光明,虽然在罗马人宣布庆祝潘诺尼亚的胜利之后仅过了五天,日耳曼尼亚就传来了一个可怕的噩耗。
日耳曼人叛乱
日耳曼尼亚这些年的战争已经让罗马的边界线从莱茵河推进到了
易北河,今天德国西部的大部分土地都成了帝国的领土。公元9年,罗
马人没有展开战事,这大概是十年以来的第一次。他们转而致力于建
立政治和其他领域内的秩序。新任总督瓦卢斯(Varus)是一位经验丰富
的将领,他和奥古斯都政权高层的关系也很近。此时,他认为已经可
以正式地展开日耳曼尼亚的行政工作,征收税款了。[512]为此,瓦卢
斯召来了日耳曼尼亚的重要人物,希望他们成为自己的顾问。此前或
许从未有过如此多的日耳曼首领聚集在一起,这为他们提供了一个绝
佳的密谋时机。
叛乱的领导者名为阿尔米尼乌斯(Arminius),他和瓦卢斯的关系
很近。叛乱者的计划比较细致,并且凝聚了多方的力量。他们让瓦卢
斯得知日耳曼尼亚境内某个偏远的地方爆发了一场叛乱。于是,瓦卢
斯召集了部队,打算和日耳曼盟军一起去解决这场看起来规模不大的
小骚动。然而,在行军时,同行的日耳曼人找了各种各样的理由,陆
续离开。与此同时,更加偏远处的小型罗马据点也受到了攻击,其中
的士兵遭到了屠杀。当瓦卢斯终于发现自己面对的是一场大规模叛乱
之时,他已经深陷于日耳曼人的势力范围。他只得下令全军开始争取
撤回莱茵河畔。士兵们带上了奴隶、家眷和财物,顶着这些负担在日
耳曼尼亚的森林里缓慢前行。
日耳曼人知道瓦卢斯的行军路线。他们砍断了大树,用以拦住罗马人的去路。罗马人的队列很长,日耳曼人可以从容地选择可能的薄弱点,发起进攻。罗马军队能够组织起来应战,却无法进一步解决问题。[513]随着负伤士兵越来越多,行军的速度变得更慢了,就连瓦卢斯本人也受了伤。绝望之中,他们加强了某个据点的防备,然后烧掉了自己无力再保住的货车。如此一来,他们可以轻装简行,更快地撤离。然而,四天以后,他们仍旧被困在日耳曼尼亚的森林里。
瓦卢斯召集了高级军官来商量对策。在审时度势之后,瓦卢斯及其下属军官选择了自杀。罗马军队崩溃了。一些人试图逃跑,但日耳曼人将其砍倒,任由其尸体在林间的道路上腐烂。还有一些人被抓住,受到了折磨,或是被献祭给了神灵。[514]总共三个军团及其辅助部队、奴隶、家眷以及随军商贩尽数覆没,遇害者总数在两万到三万人之间,莱茵河以东的日耳曼尼亚领土全部丧失。[515]
这个噩耗令罗马人深感震惊,奥古斯都换上了丧服。据说,他曾经一边用头撞击门框,一边呼喊着:“昆克提里乌斯·瓦卢斯(Quinctilius Varus),还我军团!”[516]提比略立刻被派去了莱茵河畔。[517]同时,奥古斯都开始着手征兵。不过,有一些人不太愿意应征献身于这场漫长而艰难的战争,他们设法避免了被征召入伍。因此,奥古斯都剥夺了他们的公民权和财产。奥古斯都还鼓励老兵们重新入伍参战,并且把得到了解放的前奴隶也招入了军队。这些匆忙召集起来的部队被派去了高卢,支撑着莱茵河防线。[518]公元11年,提比略和日耳曼尼库斯率军再次出击,这是罗马人唯一的战斗方式。[519]
阿尔米尼乌斯领导的这场叛乱是奥古斯都时代的最后一场大规模
战争,罗马的军事资源已经被运用到了极限。潘诺尼亚的叛乱被镇压
了下去,当地的领土失而复得,但日耳曼尼亚的战争让罗马人遭遇了
一场大败。罗马军队的人员伤亡相当惨重,而平定潘诺尼亚叛乱已经
让罗马人消耗了不少的人力,他们很难迅速地补上日耳曼尼亚的缺
口,奥古斯都的征兵活动非常不受欢迎。此后,罗马人再也未能夺回
丧失的土地。
不过,尽管这些叛乱给皇室的军功簿上增加了一个污点(虽然传统
观点把绝大部分责任都归结到了无能的瓦卢斯头上),但从长远来看,
帝国政权并没有遇到一场政治灾难。恰恰相反,奥古斯都政权得以由
此向罗马人民说明,罗马仍然需要一支纪律严明的强大军队,提比略
得以再次展现其军事能力。日耳曼尼库斯则在平叛时初次掌兵,并且
获得了属于自己的军事胜利。在镇压了潘诺尼亚叛乱以后,提比略和
日耳曼尼库斯可以将自己塑造为意大利的拯救者。在公元11年的日耳
曼尼亚战事以后,他们更是成了罗马军队名誉的恢复者。在公元14
年,帝国政权完全可以把日耳曼尼亚和潘诺尼亚的战事宣传为说明帝
国政权存在的必要性的正面例子。而且,提比略就是那个能够带领罗
马人民维持大国霸权的领袖。
奥古斯都之死
公元13年,奥古斯都宣布自己不再出席公共宴会。他要求各位元老不要再来他的家中致以问候,或者,至少不要频繁拜访。[520]第二年,他离开罗马,去为再度出征北方的提比略送行。途中,奥古斯都患上了疾病,转而前去他在坎帕尼亚的庄园休养。他的病情有所好转,提比略便踏上了旅途。接着,奥古斯都来到了纳波利(Neapolis)观看比赛。然而,他其实并没有完全康复,再度变得虚弱的奥古斯都回到了位于诺拉(Nola)的祖宅,并且命人召来提比略。
奥古斯都知道自己命不久矣,他派人去召集自己的亲朋好友来陪伴自己度过最后的时光。他对他们吟诵了一首希腊语诗,要他们为一位已经出色地完成了使命之人喝彩。接着,他便让他们离去了,最后陪伴在他床边的是他的妻子莉薇娅。公元14年8月19日,罗马历史上第一位皇帝奥古斯都安详地离开了人世。他一生经历了七十五度春秋又十个月二十六天,在他死后十三天就是阿克提翁海战的四十四周年。[521]
提比略也许未能及时赶到诺拉来见奥古斯都最后一面。不过,当他和莉薇娅一起对静候讣告的帝国臣民传达丧讯之时,他们已经完全掌控了局面。提比略在控制了禁卫军以后开始准备返回罗马。早在丧礼举办之前,这一年的两位执政官、禁卫军长官以及供粮官就已向提比略起誓效忠;某些会议上的平民和罗马的驻军或许也已发誓要为提比略效劳;他给帝国境内各地的军团和总督写了信件;他所到之处都有士兵随行。[522]罗马政局的新形势已经非常明显:提比略一如人们所预料的那样继承了奥古斯都的地位。
共和国没有恢复,也没有人想要使其恢复。罗马城内无人可以反对提比略的继位,唯一有可能挑战其地位的是他的族人,但他很快就将其抹除干净了。尤莉亚仅剩的儿子阿格里帕·波斯图穆斯被杀死了,成为新政权的第一位受害者。[523]提比略还派士兵去杀死了塞姆
普罗尼乌斯·格拉古,据说他是尤莉亚的情人。提比略显然认为就算
经过了十四年的流放,他也应该遭到处死。[524]尤莉亚则自杀了。多
瑙河流域以及日耳曼尼亚境内都有罗马军队哗变。日耳曼尼库斯一度
看起来有一些机会争夺皇位,但这位年轻人对皇室忠心耿耿。[525]就
算这些士兵真的成功了,他们也只会让日耳曼尼库斯给他们提供报酬
并且索取更好的待遇,绝不会让共和国复苏。无论人们私底下怎样看
待奥古斯都的一生,至少在公开的场合,诸位元老和骑士、平民和士
兵都在为奥古斯都的离去而悲痛不已。新任皇帝提比略平静地看着人
们把奥古斯都从罗马的第一人升格为皇室的第二位神明—神圣的奥古
斯都(Divus Augustus)。
此次和平的政权更迭是奥古斯都政权的一大成就。作为后人,我
们或许会觉得提比略的上台是奥古斯都时代理所当然的结果。毕竟,
我们知道奥古斯都是第一位罗马皇帝。而罗马帝国的历史至少延续到
了公元475年,东罗马帝国甚至延续了更久。我们知道在他把提比略
(他出自克劳狄乌斯家族)收入尤里乌斯家族以后就有了我们所知的尤
里乌斯-克劳狄乌斯王朝,而这个家族里还涌现了盖乌斯·卡里古拉、
克劳狄、尼禄[1]这些皇帝。但是,在公元前28年,当屋大维和阿格里
帕着手构建奥古斯都共和国之时,没有人能够预料到这一切。
奥古斯都共和国的存在也许确实是一个自相矛盾的奇怪现象,但至少这种矛盾很有用,帝国政权愿意将其维持下去。即使是在盖乌斯·恺撒去世,提比略重返罗马政坛前台以后,他和奥古斯都也还在小心翼翼地宣传着共和国的遗产。提比略的继位是因为他是奥古斯都的养子、莉薇娅仅剩的儿子、奥古斯都家族的中流砥柱,但也同样是因为他是同代人当中最杰出的将领,他曾经领军作战于亚美尼亚、雷蒂亚、多瑙河流域、日耳曼尼亚。他不仅击败了叛乱的潘诺尼亚人,还在日耳曼尼亚的战场上恢复了罗马人的荣耀。以军事化的罗马政治文化来看,提比略毫无疑问是名望最高、功绩最大的将军。
提比略也是当时最有经验的政治人物。他曾经在公元前13年和公元前7年两度出任执政官,也曾在“退隐”之前和之后与奥古斯都一起掌握保民官权力。当奥古斯都去世之时,提比略已经重返政坛十年了。他完全可以卓有自信地宣称自己就是国家的领导者,是唯一拥有足够的经验和权威去继承奥古斯都之人。
不过,就算提比略试图以其履历来说明自己继位的正当性,让更
加保守、更加拥护共和制度的那些人感到有些亲切,罗马政治现在的
实质也无疑是君主制。在奥古斯都时代末期,罗马人民已经充分表明
了他们愿意拥抱君主制度。元老院给奥古斯都颁发的无数特殊荣誉也
足以说明他和元老之间绝非共和国时代平等共事的关系。盖乌斯和卢
奇乌斯的迅速擢升也是罗马转向君主制度的明证,因为如果以共和制
度的眼光来看,他们二人只是别无特殊长处的两个年轻人。尤莉亚及
其子女的生活方式奢侈无比,更接近于克莱奥帕特拉的宫廷生活,而
非古代罗马的卫道士们推崇的简朴之道。盖乌斯和卢奇乌斯纯粹是因
为不幸才未能取代资历更深的提比略。
公元14年,或许提比略在奥古斯都的赞同下选择了利用奥古斯都
确立的这一套制度中共和制的成分,也许这是为了说明为什么继位者
是他而非其他的皇室成员,也许这是为了再一次强调罗马需要有一位
强大的领袖来带领人们与边疆的潜在敌人作战。于是,提比略陷入了
共和君主制的悖论,在其统治前期的很长一段时间里表现得顺从于诸
位元老。这大概反而让元老们感觉到有些困惑,因为元老们同样能够
认清皇权的实质:提比略控制着军队和帝国。他所掌控的财力、军力
以及政治资源远超其他元老的想象,所有人都必须如临深渊地对待提
比略,没有人胆敢冒犯他。无论他对元老们说了什么,无论他表现得
多么尊重元老们的集体智慧,罗马只有一位至高无上的统治者。
提比略在罗马的漫长历史上享有一个非常奇特的位置。在所有的
史料当中,他都是一个深深浸染着罗马传统道德、思想的人物。然
而,当他最终继承奥古斯都的地位之时,罗马的政治制度已经发生了
巨大的变化。他置身于帝国时代,共和国只存留在人们的记忆里,虽
然这份记忆仍然具备一定的力量,许多人或许还会怀念那个时代,某
些元老也许还曾幻想过要恢复共和制度下的自由与荣耀。不过,就算
在公元14年以后真的有人曾经将这种梦想付诸实践,发起了一场恢复
共和国的政治运动,他们也未能在史料中留下自己的身影。[526]罗马
经历了一场革命,没有人能够倒行逆施。
罗马革命
自恺撒遇刺到奥古斯都去世,在这五十七年当中,绵延将近五百
年的罗马共和国被扫到了历史的垃圾堆里,这一事实本身就足以证明
“革命”的存在。认可这一说法的一部分困难在于,我们通常会以国
家机关的变迁来鉴别政治的形态—这是承继自希腊人的习惯。今天,
我们一般认为革命就意味着政府的整体框架发生了变化,国王会被送
上断头台;或者君主的军队和代表会被遣散,民主政权或许会从中诞
生。然而,罗马革命并没有带来国家机关的革命,元老们仍然正常地
召开会议,官员的人数和权力大致如故,选民们依旧集会表决。如果
仅仅着眼于这些国家机关,我们甚至很难分辨出公元14年的罗马和五
十年以前到底有什么区别。
但是,罗马确实经历了革命。当布鲁图斯和卡西乌斯在恺撒血淋
淋的尸体旁边高举匕首之时,他们满怀信心地期待着罗马的政治秩序
能够恢复过去的面貌,期待着元老们能够再次统治这个国家。在接下
来的岁月里,罗马的军人们成了政治舞台上不容忽视的重要角色,罗
马的贵族阶层遭到了三头同盟的蹂躏,旧时代的政治秩序倒在了血泊
当中。公元前28年以后的复苏只是有条件的部分恢复,元老们再也无
法控制罗马的军队、财富和平民。渐渐地,随着奥古斯都垄断了权力
的实质(金钱与暴力),他的影响力进一步延伸到了元老们身上,他能
够决定元老们的升降。
元老们之所以没有被铲除,是因为他们顺利地融入了奥古斯都的新政权。奥古斯都并没有事先准备好某种宏大的计划或蓝图,帝国政权对新秩序的要求只是:国家大权必须高度集中于奥古斯都及其亲信手中。任何反对这一点的机关或个人都会被铲除,所有人都不得不服从。自公元前43年起,一张私交关系网络便成形了,它最终统治了罗马政治的方方面面。迫使罗马经受了一场革命的就是这张关系网络,而不是某个机关或者某个不满的群体。但是,它同样是一股非常强大的政治势力。
后人眼中的奥古斯都时代是相当辉煌的。在经历了几十年的动荡以后,奥古斯都政权转而致力于维护秩序与和平。它鼓励人们创作优秀的艺术品,主持兴造了许多建筑,给罗马城和皇室都增添了光彩。我们完全有理由相信当时真的有很多人拥护奥古斯都,平民和士兵几乎没有理由哀悼共和国时代的逝去。不过,这种和平与秩序是有代价的,帝国制度以暴力和腐败的手段换来了人民的认可。或许自由公民
的权利与特权在共和国时代会被滥用,但在帝国时代则几乎失去了意义。帝国政权控制了巨量的资源,使得其权力几乎毫无限制。在奥古斯都和提比略以后,这种几乎无限的权力便孕育出了暴君。唯一能够限制他们任意妄为的大概就是他们的想象力了。奥古斯都时代的罗马是一个极权主义国家,他致力于控制公民的生活,让他们帮助自己实现帝国扩张的目标。在奥古斯都的黄金时代,人们需要服从于铁一般
的纪律,就连他们的卧室也成了促进帝国延续的战场。帝国政权的反对者被排挤到了政治舞台的边缘,被迫以阴谋或者文学讽刺的形式来表达其敌意。为了支持帝国在边疆展开的军事行动,罗马的政治秩序得到了重塑。军队始终是奥古斯都政权的一大支柱。人们也许会认为军队是一股很少现身的政治势力,当权者们会尽量让这个不受欢迎的组织隐藏起来。然而,奥古斯都及其家人既是显赫的政治人物,也是
功绩卓著的将军。他们正是靠着军队才赢得了无人能及的权威、名望和财富,然后统治了罗马。在奥古斯都政权与罗马人民展开的政治交易当中,奥古斯都为人们提供的不仅是和平,还有军事胜利和大帝国的荣耀。西班牙、雷蒂亚、日耳曼尼亚、达尔马提亚、潘诺尼亚、色雷斯、亚美尼亚和阿非利加的人民都为他的这个承诺付出了代价。
在评价奥古斯都的成就之时,我们绝不能忘记因他而丧命的那些人,内战、追杀公敌、铲除密谋者以及罗马帝国的扩张战争让无数罗马人和非罗马人失去了生命。许多历史学家和政治人物都赞美过罗马人建立的帝国,并且尤其推崇奥古斯都时代。但是,在欣赏各位恺撒和他们的文明之前,我们还应该仔细地思考一下罗马人民为了帝国的利益而付出了什么代价。我们应当记住那些与主流不合、常常遭到打压的声音,比如基督徒。我们也许还会想到那些在残酷的宫廷斗争中失利遇害的贵族。我们还应看到,罗马帝国是一个极其不平等的社会,贵族与奴隶、富人与穷人之间有着一道不断扩大的鸿沟。总而言之,我们应该思索人们为了所谓的和平的帝国时代而失去的自由的价值。
[1] 这三位皇帝分别是尤里乌斯-克劳狄乌斯王朝的第三任、第四任、第五任(也是最后一任)皇帝。其中,卡里古拉、尼禄都是罗马帝国历史上著名的暴君。—编者注
[489] Velleius Paterculus, 2.100; Dio, 55.10.
[490] Suetonius, Augustus , 65.
[491] Dio, 55.13.
[492] Res Gestae , 6.
[493] 请参考Catharine Edwards, The Politics of Immorality in Ancient Rome(Cambridge, UK: Cambridge University Press, 1993)。
[494] Dio, 55.10A.
[495] Suetonius, Tiberius , 13.
[496] Dio, 55.10A; Suetonius, Tiberius , 12.
[497] 请参考Fasti Antiates 。
[498] Dio, 55.10A.
[499] Suetonius, Tiberius , 15-16.
[500] Dio, 55.29-30; Velleius Paterculus, 2.110.
[501] Dio, 55.31.
[502] Dio, 55.22.
[503] Dio, 55.32.
[504] Tacitus, Annales , 1.3; Dio, 55.32; Suetonius, Augustus ,64-65.
[505] Suetonius, Augustus , 19.据说和尤莉亚私通者中有一人为迪奇穆斯·尤尼乌斯·西拉努斯。他遭到了流放,但在提比略时代获准返回罗马。其条件是,他必须远离公众的视野。读者可参考Tacitus, Annales , 3.24。
[506] Suetonius, Augustus , 72,他以摧毁这幢房屋为例,表明奥古斯都在居住方面比较简朴。
[507] Tacitus, Annales , 4.71.
[508] Dio, 55.33-34; 56.1.
[509] Dio, 56.16.
[510] Res Gestae , 4.
[511] Dio, 56.17.
[512] Dio, 56.18; Velleius Paterculus, 2.117-118.
[513] Dio, 56.19.
[514] Tacitus, Annales , 1.60-62.
[515] Velleius Paterculus, 2.117.
[516] Suetonius, Augustus , 23.
[517] Velleius Paterculus, 2.121.
[518] Dio, 56.23.
[519] Dio, 56.25.
[520] Dio, 56.27.
[521] Suetonius, Augustus , 100; Dio, 56.29-30; Tacitus, Annales , 1.5; Velleius Paterculus, 2.123.
[522] Tacitus, Annales , 1.7.
[523] Tacitus, Annales , 1.6.
[524] Tacitus, Annales , 1.53.
[525] Tacitus, Annales , 1.16-54.
[526] 在盖乌斯·卡里古拉遇刺以后,元老们似乎一度考虑恢复共和国,但他们无法掌控军队,所以,这个主意很快就被放弃了。
年表
重要人物简介
本名单只列举了本书中出现的重要人物,按照这些人物最为人所知的名字的拉丁字母先后顺序而定。例如,提比略·克劳狄乌斯皇帝会以提比略的名字排序,虽然他的家族名是克劳狄乌斯。
马尔库斯·维普萨尼乌斯·阿格里帕(Marcus Vipsanius Agrippa):奥古斯都的亲密战友。他后来成了奥古斯都的副手暨指定的继承人。
阿格里帕·波斯图穆斯(Agrippa Postumus):奥古斯都的外孙,阿格里帕与尤莉亚之子。
阿格里皮娜(Agrippina):奥古斯都的外孙女,阿格里帕与尤莉亚之女,日耳曼尼库斯的妻子。
卢奇乌斯·多米提乌斯·艾诺巴尔布斯(Lucius Domitius Ahenobarbus):曾经是塞克斯图斯·庞培麾下的舰队统帅,后来投靠了安东尼。
亚历山大·赫利俄斯(Alexander Helios):克莱奥帕特拉与安东尼之子。
卢奇乌斯·安东尼乌斯(Lucius Antonius):马克·安东尼的弟弟。他在佩鲁西亚战争中与屋大维交战。
马克·安东尼(Mark Antony):三头之一。
巴托(Bato):达尔马提亚人。他带领达尔马提亚军队发起了反抗罗马的叛乱。
巴托(Bato):潘诺尼亚的部落酋长。他领导了一场反抗罗马的叛乱。
尤尼乌斯·布鲁图斯(Junius Brutus):刺杀恺撒行动的领导人。
法尼乌斯·凯皮奥(Fannius Caepio):公元前22年的谋逆者。
恺撒里昂(Caesarion):克莱奥帕特拉与尤里乌斯·恺撒之子。
昆图斯·卡里努斯(Quintus Calenus):安东尼的支持者及代表。
迪奇穆斯·卡尔弗里努斯(Decimus Carfulenus):屋大维军中的著名军官。
盖乌斯·卡西乌斯(Gaius Cassius):刺杀恺撒行动的领导人。
卢奇乌斯·塞尔吉乌斯·喀提林(Lucius Sergius Catilina):公元前63年的谋逆者,其谋逆被西塞罗成功镇压。
(小)加图(Cato):著名元老及卫道士。在恺撒与庞培的内战中支持庞培,于乌提卡之战失败以后自裁。
昆图斯·卡图卢斯(Quintus Catulus):公元前78年的执政官,苏拉时代以后的重要人物。
马尔库斯·图利乌斯·西塞罗(Marcus Tullius Cicero):著名的政治家、演讲家。在尤里乌斯·恺撒遇刺以后成了元老们的领袖。
卢奇乌斯·秦纳(Lucius Cinna):在马略和苏拉的争斗中支持马略的执政官。
克莱奥帕特拉七世(Cleopatra Ⅶ):埃及女王,尤里乌斯·恺撒的情人,马克·安东尼之妻。
克莱奥帕特拉·塞勒涅(Cleopatra Selene):克莱奥帕特拉与安东尼之女。
克洛狄娅(Clodia):克洛狄乌斯与富尔维娅之女。她一度是屋大维的妻子。
普布利乌斯·克洛狄乌斯(Publius Clodius):深受平民拥戴的政治人物。他与西塞罗、米洛不和,在公元前52年遇害。
科涅莉亚(Cornelia):秦纳之女,恺撒的第一任妻子。
格奈乌斯·科涅利乌斯(Gnaeus Cornelius):庞培的亲戚,在公元4年谋逆。
科尔尼非奇乌斯(Cornificius):屋大维军中的将领,曾经参与西西里的战事。
李奇尼乌斯·克拉苏(Licinius Crassus):著名政治人物。他曾与斯巴达克斯交战,后来与恺撒、庞培结盟。在公元前53年死于卡莱之战。
李奇尼乌斯·克拉苏(Licinius Crassus):著名将领,在马其顿战事中功绩卓著。
迪奇穆斯·布鲁图斯(Decimus Brutus):行刺恺撒者。后来领导共和派军队与安东尼作战,一度被围困于穆提纳。
普布利乌斯·科涅利乌斯·多拉贝拉(Publius Cornelius Dolabella):公元前44年的执政官,马克·安东尼的盟友。
德鲁苏斯(Drusus):莉薇娅之子,提比略的弟弟。
伊格纳提乌斯·鲁弗斯(Egnatius Rufus):深受平民拥戴的政治家,据说密谋对奥古斯都不利。
富尔维娅(Fulvia):克洛狄乌斯之妻,后改嫁于马克·安东尼。
伽比尼乌斯(Gabinius):共和派叙利亚总督,曾出手干涉埃及的王室争端。
盖乌斯·恺撒(Gaius Caesar):奥古斯都的外孙(后来被他收为养子),阿格里帕与尤莉亚之子。
科涅利乌斯·伽卢斯(Cornelius Gallus):埃及的第一任总督,著名诗人。在公元前1世纪20年代初与奥古斯都失和,后来自杀。
日耳曼尼库斯(Germanicus):德鲁苏斯的长子,阿格里皮娜的丈夫,提比略的养子。曾在潘诺尼亚和日耳曼尼亚作战。
盖约·塞姆普罗尼乌斯·格拉古(Gaius Sempronius Gracchus):提比略·格拉古的弟弟。在公元前123年和公元前122年担任保民官,着手展开改革。
提比略·塞姆普罗尼乌斯·格拉古(Tiberius Sempronius Gracchus):改革家,保民官。在公元前133年遇害。
塞姆普罗尼乌斯·格拉古(Sempronius Gracchus):据说为大尤莉亚的情人,提比略的敌人。
希律(Herod):统治犹地亚的国王,其任命者为安东尼。后来,屋大维保留了他的王位。
奥卢斯·希尔提乌斯(Aulus Hirtius):公元前43年的执政官。在穆提纳之战中领兵作战。
尤莉亚(Julia,1):马略之妻,尤里乌斯·恺撒的姑母。
尤莉亚(Julia,2):奥古斯都之女。
尤莉亚(Julia,3):尤莉亚与阿格里帕之女,奥古斯都的外孙女。
盖乌斯·尤里乌斯·恺撒(Gaius Julius Caesar):在内战中击败了庞培。独裁官。在公元前44年3月于罗马城内遇刺。
尤妮亚(Junia):布鲁图斯的姐妹。大约在公元前30年涉嫌谋逆。
昆图斯·拉比恩努斯(Quintus Labienus):布鲁图斯和卡西乌斯的支持者。后来逃亡至帕提亚,并且在帕提亚人的支持下与安东尼交战。
马尔库斯·埃米利乌斯·李必达(Marcus Aemilius Lepidus,1):公元前78年的执政官。他发起了对抗苏拉派的叛乱,遭到了庞培的镇压。
马尔库斯·埃米利乌斯·李必达(Marcus Aemilius Lepidus,2):三头之一。
马尔库斯·埃米利乌斯·李必达(Marcus Aemilius Lepidus,3):三头之一的李必达的儿子。在公元前30年消失。
莉薇娅·德鲁茜拉(Livia Drusilla):奥古斯都之妻,提比略和德鲁苏斯之母。
李维乌斯·德鲁苏斯(Livius Drusus):公元前122年的保民官,盖约·格拉古的竞争对手。
卢奇乌斯·恺撒(Lucius Caesar):奥古斯都的外孙(后来被他收为养子),阿格里帕与尤莉亚之子。
麦奇纳斯(Maecenas):屋大维的政治顾问,奥古斯都政权高层的一员。
克劳狄乌斯·马尔凯卢斯(Claudius Marcellus):奥克塔维娅之子,奥古斯都的外甥,尤莉亚(奥古斯都之女)的丈夫。由此成了著名的政治人物,但在公元前23年英年早逝。
盖乌斯·马略(Gaius Marius):公元前2世纪末崛起的著名将领。他和科涅利乌斯·苏拉展开了内战。
米诺多洛斯(Menodoros):塞克斯图斯·庞培麾下的舰队统帅,后来投靠了屋大维。
提图斯·阿尼乌斯·米洛(Titus Annius Milo):与克洛狄乌斯作对的政治人物。他最终杀死了克洛狄乌斯。
莫奈西斯(Monaeses):投靠了安东尼的帕提亚贵族。
卢奇乌斯·提兰提乌斯·瓦罗·穆雷纳(Lucius Terentius Varro Murena):据说在公元前22年谋逆。他和奥古斯都政权的高层人物有着很近的关系。
安东尼乌斯·穆萨(Antonius Musa):奥古斯都的医生。
奥克塔维娅(Octavia):奥古斯都的姐姐,一度是安东尼的妻子,马尔凯卢斯之母。
马尔库斯·奥克塔维乌斯(Marcus Octavius):保民官。曾经威胁要以否决权阻碍提比略·格拉古出台土地法,并且因此遭到了罢免。
卢奇乌斯·欧皮密乌斯(Lucius Opimius):公元前122年的保民官。他带领着元老们一起和盖约·格拉古作对。
奥维德(Ovid):奥古斯都时代后期的诗人,以其爱情诗著称于世。晚年遭到流放。
帕科鲁斯(Pacorus):帕提亚王子。曾领军与安东尼作战。
维比乌斯·潘萨(Vibius Pansa):公元前43年的执政官。在穆提纳之战中带领共和派部队参战。
昆图斯·裴迪乌斯(Quintus Pedius):屋大维的朋友与亲戚。在公元前43年末当选执政官。
普拉提斯(Phraates):帕提亚国王。
穆纳提乌斯·普朗库斯(Munatius Plancus):恺撒旧部,但是在屋大维进军罗马之前一直支持着共和派。
格奈乌斯·庞培·玛格努斯(Gnaeus Pompeius Magnus,伟大的庞培Pompey):晚期共和国的著名将领,在内战中被恺撒击败。
塞克斯图斯·庞培(Sextus Pompeius):伟大的庞培之子。他以西西里为基地,和屋大维等人对抗。
阿西尼乌斯·波利奥(Asinius Pollio):将军,安东尼的朋友。
马尔库斯·普里穆斯(Marcus Primus):将军。在色雷斯建立了战功,但在回到罗马以后遭到了起诉。他引发了凯皮奥和穆雷纳的阴谋事件。
盖乌斯·普罗库莱乌斯(Gaius Proculeius):屋大维的朋友。曾经和他一同前去亚历山大。在帝国时代早期地位显赫。提兰提娅(麦奇纳斯之妻)和卢奇乌斯·提兰提乌斯·瓦罗·穆雷纳的兄弟。
普罗佩提乌斯(Propertius):诗人。著有四卷挽歌集,其中许多都与爱情有关。
萨卢斯提乌斯(Sallust):共和国晚期的拉丁史家。
萨尔维迪伊努斯·鲁弗斯(Salvidienus Rufus):支持三头同盟的将军,在佩鲁西亚战争后遭到处决。
萨图尔尼努斯(Saturninus):公元前100年的保民官,遭到了马略的打压。
盖乌斯·森提乌斯·萨图尔尼努斯(Gaius Sentius Saturninus):公元前19年的执政官。他与伊格纳提乌斯·鲁弗斯不和。
西庇阿·纳西卡(Scipio Nasica):元老,最高祭司,提比略·格拉古的反对者的领导人。
斯克里波尼娅(Scribonia):屋大维之妻,尤莉亚之母。
塞多留(Sertorius):马略派将领。在公元前1世纪70年代于西班牙发起了一场叛乱。
斯巴达克斯(Spartacusius):来自色雷斯的角斗士,领导了一场奴隶起义。
科涅利乌斯·苏拉·菲利克斯(Cornelius Sulla Felix):将军,独裁官。在公元前88年发动了政变,打响了内战,并且取得胜利。
普布利乌斯·苏尔皮齐乌斯·鲁弗斯(Publius Sulpicius Rufus):保民官。与苏拉相争,导致苏拉第一次进军罗马。
提兰提娅(Terentia):麦奇纳斯之妻,奥古斯都的情人。
提比略(Tiberius):第二任罗马皇帝,莉薇娅之子。
提里达提斯(Tiridates):帕提亚王位的竞争者。
瓦列里乌斯·拉尔古斯(Valerius Largus):奥古斯都时代早期的告密者。
昆克提里乌斯·瓦卢斯(Quinctilius Varus):日耳曼尼亚总督。他遭遇了一场严重的叛乱,并且大败。
普布利乌斯·文提迪乌斯(Publius Ventidius):安东尼之友。在公元前43年代表安东尼召集了部队,后来曾经在东方为安东尼作战。
马尔库斯·维尼奇乌斯(Marcus Vinicius):公元前19年的执政官,奥古斯都的近友,著名将领。
维普萨尼娅(Vipsania):阿格里帕之女,提比略之妻。
维吉尔(Virgil):奥古斯都时代的诗人,《农事诗》(Georgica)、《牧歌集》、《埃涅阿斯纪》的作者。